Cyber Command has redeployed overseas in effort to protect 2020 elections
U.S. Cyber Command is still working overseas with allies to try preventing election interference, Brig. Gen. Timothy Haugh, the commander of Cyber Command’s cyber national mission force said Tuesday.
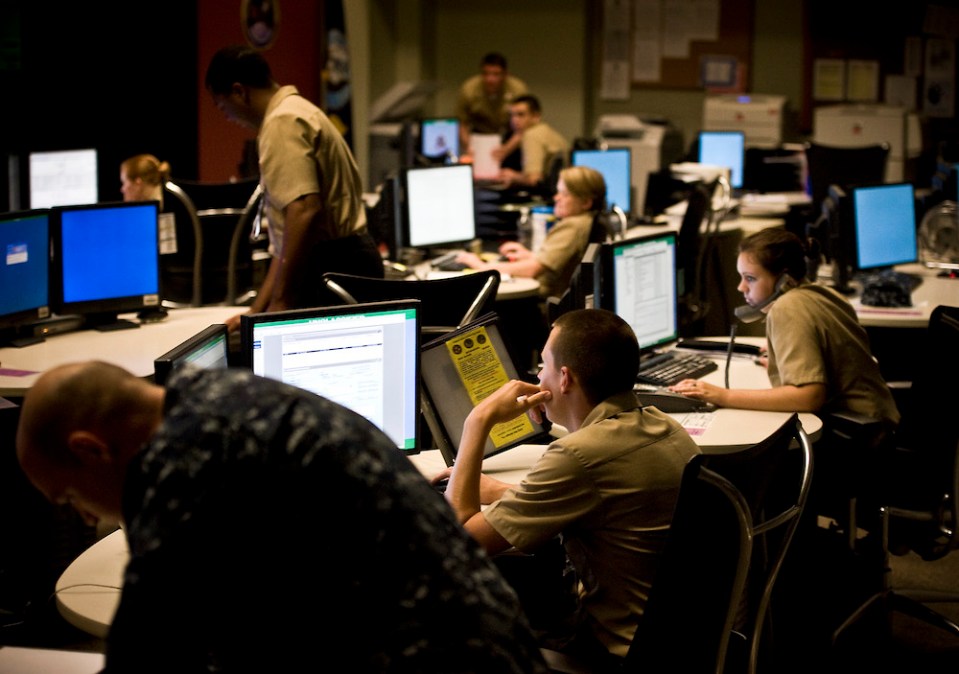
As part of the military’s operation to defend the U.S. midterm elections in 2018, an operation known internally in the Department of Defense as “Synthetic Theology,” Cyber Command deployed cyberwarriors to Ukraine, North Macedonia, and Montenegro to help defend those countries’ networks, and to collect intelligence on adversaries. Cyber Command has since “redeployed” out of “some of those” countries, Haugh said during a reporters’ roundtable at the Integrated Cyber Center and Joint Operations Center in Fort Meade, Maryland.
Haugh did not specify in which countries Cyber Command has ongoing operations right now in preparation for 2020, but said these kinds of partnerships will continue to grow.
“When we look to do partnerships overseas … we want to do that anywhere where there’s a potential adversary that would also target our electoral systems,” Haugh said.
The effort is meant to complicate possible election interference originating in countries like Russia, which the U.S. intelligence community has determined sought to interfere in the 2016 presidential election. Investigators also found that hackers infiltrated state election infrastructure ahead of last year’s midterm elections, and a steady stream of account takedowns have demonstrated how suspected government propagandists still are using social media to manipulate public opinion. By working with the countries affected by this problem now, the logic goes, Cyber Command can gain an insight into what the U.S. might expect next year.
“We recognize and understand the importance of being in constant contact with the enemy in this space especially below the level of armed conflict so we can defend ourselves and we can impose costs,” said Maj. Gen. Charles Moore, Cyber Command’s director of operations.
Haugh told reporters he felt Cyber Command “did a good job” in the operations the command has launched in years past to counter adversaries in their attempts to meddle in U.S. elections.
It is only in recent years that Cyber Command has been able to defend against adversaries overseas.
