The White House says Section 702 is critical for cybersecurity, yet public evidence is sparse

Since the Biden administration came out in favor of reauthorizing Section 702 of the Foreign Intelligence Surveillance Act in February, the intelligence community has pointed to the growing threat of foreign cyberattacks on the U.S. as a key argument in favor of the controversial surveillance tool.
Officials have made broad and general declarations, pointing to wide-ranging applications that include thwarting multiple ransomware attacks against U.S. critical infrastructure, finding out a foreign adversary had hacked sensitive information related to the American military and uncovering a cyberattack against critical federal systems.
Yet, 15 years into Section 702’s history, declassified examples of thwarting cyberattacks are sparse. In the little over three months that the Biden administration has been publicly advocating for the renewal of Section 702, it hasn’t mentioned a single specific public incident where Section 702 was used, despite a term marked by both ample cyber attacks and well-publicized takedowns of foreign hackers.
That lack of transparency and specificity doesn’t appear to be helping the Biden administration in what will likely be an uphill battle for Congress to reauthorize the authority before it sunsets in December. Even some of the authority’s greatest supporters have expressed frustration.
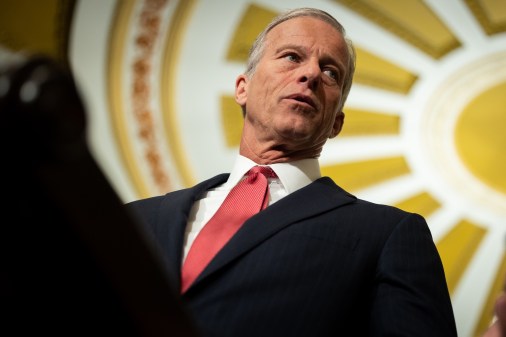
“Whether it’s helping to identify victims so they can be notified of the attack or helping to identify ransomware actors, 702 has been invaluable over the past several years,” Sen. Mark Warner, D-Va., told CyberScoop in an email. “However, I am frustrated that more of these compelling examples have not yet been made public.”
Warner’s office confirmed that the intelligence community has shared examples of the tool’s cyber significance in classified settings but declined to elaborate.
“While it’s important that we do not risk sources and methods, it is also critical that we explain to the American people what will be lost and how they would be increasingly vulnerable to cybercriminals and foreign governments if this authority were allowed to expire,” the Senate Intelligence chairman wrote.
Adam Hickey, former assistant attorney general of the Justice Department’s national security division, echoed Warner’s concerns. “I think they’re fighting with one hand behind their back,” said Hickey, now a partner at the law firm Mayer Brown. “On the one hand, you don’t want the very people who pose a threat to understand your capabilities, because they will work around them … On the other hand, you don’t want to be so careful to avoid that risk that you lose the very authority itself.”
The reticence also isn’t helping the civil liberties community, either, who have challenged the intelligence community’s persistent claims that any reforms to Section 702 that slow down investigators would imperil America’s national security.
“If that’s what the FBI is going to say — not only is it useful for cyber, but it’s useful in this preventive way, this very rapid way — I think this claim needs to be able to be backed up with some examples,” said Jake Laperruque, deputy director at the Security and Surveillance Project for the Center For Democracy & Technology.
Section 702 was first passed in 2008 as an amendment to FISA, pitched initially as a key tool in America’s fight against terrorism. The authority allows the U.S. government to collect the U.S.-based communications of non-Americans outside the country. The collection of the data of U.S. citizens using Section 702 is prohibited, but such data is often swept up in the surveillance in “incidental collection.” This data can be searched by the FBI under certain statutory requirements.
While the amount of FBI searches of 702 data has fluctuated over time, the amount of those searches related to cybersecurity has steadily increased. In a recent interview with CyberScoop, a senior FBI adviser confirmed that “about half” or a “plurality” of Section 702 database searches made by the agency today relate to the investigation of malicious, state-sponsored cyber attacks. While the adviser couldn’t say how much of an increase that was from previous years, they said it was reflective of an overall shift in the agency’s work toward more cyber investigations.
“Our use of the authority in the FBI and across the intelligence community is weighted a lot more heavily towards cyber now than it was five years ago,” the senior FBI adviser said. “Part of that use of this authority is reflective of its value, and the fact that we are just doing more work in this field and we’re seeing cyber threats increase over time.”
While the FBI adviser couldn’t share any specific examples, there is some limited data about how Section 702 data has shown up in cyber investigations. For instance, in its 2022 annual transparency report the ODNI wrote that of the 3.4 million searches made by the FBI in 2021, nearly two million were related to an investigation into an alleged attempt by Russian hackers to break into critical infrastructure. The searches helped to identify potential victims, officials said at the time.
The number of FBI searches declined dramatically in 2022, in part due to a new methodology used by the FBI to count searches.
“Cyberattacks happen at a larger scale. And therefore, the amount of information collected and queried on cyber attacks is just proportionately larger,” said Tom Bossert, the former United State Homeland Security adviser under the Trump administration. “You can imagine hundreds of thousands of attempted cyber attacks in any given period of time, and perhaps only five terrorist phone calls in that same period.”
