A researcher made an elite hacking tool out of the info in the Vault 7 leak

When WikiLeaks published a cache of more than 8,000 CIA documents in 2017 detailing U.S. hacking capabilities, security experts complained that the organization had possibly produced a technical blueprint on how to recreate the government’s elite-level tools.
Wayne Ronaldson has made it a reality.
Ronaldson, who looks for corporate clients’ vulnerabilities as “red team” leader at Melbourne-based offensive security company Loop Secure, pored over many of the so-called Vault 7 documents to find the Assassin program. The CIA described Assassin as an automated implant tool capable of monitoring computers running Microsoft Windows for long periods of time without detection, sending periodic updates to its operator.
Ronaldson, using Assassin as the model for his own intelligence-gathering tool, studied the leaked CIA documents and consulted with industry friends about how to make his own cyber-espionage weapon. Next week, nearly 16 months after he began the process, Ronaldson plans to unveil Overwatch Offensive during a presentation at the 2019 RSA Conference in San Francisco. Red teams probe corporate security defenses for vulnerabilities, getting paid to detect and report holes real-world adversaries could use for their own gain.
“Being one person, I wanted to see if I could make a tool close to what the NSA or CIA and their teams of people can make,” he said. “And I wanted to use the documents from the dump to build a framework like that. Why did I want to do this? Well, because it’s awesome, and also because I’m a hacker deep down.”
Overwatch Offensive — named by Ronaldson’s son, who thought the web portal resembled the “Overwatch” video game — appears to be capable of a conducting a range of tasks on an infected machine, according to a walkthrough Ronaldson provided CyberScoop.
