Researchers found a semi-legit way to turn an Amazon Echo into a wiretap
An Amazon Echo application created by security researchers proves how the popular smart home device can be co-opted to remotely listen to people’s nearby conversations, according to cybersecurity firm CheckMarx.
The research describes how an inherent design flaw in the Amazon Echo could be exploited to covertly and remotely launch the Alexa voice assistant on compromised devices. Alexa was engineered to be able to record and react to voice commands within a predetermined distance from the device.
During their controlled experiment, CheckMarx researchers disguised a malicious Echo skill by marketing it as a voice-enabled calculator application that leverages Alexa to execute certain commands.
“It can be done totally remotely,” said Erez Yalon, manager of application security research at Checkmarx. “While a hacker creates a malicious skill and publish it to the Amazon store, every user that will use this Amazon skill is exposed.”
CheckMarx says the trick didn’t “break or hack anything,” since the calculator app functioned normally aside from a few hidden tools which were actively manipulating Alexa. The manipulations allowed researchers to consistently collect recordings.
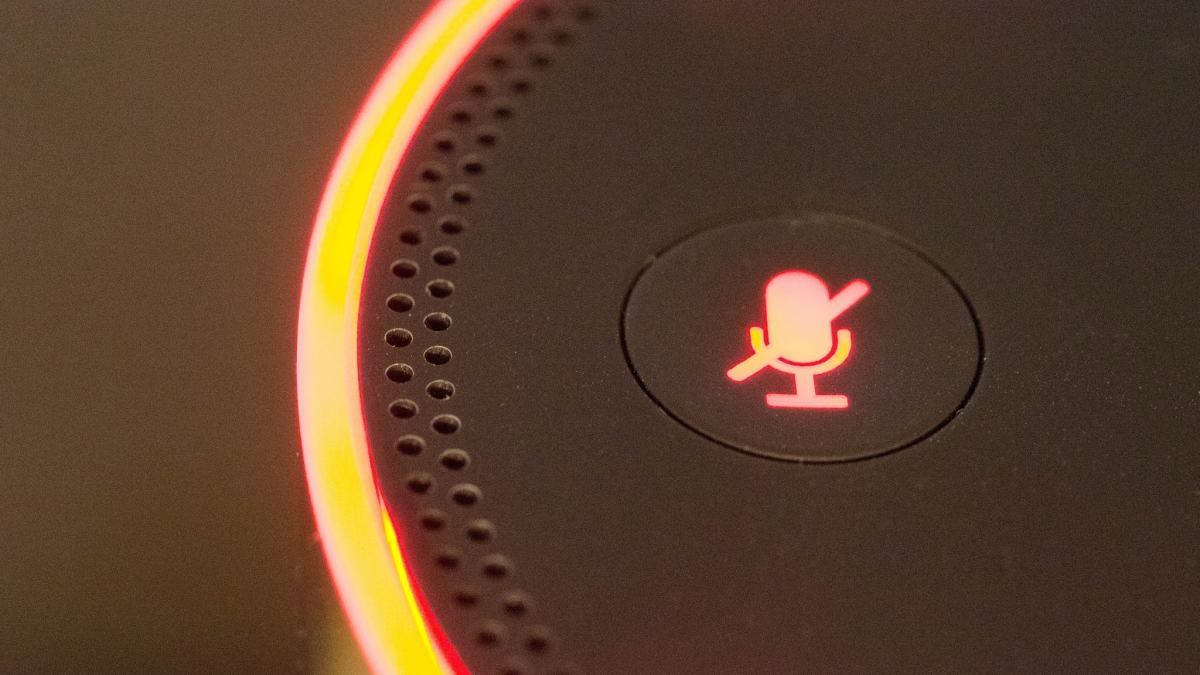
While Alexa is supposed to be responsive, it’s not always listening for a voice command. A small blue ring light indicates when it is ready to react. The calculator skill caused the light to always be on.
CheckMarx researchers found a way to fool the voice assistant by adding a snippet of new code in the developer API for the calculator app. By doing this, they were able to make sure that the Echo stayed on and was listening at all times. With that capability set, all the researchers had to do was introduce a basic transcription script and then configure the software to send records back to the attacker’s computer.
“Part of the regular process of the skills is that relevant words for the skill are recognized and used by the skill,” explained Yalon. “We created a ‘catch-all’ customized word slots that are transcribed and sent to the attacker.”
In a real world scenario, the booby-trapped application would first need to be voluntarily downloaded by the end-user and then activated. Within Alexa’s software ecosystem, applications are named “skills.” There is a skills “store” where people can go download both free and paid content for their own Amazon devices, which are submitted by developers to the tech company.
Google has been fighting against a similar type of issue in the Google Play Store for years. Prior reporting by CyberScoop has shown that while a screening process is in place for the marketplace, it has let spyware and other malware be hosted for download. Amazon has yet to face the same sort of pressure or scrutiny as Google, but CheckMarx’s research makes it clear that the threat exists.
CheckMarx reported the issue directly to Amazon prior to publishing their research and the company has already taken action to create a fix. An update makes it so the device will warn the user if Alexa is continuously active.