In its early days, Section 702 was branded as a powerful counter-terrorism tool, reflecting the intelligence community’s focus at the time. In fact, some of the program’s biggest declassified successes involve foiling terrorist plots and taking down their leaders. Most recently, last summer Section 702 intelligence led to a successful operation against al-Qaeda leader Ayman al-Zawahiri.
It was only in 2017 amidst the last renewal debate that cybersecurity began to take a more leading role, with examples of thwarted ransomware attempts eclipsing references to ISIS and other terrorist cells. Now, it often takes top billing when discussing the threats that nation-states pose to the homeland. In its 2023 annual threats assessment, the Office of the Director of National Intelligence put China, Russia, North Korea and Iran and their cyber capabilities among the leading threats to the nation.
Bossert, who was in charge of the Trump administration’s efforts to secure a reauthorization in 2017, sees the new strategy in part as reflective of the national security community’s shifting focus. “I think a lot of people will perceive the cyber threat to be real and ever-present. And fewer people find the terrorist threat to be as urgent,” he said. “And I’d like to think that’s because we’ve spent 20 years confronting that problem and putting controls in place.”
Officials say part of the reason Section 702 has become so valuable in thwarting foreign actors is the complicated nature of cyberattacks. In the majority of cases, attackers use U.S. infrastructure as a lily pad into domestic targets. Intelligence officials have often pointed to this as a challenge when trying to follow the activity of foreign actors onto domestic soil, noting it as a “blind spot” that contributed to the failure to detect Russian hackers during the SolarWinds attack.
Section 702, they say, fills restores that visibility. “It is an authority that lets us do collection against a known foreign entity who chooses to use U.S. infrastructure,” NSA director of cybersecurity Rob Joyce told a crowd at the RSA Conference in April. “And so it makes sure that we don’t afford the same protections to those foreign malicious actors who are on our infrastructure as we do the Americans who live here.”
“I can’t do cybersecurity at the scope and scale we do it today without that authority,” he added.
The FBI and NSA aren’t alone in praising the tool. This week a senior state department official spoke about how the tool is instrumental in informing the work of U.S. diplomats, including cybersecurity issues such as North Korean IT fraud.
One potential stakeholder the Biden administration has yet to seriously court in the fight to renew Section 702 is industry. The senior FBI adviser stressed how failure to renew the authority would hurt its ability to advise chief information security officers, inundated with warnings about vulnerabilities, about which specific threats are most urgent.
“This is one of those things that lets us reach out to specific sectors and even specific companies to say, look, this specific vulnerability is one you want to take care of right now because we’re seeing certain types of actors targeting companies, companies like you, using that,” the senior FBI adviser said. “We’re going to have a severely constricted optic in all those things if we’re forced to rely solely on other tools.”
Former general counsel of the National Security Agency Stewart Baker has made the case that the intelligence community should do more to demonstrate to industry how they can benefit from Section 702. “If I were a CISO, I’d want to weigh in on the kinds of warnings, the kinds of uses of this intelligence in real-time, that would be particularly useful to me.”
Businesses need to understand that if Section 702 goes away, so does that intelligence, says Bossert. “They shouldn’t just think of this as a national security threat. They should think of this as an enterprise threat to their company. And they should view the US government as a potential partner,” he said. “If they expect the US government to continue to be a reliable partner…they have to understand that the underlying information that they have to share is in the government’s holdings because of authorities like 702.”
The senior FBI adviser told CyberScoop that the agency is looking at ways to increase industry engagement on the subject. “There’s a variety of different stakeholders here. And industry, particularly when we’re talking about cyber, is a very important one,” the senior FBI adviser said “So that is something that we are going to take a look at going forward about how we can start getting them engaged now that this is really starting to bubble up to the top of the public conversation as well as the conversation on Capitol Hill and in other stakeholder constituencies.”
Even if there were more examples, it’s unclear if Section 702’s purported value in preventing these attacks can overcome the program’s many criticisms, both from lawmakers wielding the power to reauthorize it and civil liberties groups seeking to reform the program. Most of the political pushback against the authority centers around concerns about well-documented abuses of America’s civil liberties, public examples of which have nothing to do with ransomware or foreign actors infiltrating critical infrastructure.
For instance, a recently declassified 2022 U.S. court ruling found that the FBI had improperly searched for information on Americans in the FISA database 278,000 times, including to spy on political campaigns and protesters. The report sparked outrage from both leading Democrats and Republicans who insist that the program can’t be reauthorized without reforms.
(The FBI argues that it has implemented new compliance measures since those searches occurred to cut down on misuse.)
Officials advocating for Section 702’s reauthorization have been vague about what reforms they would be willing to discuss, instead emphasizing that changes should not diminish the tool’s effectiveness. The reforms sought by advocates and lawmakers may do just that, at least in the eyes of the intelligence community. For instance, the senior FBI adviser said a warrant requirement, one of the top asks from reformers, would make it difficult for the agency to act swiftly to notify ransomware victims.
CDT’s Laperruque noted that courts have long recognized emergency exceptions to the warrant process. Reforms such as adding a warrant requirement to Section 702, which CDT and other groups are advocating for, wouldn’t change that.
“That’s not going to stop Section 702 from being used for cyber,” said Laperruque. “It’s going to stop 702 from being used on Black Lives Matter and members of Congress, which is what we’ve seen 702 used for in recent years.”