By clicking a dropdown box in Overwatch’s web portal, a hacker (or red teamer) could choose to collect screenshots, activate a keylogger, covertly turn on a computer’s microphone, access an individual’s scheduled appointments, and carry out more than a dozen other tasks. The tool sweeps up targeted information and sends it back to the command-and-control host at least once every 24 hours through an encrypted connection.
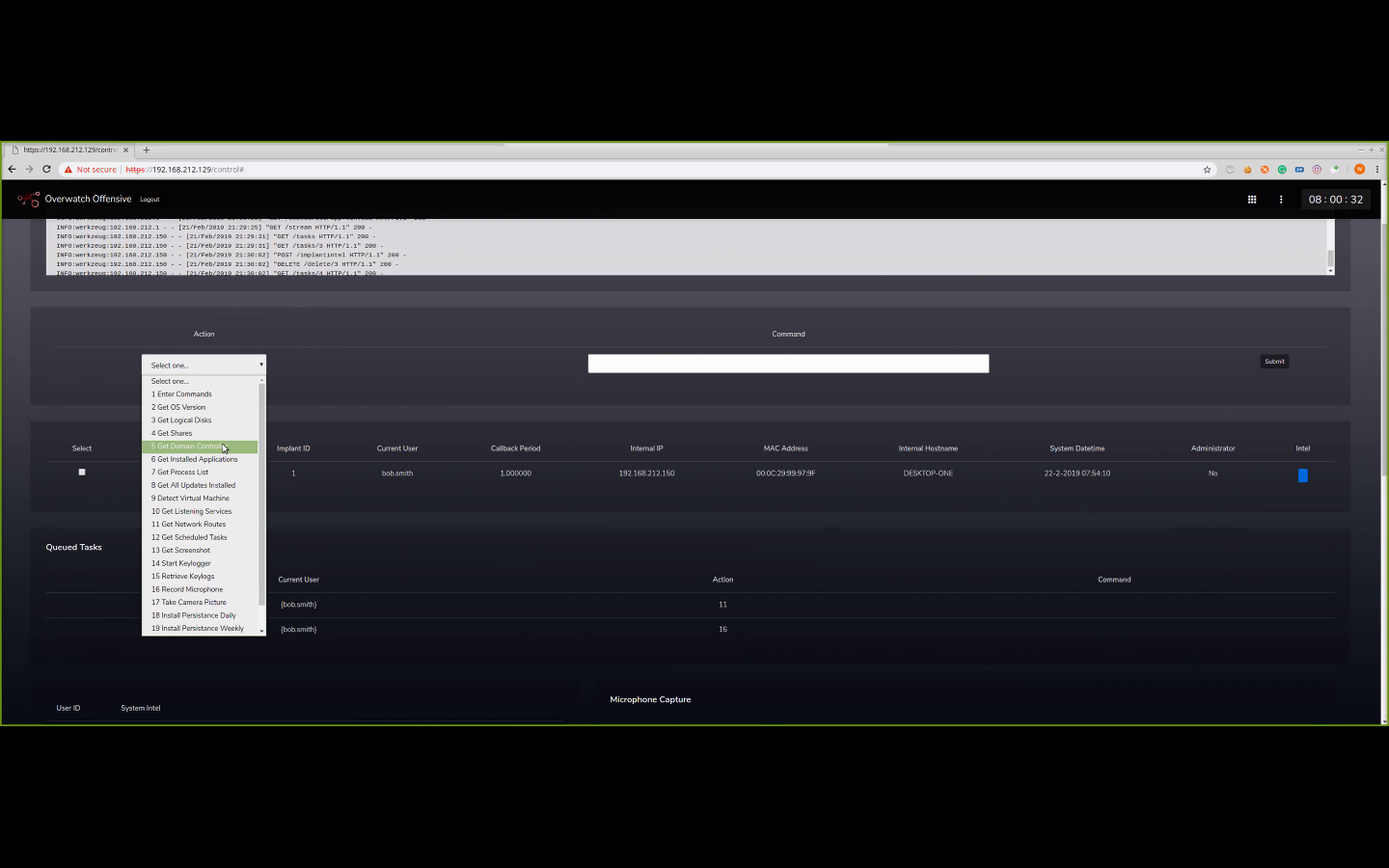
A dropdown box on the left-hand side of Overwatch Offensive’s navigation screen offers a glimpse into the tool’s capabilities (Wayne Ronaldson).
“These are all the things that Assassin or the other tools in the Vault 7 leaks would do,” Ronaldson said.
“Some of the things released in the documents were details on the antivirus providers they would test tools against,” he said. “They said Kaspersky detects a recording microphone, and they’d describe McAfee detecting keylogging in a certain way. So I would avoid doing that in mine so I wouldn’t get caught.”
Overwatch Offensive could be added to target machines either via attachment in a phishing email or physical access to the machine, he added.
“The tool is not to just hack people. It’s for the special person in a company with all the secrets,” he said. “This would just sit on their laptop.”
Ronaldson says no one else has the code to his hacking tool, and that he will protect it from going public. Few specific technical details were included in the presentation reviewed by CyberScoop, and he says the audience at RSA will witness the public debut of the tool. Ronaldson said he does not intend to make Overwatch Offensive widely available, adding that a number of tools like it already are available for red team testing.
“It was my own challenge [and] my digital Everest,” he said. “The only way it gets released is if WikiLeaks somehow releases it.”
“But if you saw it I think you’d probably say yes, it works,” he said.