Haugh credited the National Defense Authorization Act of 2019 for some of Cyber Command’s successes in protecting U.S. elections in that it freed up the command to move off the Department of Defense networks to defend the U.S. from outposts overseas.
“That allowed us to gain insights in a way we hadn’t in years past,” Haugh said. As a result, “defensive missions that we did overseas were clearly intended for us to be able to gain insights into how adversaries operate in areas that we believe that, in this case, one of the NDS [National Defense Strategy] competitors was operating. Our approach to that was different.”
The Pentagon’s NDS of 2018 names Russia, in addition to China, as a principal priority among strategic competitors.
Prior to the new offensive authorizations, Cyber Command was “a maturing force,” Haugh said, referring to the way it handled the 2018 midterm elections. As an example of that maturing process, Haugh pointed out that in 2018 Cyber Command was still focused on building relationships between agencies to handle election interference attempts.
“We had to build new relationships, whether that was with DHS, whether that was with FBI, or our teammates in the Department of State,” Haugh said. “All of those we had to build together in a really short timeframe.”
One of the ways Russia attempted to interfere in the 2016 presidential elections included an attempt to sow discord and misinformation online through social media platforms. As part of operation Synthetic Theology in 2018, Cyber Command worked to prevent election interference by interrupting the Russian-backed Internet Research Agency’s internet access, an operation The Washington Post first reported.
This was the first publicly reported example demonstrating how Cyber Command would be “defending forward” with its new authorizations.
And yet, the National Security Agency’s David Hogue, the senior technical director of the Cybersecurity Threat Operations Center, said last month he thinks there is still much interagency work to be done to push forward the U.S.’s approach to information warfare. International governments are exploiting social media to push their own message, and divide global populations, he said.
“They’re furthering their own narrative at a very low cost,” Hogue said while speaking at a McAfee event produced by CyberScoop and FedScoop last month. “I think there’s still a lot that we’re collectively trying to understand.”
Rooting out adversaries’ information operations on social media platforms falls outside of Cyber Command’s purview, Haugh said Tuesday.
“When Gen. Nakasone and the department talk about ‘defend forward’ we’re really looking outside our borders,” Haugh said. “That type of information is probably best left for a real focus from our domestic agencies as we go forward.”
Cyber Command’s mandate is, of course, to impose costs on adversaries when directed, and in that context, Cyber Command said it will try to contribute to partners’ efforts to root out misinformation campaigns online.
“It’s an area that we want to contribute our understanding based off of what we do in our defend forward operations,” Haugh said.
One election interference effort adversaries may deploy in the buildup to 2020 elections that Haugh said Cyber Command is “unlikely” to get involved in is if an adversary makes a targeted campaign against a presidential candidate; specifically, Haugh said the command is unlikely to get involved in notifying targeted candidates of such activity. Cyber Command may be involved in providing insights related to that activity, however.
In preparation for 2020 military cybercommanders said they still want to focus on relationships between the Department of Homeland Security, FBI, State Department and Cyber Command.
“We’re at a spot where right now what we really want to be focused on is the partnerships on the interagency side,” Haugh said.
Although this was a focus two years ago, Haugh indicated he thinks Cyber Command is heading into this election cycle with better preparedness when it comes to coordinating its actions with those emanating from the FBI, DHS, and the State Department given that they have had some experience working to counter adversaries’ efforts to impact U.S. elections now.
“The work that we went through, the lessons we learned … we now benefit from that hard work in 2020,” he said. “We’re starting from a set of foundational partnerships.”
When asked if Cyber Command wants more authorities to conduct its offensive operations, Haugh said that’s not the command’s focus right now.
“Any discussion of authorities from our standpoint is premature,” Haugh said.
It is also likely that the group the NSA and Cyber Command stood up last year to counter Russian attempts at election meddling is about to receive more resources, an intelligence official told CyberScoop. The group, dubbed the Russia Small Group, was recently made permanent to prepare for a “broader challenge in the upcoming 2020 election cycle,” a spokesperson said.
Cyber Command would not comment today on the level of threats coming from Russia, China, and Iran. Cyber Command also would not comment on the number of operations it has been able to launch given its newfound authorization to operate against adversaries overseas.






