House panel advances State Department bug bounty bill
The House Foreign Affairs Committee on Wednesday advanced a bill that would establish a bug bounty program at the State Department, the latest effort by lawmakers and security gurus to encourage agencies to use ethical hackers to secure their networks.
The Hack Your State Department Act would task the Secretary of State with setting up a vulnerability disclosure process for researchers to hunt for and disclose flaws in the department’s public-facing websites and applications. The program, which would emulate the Hack the Pentagon project the Defense Department carried out in 2016, would pay researchers for finding vulnerabilities of which State officials were unaware.
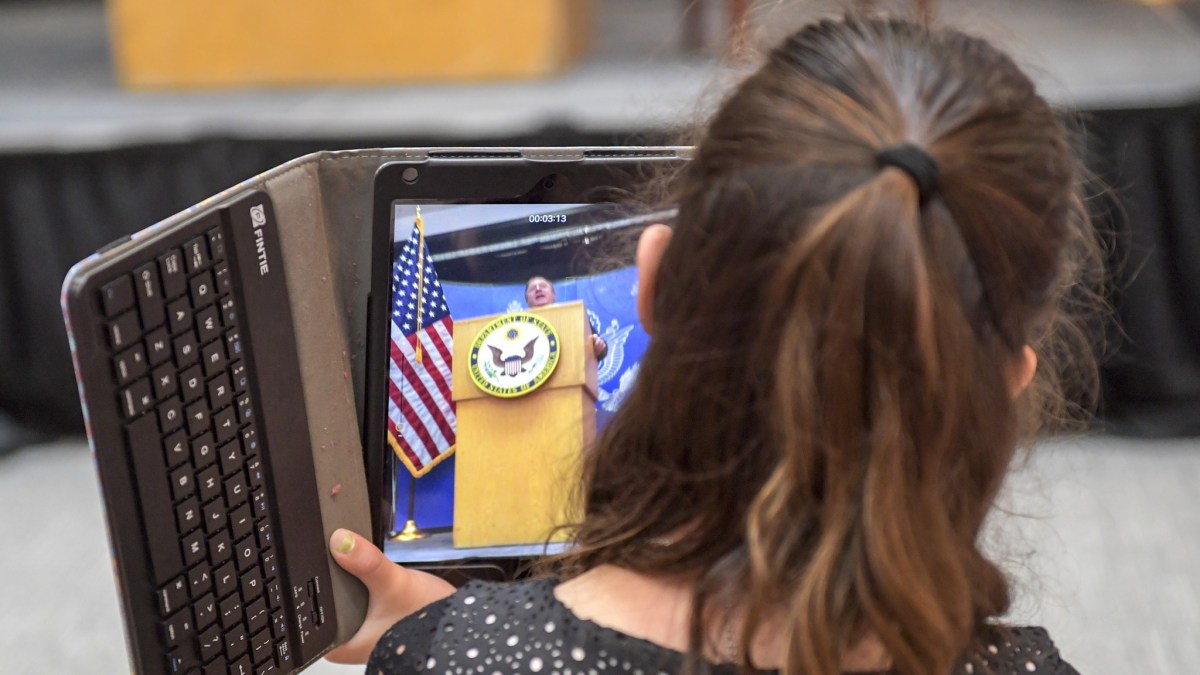
“Any agency or private sector company should have an independent way of testing security,” Rep. Ted Lieu, D-Calif., the bill’s sponsor, told CyberScoop. “This is one of the ways to do it – get an independent check on the strength of the cybersecurity system.”
“A lot of these systems – no matter how smart you think you are – there are always hackers out there who can figure out ways to breach them,” Lieu added.
Mark Kuhr, co-founder and CTO of Synack, a cybersecurity-testing firm that expanded the Pentagon’s bug-bounty program to cover sensitive IT assets, said he was encouraged by “positive momentum behind crowdsourced security testing.”
“The most successful programs vet for the most skilled and trustworthy hackers and aim for reducing the number of vulnerabilities over time as their systems become more hardened to attack,” Kuhr told CyberScoop. “We hope to see these considerations kept in mind as the bill advances.”
Lieu’s bill calls for establishing a bug bounty program within a year, but Katie Moussouris, a bug bounty expert and founder of consultancy Luta Security, cautioned that it would take longer than that.
Rather than establishing timelines for setting up bug bounties, “Congress should be funding an overhaul of internal capabilities” at federal agencies to make them more secure, Moussouris said.
“Bug bounties should only be used in circumstances where you’ve done your best to find and fix issues yourself, not as a replacement for due diligence and process, and not as a replacement for professional penetration testing,” Moussouris, who helped stand up the Hack the Pentagon program, told CyberScoop.
The Hack Your State Department Act is part of a series of legislation that aims to get federal agencies to embrace bug bounties, which are common practice in the private sector. The Senate last month passed legislation that would put $250,000 toward setting up a bug bounty program at the Department of Homeland Security. Lieu has introduced a companion bill in the House.
Lieu sees the legislation as part of a larger effort to open federal networks to ethical hacking.
“One reason we’re doing this is to raise the profile of this issue in general,” Lieu told CyberScoop. “Hopefully, other agencies will look at this and go, ‘Hey, we should try doing that.’ ’’
Malicious hackers have targeted State Department networks in recent years. In 2014, the department was forced to temporarily shut down its unclassified email system after suspected Russian hackers had breached it.






