Inside the NSA’s CDX, a high-tech competition pitting cadets against elite attackers
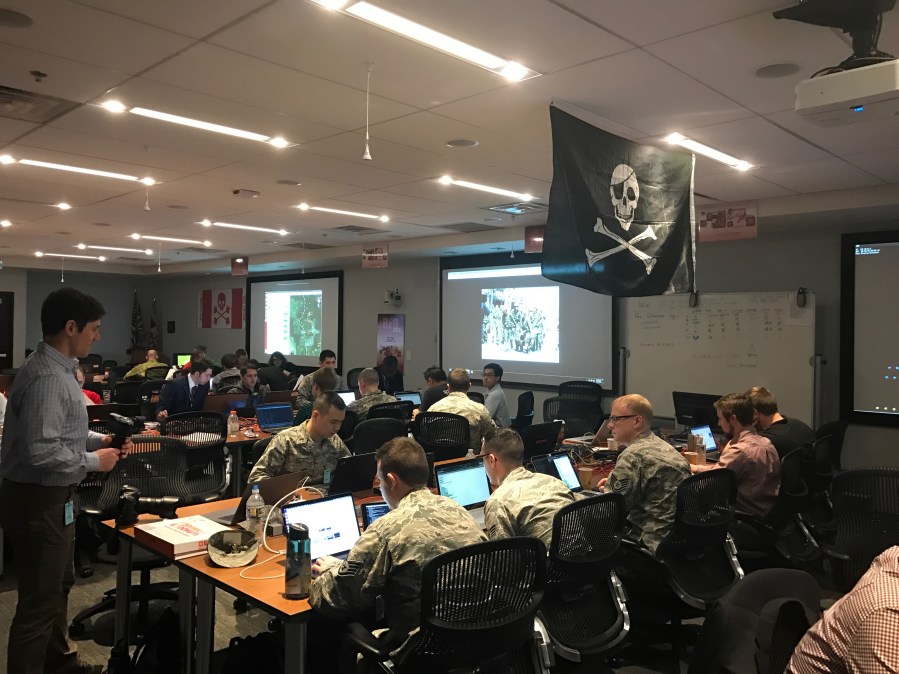
Professional hackers from the NSA, U.S. Cyber Command and foreign militaries are launching a barrage of simulated cyberattacks this week as part of a training exercise to help teach students at the service academies for the Navy, Army, Coast Guard, U.S. Merchant Marine and Canadian Royal Military how to better defend sensitive computer networks.
The annual NSA-led event, named the Cybersecurity Defense Exercise, or CDX, brings together rising talent with seasoned cyber-warriors in a simulated war games environment, where the undergraduates must monitor, identify and ultimately defend against a wide array of remote computer intrusions.
The intrusions themselves are engineered with open-source, commercially available exploits and other hacking tools. “We don’t use anything homegrown,” said CDX Technical Lead James Titcomb, a full-time NSA employee in the spy agency’s information assurance directorate.
“We don’t hit them with anything on the level of a nation-state,” Titcomb said. “The idea is that they should at least know how to defend against these [attacks].”
Each academy competes with the others to see which can best defend its own respective network while simultaneously ensuring that it is resilient and reliable for authenticated users.
Thursday marks the fourth day of the five-day tournament.

The exercise consists of four total “cells” — the attackers’ red cell, defenders’ blue cell, a white cell of referees and gray cell meant to represent active, neutral users relying on the networks being protected by the cadets and midshipmen. In a real-world scenario, the gray cell may represent a military unit using a communications channel that could be hacked.
Referees closely monitor the competition and are responsible for awarding points and penalizing teams if they break a strict set of predetermined rules.
Participants are working this week from computer labs based across the country, while the attacking team, or red cell, and competition administrators, operate from a high-tech facility in Columbia, Maryland — a short drive away from the secretive spy agency’s main headquarters at Fort Meade Army Base.
A total of more than 70 graduate and undergraduate military service academy students are involved in the 2017 CDX.
