Klobuchar to voting vendors: Don’t turn your back on good hackers when setting up a CVD program
After years of getting pummeled by critics for not embracing ethical hacking, the country’s biggest voting equipment vendors took a big step in that direction in September. They asked the cybersecurity community for ideas on how to set up a process through which researchers could flag software flaws for vendors to fix.
Companies that specialize in coordinated vulnerability disclosure (CVD) programs like Bugcrowd and Synack responded to the request for information. But the usual suspects weren’t the only entities to submit ideas.
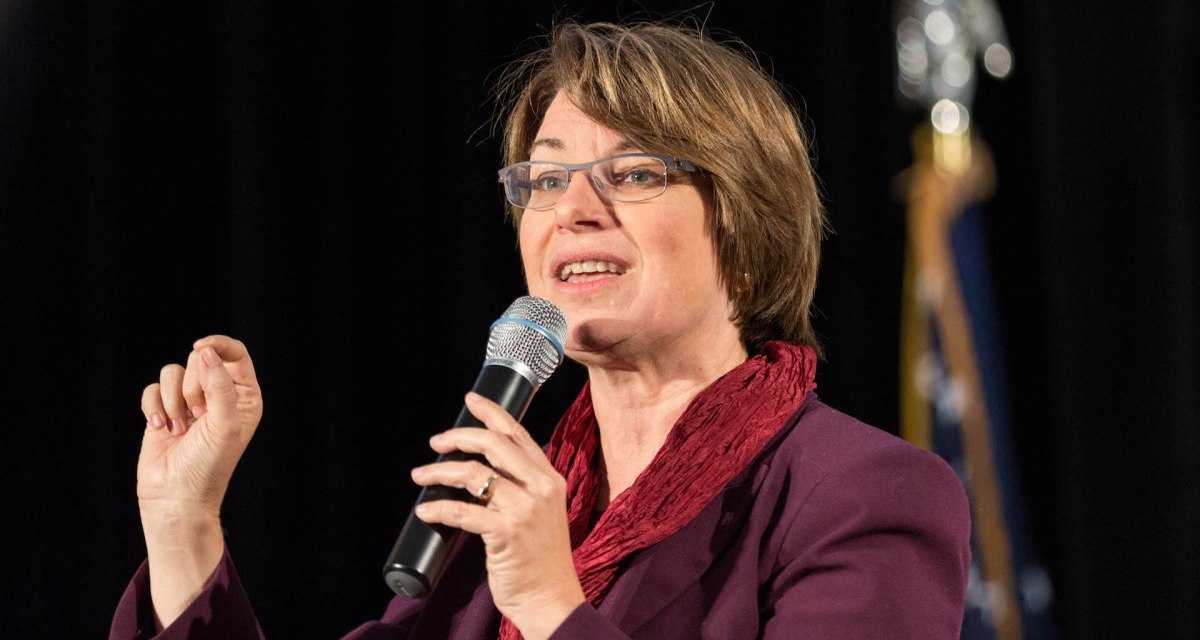
A Democratic presidential candidate and one of the most outspoken voices in the Senate on election security also chimed in.
In a four-page letter to the industry association establishing the CVD program, Sen. Amy Klobuchar, D-Minn., advised the voting-gear vendors to ditch their reservations about working with unvetted researchers, pay close attention to their supply chains, and set a timeline for getting software bugs fixed.
“[V]oting system manufacturers must work out reasonable, time-limited, and researcher-friendly terms for disclosure,” Klobuchar wrote to an election industry working group at the IT-Information Sharing and Analysis Center (IT-ISAC).
Klobuchar’s detailed letter is a push to ensure that the country’s three biggest voting equipment makers — Election Systems & Software, Dominion Voting Systems, and Hart InterCivic, — don’t build a CVD program that deters white-hat hackers from participating. She advised the vendors not to exclude any hacker from their CVD program who could help secure voting systems. Limiting participation to “vetted researchers would be detrimental the effectiveness” of the program, she warned.
The prospective CVD program is one of multiple initiatives to strengthen U.S. election security initiated since 2016, when Russian operatives probed IT systems that supported voting in states across the country.
Done right, advocates of the CVD program say, it can put voting equipment makers on a more proactive security footing and build bridges with ethical hackers.
A potentially ‘significant step forward for election security’
Election security has scarcely come up in Democratic presidential debates despite the fact that U.S. intelligence officials warn that the 2020 election will draw concerted attempts by foreign powers to interfere in the electoral process. But in the Senate, Klobuchar has pressed the issue by calling on voting equipment vendors to be more transparent about their plans to make their products more secure. She also sponsored a bill, which stalled in the Senate, aimed at boosting information sharing between state election officials and the federal government.
In her recent letter to voting equipment vendors, Klobuchar contested a few of the assumptions the vendors put forth in the RFI. The RFI expresses interest in a CVD program for systems that are isolated and disconnected from the internet. But Klobuchar pointed out that vulnerabilities in public-facing systems can have security implications for voting infrastructure that isn’t sitting on the internet.
“If a member of the public finds a vulnerability on a public website run by a voting system manufacturer, this could have unexpected ramifications, particularly if that website is hosted on a server inside a trusted environment,” Klobuchar wrote.
“Voting system manufacturers should acknowledge this by welcoming vulnerability reports that apply to all of their internet-accessible IT systems, including systems not intentionally made internet-accessible,” she added.
CVD programs are common practice in other industries, and Klobuchar cited a few that the voting equipment makers might learn from, including programs at the U.S. General Services Administration, and Dräger, a medical device manufacturer.
It is unclear when the voting equipment vendors might establish the CVD program.
“We are in the process of reviewing the responses we received [to the RFI] and plan to meet in person before the end of the year to discuss next steps and a path forward,” Scott Algeier, executive director of the IT-ISAC, told CyberScoop in an email.
“We are committed to moving as fast as we can,” Algeier said.
If and when the program gets off the ground, Klobuchar said, it “could be a significant step forward for election security.”
You can read the full letter from Klobuchar to the IT-ISAC’s Elections Industry Special Interest Group below.
[documentcloud url=”http://www.documentcloud.org/documents/6550653-Senator-Amy-Klobuchar-IT-ISAC-RFI-Comment-Signed.html” responsive=true]






