The Energy Department’s Puesh Kumar on grid hacking, Ukraine and Pipedream malware

Cyberattacks against the energy sector have received increasing attention since a ransomware attack against Colonial Pipeline catalyzed a nation’s understanding of the risks to critical infrastructure. The Department of Energy is the agency responsible for ensuring that the energy sector is secured against all types of threats — whether physical or digital. The DOE stood up the Office of Cybersecurity, Energy Security, and Emergency Response, or CESER, in 2018 under the Trump administration to focus on such threats to the sector.
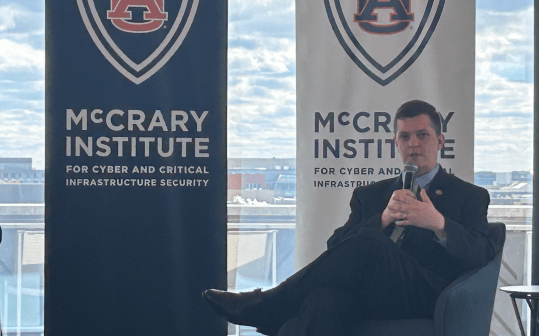
At the annual industrial cybersecurity conference S4, CyberScoop caught up with Puesh Kumar, director of CESER, to discuss where the new office is heading, lessons learned from the Russian invasion of Ukraine, and how to protect the grid of the future. The following interview has been edited for length and clarity.
President Biden’s forthcoming national cybersecurity strategy is, of course, something that’s on people’s mind these days. How are you thinking about the implementation of the strategy without getting into details of what’s in the strategy?
I can’t comment on the specifics of the strategy. But certainly, when large strategies like this come out, it really helps to ensure that we’re coordinated in taking the whole of government approach to thinking about security to not only critical infrastructure but also our federal systems. So, this strategy will hopefully bring all of us together and really prioritize our efforts in terms of security and resilience in my case for the U.S. energy sector, and really help identify some of the priorities we need to have as an organization so that we can address what the priorities are in the national cyber strategy. So, that’s how we’re looking at it as the work we’re doing feeds up into a larger whole of government strategy that will be outlined here.
CESER is still a relatively young office. I’m curious where you see it going in the future?
So, it’s been around since 2018. It’s not just cyber risk, which is certainly top of mind for us. It’s physical security risks. It is climate-based risks. We’re seeing all these risks that intersect and we had to ensure that we had a focal point that the Department of Energy really focused on security and resilience of the sector based on these increasing risks. So since then, it went from an office about $50 or $60 million to now we’re at an office of $200 million focused on this space and we’re looking at everything from policies, national level policies, state level policies, to tools and technologies and the research, development and demonstration that DOE does so well, that we can apply to the security space really thinking about designing things securely.
CESER partnered with the National Association of Regulatory Utility Commissioners to launch an effort to develop cyber baselines for distribution systems and distributed energy resources. Really, the idea is let’s come together and say what are the best practices for the distribution system. We certainly have the FERC and NERC regulators for the bulk power system, but as we start thinking of the distribution system, in light of a lot more connectivity on the grid like solar, wind, EVs and charging stations, batteries, that’s all great because it helps us address the climate risks. But as we do that, how do we ensure that we also have cybersecurity built into these new systems that we’re going to connect into the distribution system?
On the R&D side, the goal here is to ensure that our R&D continues the same pace with the threats we’re seeing. So, we should be R&D’ing for the threats of 5, 10, 20 years from now, as opposed to where the technology is today. As we think about heading more into the cloud, what does that look like as we start to see quantum becoming a bigger piece of the technology? How do we ensure that we can build in quantum resistance technologies into some of the energy systems of tomorrow? And then, of course, how do we ensure that all these comms pathways that are going to be needed to connect all this great new grid future is secure?
The anniversary of the invasion of Ukraine is coming up and so I’m curious if there were any lessons learned from the early days during the invasion when it seemed like people were concerned about Russian attacks on U.S. critical infrastructure.
This this unprovoked invasion by Russia is horrific, number one, and just seeing the resilience that Ukrainian people has been amazing. There are a couple of things that I’d say that come to mind. One: just look at Ukraine’s cyberdefenses. Clearly since 2015 and 2016 they’ve invested a lot in their own cyberdefenses and I think that is a story we should be really telling. We didn’t see as much cyber activity taking down operational impacts. Certainly, we saw a lot of kinetic impacts, but on the cyber side, they had a robust cyber defense. So, as a community, I think that’s a lesson learned for all of us that there’s so much we can be doing on the defense side.
Number two. The other piece is as this invasion was happening, Ukraine certainly had their cyberdefenses, but there were a lot of others that came in supported them and it wasn’t just the [U.S.] government. Certainly, we on the government side wanted to make sure we were supporting Ukraine with with all the resources and anything we could help with. But we saw private sector coming in. And so that brings into the conversation of operational cooperation and really the value of industry and government. We need the private sector working collaboratively with government on how we look at these threats. What they are seeing is equally as important as what we are seeing on the government side. If we start to connect these dots, we can get ahead of some of these threats. So for us, at the department and with our colleagues at CISA, this concept, this pilot activity that we’re engaging in called the Energy Threat Analysis Center is meant to be a spoke off of the Joint Cyber Defense Collaborative. It shows how we can come together as a community.
Now, that leads me to number three, broadly that in the case of Ukraine, just international collaboration. I think there’s another lesson to be learned — and certainly the operational cooperation is part of that — but if we have like-minded countries who have similar values, and want to make sure that we’re secure, we can be partnering with them. We can be thinking about cybersecurity in the context of where we think cyberdefenses need to be, but also what are some of the cyber norms going forward? We had all these allies coming together to support Ukraine in a lot of different ways. At the Department of Energy, we’re supporting Ukraine most recently in terms of getting grid equipment to Ukraine to help restore parts of their system. There is power in that, and we can leverage it to think about addressing things like supply chain risks.
Where is the Energy Threat Analysis Center at right now?
We’re still in the pilot base of the ETAC. Really, the idea is to bring industry and government together. Bring intel and non-intel together. All of us using our special powers and authorities to really look at these tough problems. We’re bringing together the community, the industry and government folks to start thinking through some of the cyberthreats that we’re seeing and then also looking at some of the systemic risks in the industry, so that we can do a better job of trying to get ahead of them.
Recently, Robert M. Lee of Dragos held a media briefing where he said that the Pipedream malware was the closest that the U.S. has ever been to having portions of the grid go offline. I’m curious if you agree with that assessment, and additionally, he did mention that there were around 12 specific utilities that were targeted. Can you confirm whether or not you believe that this was as close as Rob said and if the 12 utilities number is also correct.
Pipedream was, in many ways, a fundamental shift in the cyber capabilities that are out there. As you know, it’s a toolkit and it’s certainly one that concerns a lot of us at DOE, but it also concerned a lot of the cyber community once they saw the abilities of that toolkit, and how it could take advantage of normal processes in systems across the board to potentially cause destructive effects. From that vantage point, I would say that it is something that we should be paying attention to in terms of how this cyberthreat landscape continues to change and we have to stay ahead of these types of cyberthreats that are out there. I can’t comment on Dragos reporting out there, but I would say that that is something that we should be paying attention to in terms of just the toolkit that Pipedream is and where the cyberthreat is today versus where it will be tomorrow. We had the opportunity at DOE to work with our colleagues at DHS, NSA and FBI to help author the alert that went out on the Pipedream toolkit. Our focus has continued to ensure we’re staying ahead of it. As we’re discovering this stuff, we want to get it out to the community so they can then take the right actions.