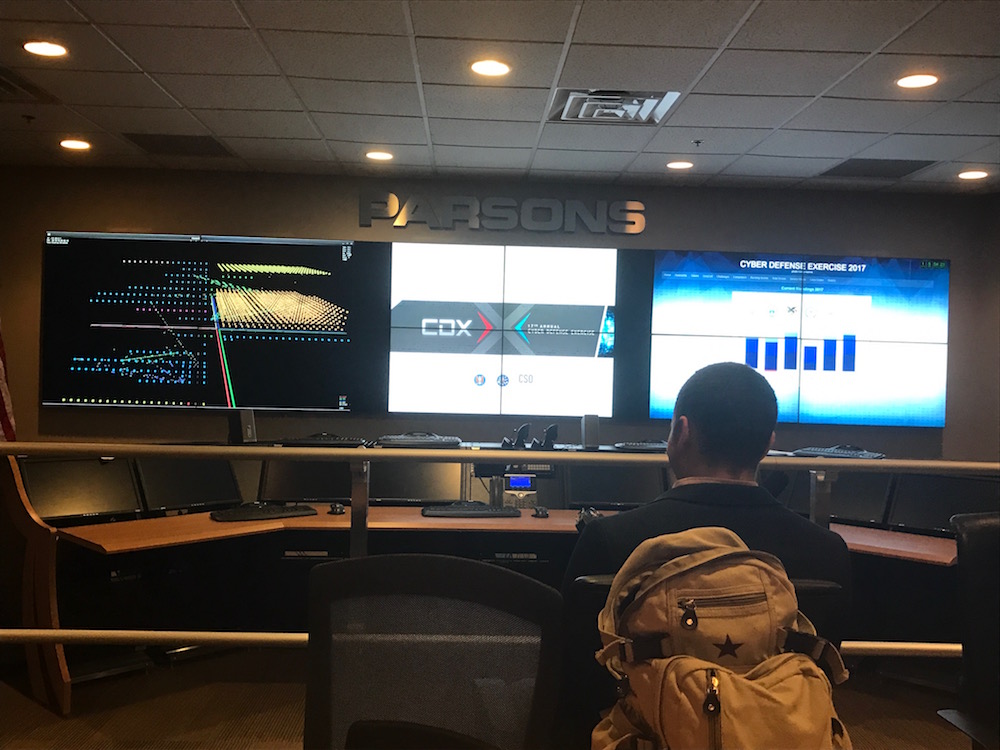
Screen on the left shows a three dimensional model for network activity related to the competition
Each year, the competition offers a set of separate challenges that are divided from the larger red team/blue team exercise. For 2017, those challenges include completing tasks related to offensive hacking, malware analysis, host forensics and defending an unmanned aerial vehicle from being compromised. Graduate-level students can also compete in two other, exclusive challenges that were established to test the ability of participants to protect data as it’s being transmitted between a computer, unmanned ground vehicle and small space satellite.
The simulated UAV challenge is a recent addition to the competition, organized by the Air Force Research Lab. The goal for students is to establish a secure, unbreakable communications link between their drone and its corresponding control console, explained the lab’s Sam Allen. As of Wednesday afternoon though, nearly all of the drones defended by the cadets had been taken over by the red cell, Allen said.

The CDX trophy
Founded in 2002, the CDX has grown and steadily evolved to match the cyber-workforce needs of the Defense Department. From a planning perspective, the competition’s inclusion of a UAV, and the more recent, UGV and space satellite cyber defense challenges is reflective of how the U.S. government is broadly thinking about emerging threats.
In 2017, for the first time, a small group of undergraduates are also participating in the red cell component of the competition — a move that Titcomb said will simultaneously teach cadets how to develop more effective defensive measures.
One of the few undergraduates who was supporting the Maryland-based red team spoke with CyberScoop about his CDX experience.
“These guys are on a whole other level to what we do. Just being able to look over their shoulder this week has been a really great opportunity for us,” said 20-year-old U.S. Military Academy student Connor Eckert. “Talking to a lot of the NSA guys here, it has really opened my eyes to how much the civilian side is involved, it’s not just the military for cyber.”
“[A career in the NSA] could open up some doors for me after my time in service to do this sort of thing on an ongoing basis,” said Eckert.
After graduation and the completion of their respective service requirements, it’s not uncommon for former CDX participants like Eckert to join the U.S. intelligence community.
Even so, Titcomb said that the competition was never designed to specifically recruit individuals to the NSA. The underlying objective, he said, is to develop talent across the various military branches.


