New research highlights Vietnamese group’s custom hacking tools
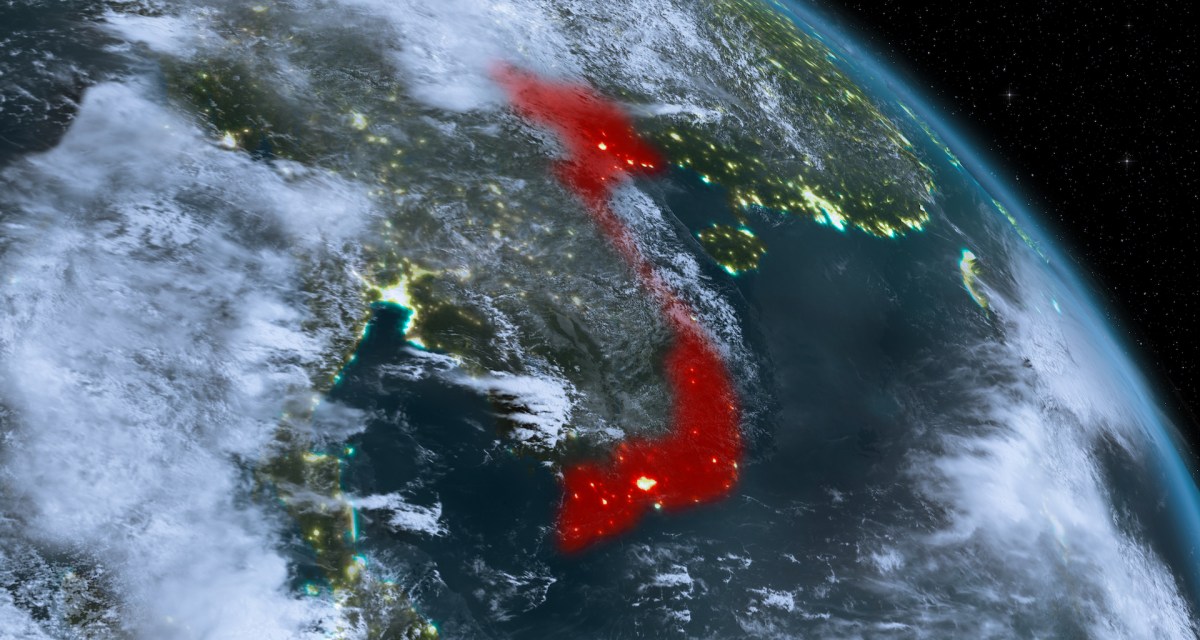
Cybersecurity researchers have uncovered remote access tools, or backdoors, linked to an infamous Vietnamese hacking group with a history of targeting government organizations and intellectual-property-rich companies.
Analysts with cybersecurity company Cylance say that while investigating a security incident last year, they found multiple custom backdoors used by the cyber-espionage outfit known as APT32 or OceanLotus Group. The hackers used command and control protocols that were tailored to their targets and that supported multiple network communication methods.
“The overall design and development of these threats indicate they come from a well-funded development team,” research from Cylance published Wednesday states. “The OceanLotus Group uses an expansive amount of custom library code that can easily be repurposed for maximum effectiveness against their next target.”
Tom Bonner, Cylance’s director of threat research, told CyberScoop that the “underlying code for the APT32 backdoors is highly modular,” meaning it can be repurposed by tweaking command and control protocols.
APT32, whose activity researchers say aligns with Vietnamese state interests, caught the attention of malware hunters last year after breaching a series of companies with business interests in Vietnam. The group has had a busy 18 months, from apparently researching a leaked National Security Agency hacking tool to stealing a transcript of a conversation between President Donald Trump and his Philippine counterpart, Rodrigo Duterte.
Nick Carr, a senior manager at FireEye who has closely tracked APT32, said that after a “brief hiatus” following his firm’s May 2017 report on the group, APT32 is “actively targeting” many of FireEye’s private-sector and government clients.
“After a late 2017 shift to the electronics and automotive industry to support Vietnam’s goals, throughout 2018 [the group] has focused more targeting on financial institutions instead of the global corporations themselves, likely to obtain foreign company investment and operations data at scale,” Carr told CyberScoop.
APT32, Carr said, continues “to develop their technical tradecraft in-house with their signature style that is all their own,” including by using broad-based web compromises to “profile and deliver payloads to specific victims.” The group is innovating rapidly, “attempting new techniques in campaigns every few weeks,” he added.
Cylance says the backdoors it discovered share some code similarities with backdoors found by FireEye and Kaspersky Lab.
The new research points to steps APT32 has taken to evade detection. The group has used obfuscating tools that allow “much of the malware to operate in-memory, with no on-disk footprint,” along with an anonymizing service known as PrivacyGuardian to register its domains, Cylance said. One of the custom remote access trojans that piqued Cylance researchers’ interest was specifically designed to imitate software libraries developed by the target organization — a move that is in keeping with the group’s stealthy tactics.






