Congressional commission mulls new private sector reporting requirements

The Cyberspace Solarium Commission, a bipartisan group tasked last year with devising a strategy for defending the U.S. against cyberattacks, is almost ready to reveal its proposals to the world.
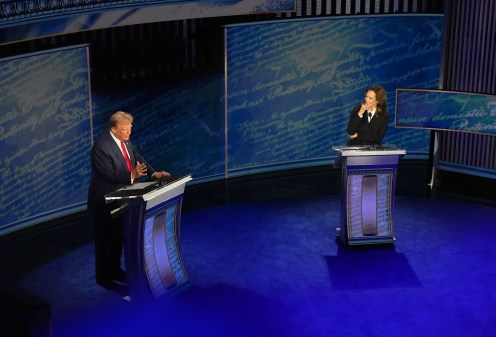
The commission’s final report, expected to be issued in March or April, may include new reporting requirements for the private sector that would incentivize better security practices, the commission’s co-chairs, Sen. Angus King, I-Maine, and Rep. Mike Gallagher, R-Wis., said Tuesday during a Council on Foreign Relations summit in Washington, D.C.
While the final language is unclear, the report is expected to include a sweeping set of proposals ranging from an overhaul of congressional oversight on cybersecurity issues to an assessment of the Pentagon’s offensive and defensive readiness. Whether there’s broader appetite outside of the 14-member commission to implement the recommendations, however, remains to be seen.
One idea the commission has entertained is convincing insurance companies to offer better rates to clients who follow specific guidelines meant to bolster their cybersecurity, King said. Insurance companies already are incentivizing clients to work with cybersecurity vendors considered more likely to stop data breaches, as CyberScoop has reported.
“How do we ensure they are at some minimal level of cybersecurity?” King said. “The insurance company will say to the company if you do these things your rate will be ‘x,’ if you don’t do these things it will be ‘2x.’”
The commission also has considered reporting requirements that would encourage companies to decrease the time it takes them to detect, evaluate, and remediate possible network intrusions.
The so-called 1:10:60 rule has been helpful in debating possible requirements, Gallagher said. That rule encourages firms to detect intrusions in one minute, have an analyst evaluate it in 10 minutes, and remediate it within 60 minutes. Meeting this benchmark, according to CrowdStrike data, would eradicate most hackers before they’re able to move beyond their initial entry point.
“You can imagine a world in which we require regulated companies or critical infrastructure to collect 1:10:60 data or something similar,” Gallagher said.
The focus of any such proposal would be to hold companies accountable in case of a breach, Gallagher said.
How the exact proposal on reporting detection and remediation might be adopted, however, is still being debated. In the meantime, Gallagher noted, the federal government could improve its own internal reporting, perhaps by sending Congress quarterly updates about agencies’ detection and remediation times.
Changing behavior in Washington, too
The Solarium’s report may present Congress with some structural proposals that could enhance its oversight of cybersecurity issues, the co-chairs said.
The commission is unanimous that Congress needs to change how it conducts cybersecurity oversight, according to King, and the Solarium report may present lawmakers with proposals on how to expands their visibility into cybersecurity gaps. One way to do that could be to create a select committee to oversee cybersecurity issues, he said.
For now, it seems, many of the commission’s proposals will be focused on “enhancing” the role of the Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA). Hiring initiatives may be a priority, Gallagher suggested.
Recommendations for the White House could make an appearance in the final report as well.
“There is near unanimity on the need to get a focal point in the White House to do oversight of the cyber community,” Gallagher said.
The White House cybersecurity coordinator, a role that then-national security adviser John Bolton eliminated in 2018, has not resurfaced despite Bolton’s departure.
The commission also will mandate the Pentagon conduct internal assessments of the operational capacity of different cyber personnel in the Department of Defense. Such a change could provide insight on how U.S. Cyber Command personnel, for example, are functioning under a new Pentagon strategy of being more aggressive in cyberspace, known as “defending forward,” according to Gallagher.
The commission has also been debating how hiring can and should be different for cybersecurity posts at the Pentagon.
“Do you need a cyberwarrior to do 100 pushups? We don’t want to lower the standards of the military, but we need to be able to tailor the requirements to the job,” King said.