Hacking group has hit Taiwan’s prized semiconductor industry, Taiwanese firm says
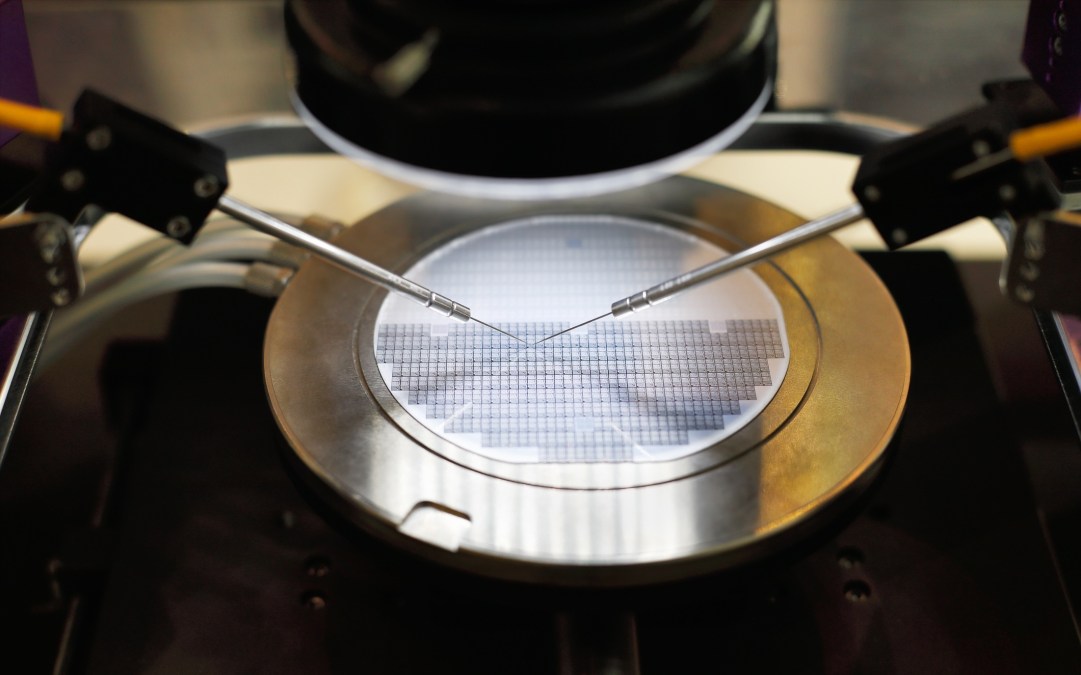
Taiwan’s semiconductor industry, a centerpiece of the global supply chain for smartphones and computing equipment, was the focus of a hacking campaign targeting corporate data over the last two years, Taiwan-based security firm CyCraft Technology claimed Thursday.
The hackers went after at least seven vendors in the semiconductor industry in 2018 and 2019, quietly scouring networks for source code and chip-related software, CyCraft said. Analysts say the campaign, which reportedly hit a sprawling campus of computing firms in northwest Taiwan, shows how the tech sector’s most prized data is sought out by well-resourced hacking groups.
“They’re choosing the victims very precisely,” C.K. Chen, senior researcher at CyCraft, said of the hackers. “They attack the top vendor in a market segment, and then attack their subsidiaries, their competitors, their partners and their supply chain vendors.”
It was unclear which companies were targeted; CyCraft declined to name them. It was also unclear who was responsible for the hacking. CyCraft said there were signs the group of attackers was based in China, including their familiarity with simplified Chinese characters and the breaks they took during Chinese national holidays. CyberScoop could not independently confirm that a Chinese group was responsible for the hacking.
Taiwan is home to multiple companies with clout in the semiconductor industry. Chief among them is the Taiwan Semiconductor Manufacturing Company (TSMC), which accounted for half of global revenue last year in foundries, a predominant manufacturing model in the industry. In May, the Trump administration dealt a blow to Chinese telecom supplier Huawei by effectively blocking the sale of TSMC semiconductors to Huawei’s chip developers.
“Most of the world’s brand-name semiconductors we know [make] their chips in Taiwan,” said Scott Kennedy, senior adviser at the Center for Strategic and International Studies, a think tank. Give the value of the data, he added, “the Taiwanese go to tremendous lengths – as does the entire semiconductor industry — to protect their IP and trade secrets.”
China, meanwhile, is trying to turn itself into a powerhouse for semiconductor production. Beijing aimed to produce 70% of the semiconductors it uses by 2020, though it appears to be falling well short of that mark.
VPNs open the door
The hackers broke into some of the corporate networks by exploiting virtual private networking software, CyCraft said. The attackers then altered a software authentication program and planted malicious code that allowed them to access other machines on the network. “Based on the stolen data, we infer that the actor’s goal was to harvest company trade secrets,” CyCraft wrote in a report they are presenting Thursday at the 2020 Black Hat security conference.
Independent analysts who track China-related hacking activity said they had not observed and verified the particular attacks described by CyCraft. (The Taiwanese firm said it had conducted incident response on site, and that it plans to release more technical data.) But the hacking would not be the first time that the semiconductor industry has been targeted.
“We have no reason to doubt this research, but can’t independently confirm it,” said Ben Read, senior manager of analysis at Mandiant Threat Intelligence. “We’ve seen multiple instances of Chinese groups targeting the semiconductor industry, going back years. We’ve also seen Chinese groups use Cobalt Strike, but that information alone isn’t enough for us to confirm the sponsorship.”
Mike McLellan, who tracks China-related hacking groups at Dell Secureworks said his team had not attributed the activity described by CyCraft to a specific group. But the techniques described, he said, “are consistent with intrusion activity [our] researchers have seen elsewhere, and that were attributed to China-based threat groups.”