Suspected Chinese hackers target telecoms, research in Taiwan, Recorded Future says
A suspected Chinese state-sponsored group is targeting telecommunications organizations in Taiwan, Nepal and the Philippines, researchers at Recorded Future’s Insikt Group said in a report Thursday.
Researchers noticed intrusions from the group, which investigators called TAG-22, in June targeting telecommunications organizations including the Industrial Technology Research Institute in Taiwan, Nepal Telecom and the Department of Information and Communications Technology in the Philippines. Some of the activity appears to be ongoing as of press time, researchers said.
The new findings play into a larger backdrop of apparent Chinese hackers snooping on global competition in the telecommunications space, which has become an arena of political and economic conflict between China and the United States.
“In particular, the targeting of the ITRI is notable due to its role as a technology research and development institution that has set up and incubated multiple Taiwanese technology firms,” researchers wrote. They noted that the organization is focused on technology and sustainability projects that align with Chinese development interests.
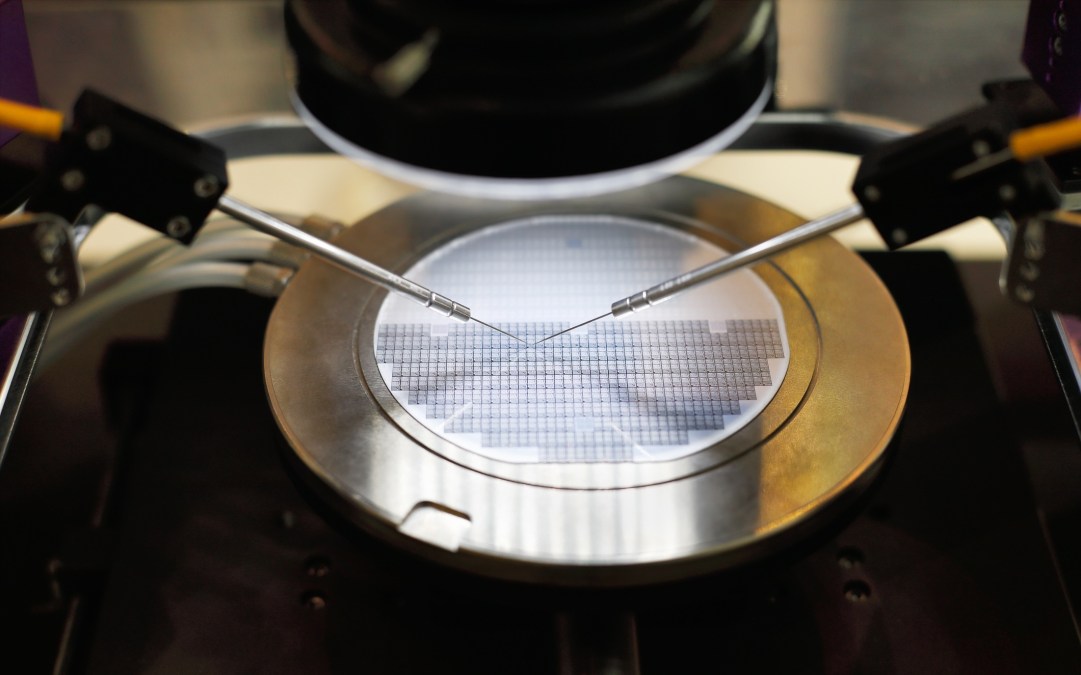
“In recent years, Chinese groups have targeted multiple organizations across Taiwan’s semiconductor industry to obtain source code, software development kits, and chip designs,” researchers added.
Cybersecurity firm CyCraft claimed last year that Taiwan’s semiconductor industry was the focus of a major two-year hacking effort likely perpetrated by actors based in China. The telecommunication sector was among the sectors most targeted by Chinese hackers in the first half of 2020, according to a report from CrowdStrike last year.
Outside of the telecommunication industry, the threat group has targeted academia, research and development, and government organizations in Nepal, the Philippines, Taiwan and less recently Hong Kong.
The threat group appears to use backdoors used by other Chinese state-sponsored groups, including Winnti Group and ShadowPad. It also employs open-source security tools like Cobalt Strike.
While researchers primarily identified the group as operating in Asia, its scope of targets is generally broader, they said. That puts it in line with other major Chinese hacking groups including APT17 and APT41, researchers noted.