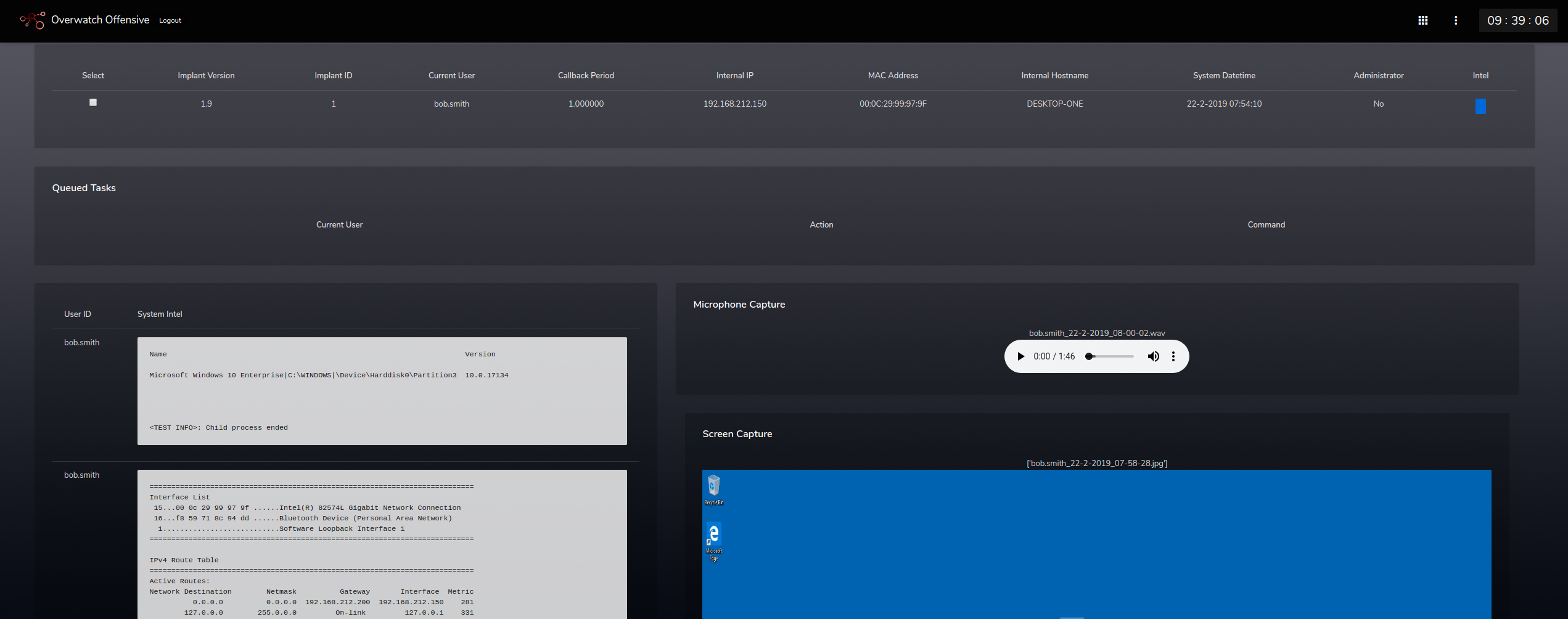
A screenshot of Overwatch Offensive’s web portal shows where a sound file from a hacked microphone, a screen capture and system information would reside (Wayne Ronaldson).
Part of the motivation to develop Overwatch Offensive, he said, was to increase his skill set and help security teams think more like adversaries. Just as the Assassin tool dodged Kaspersky and McAfee techniques, cybercriminals design their software to subvert those checkpoints.
“Using a custom tool that security operations teams have not seen before simulates a high-level threat actor giving the security team and business a real threat that they have to detect,” he said. “It will help test the business’ digital policy and procedures and most important, their security people.”
By considering these methods and other ways custom tools could impact an enterprise, Ronaldson said corporate security teams can better fend off real-world attacks.
“Some people just talk about red teaming in terms of digital,” he said. “But for me it’s different kinds of tech and physical and social stuff and supply chain vectors, either individually or together. I made this tool for adversary simulation. I wanted a tool you could use to collect to use business intelligence over long periods of time.”
Next, he said he plans to add machine learning capabilities to Overwatch Offensive. If an executive opens his or her computer at the within the same time span 90 percent of the time, Ronaldson said, “I want my implant to know that.”
Then, based on that pattern, he wants Overwatch Offensive to automatically run functions, like capturing a screenshot, when it’s least likely to be caught by security software.
“That’s going to take me ages,” he said.