Global malware attack ‘most likely’ carried out by a nation-state, NATO-sponsored researchers say
The search for the source of last week’s global malware attacks continues as experts are increasingly pointing toward Russian involvement in the incident.
The NATO-affiliated Cooperative Cyber Defence Centre of Excellence (CCD COE) in Tallinn, Estonia, concluded last week that the attack was “most likely” carried out by a nation-state. The report followed a string of separate analyses that said the attacks appeared to have Russian sources.
CCD COE researchers pointed to the sophistication of the malware.
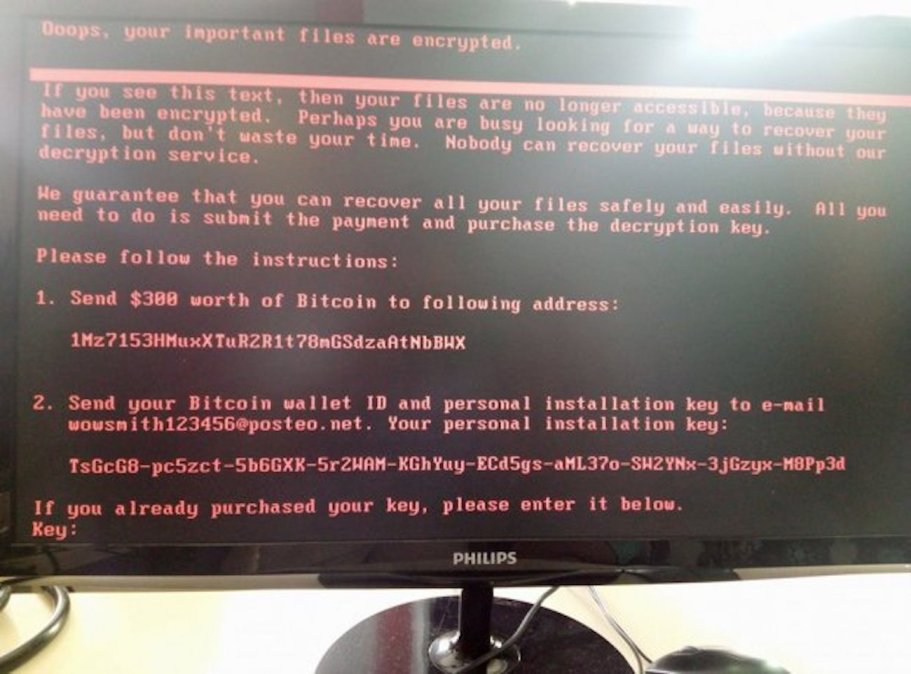
“In the case of NotPetya, significant improvements have been made to create a new breed of ultimate threat,” said one of the researchers, Bernhards Blumbergs. “Among all new features, the malware has been more professionally developed in contrast with sloppy WannaCry, and instead of scanning the whole Internet it is more targeted and searches for new hosts to infect deeper on local computer networks once initial breach has occurred.”
The assertion by NATO-sponsored researchers that a nation-state probably spread the malware only intensifies questions about what the affected countries and the international community might do next.
Cyber-operations can trigger Article 5 of the North Atlantic Treaty, which can include military responses, as NATO’s secretary general has repeatedly affirmed. There are no reports that allege the consequences of the malware are on the level of an armed attack, however, so a military response is not on the table.
“If the operation could be linked to an ongoing international armed conflict, then law of armed conflict would apply, at least to the extent that injury or physical damage was caused by it, and with respect to possible direct participation in hostilities by civilian hackers, but so far there are reports of neither,” Tomáš Minárik, researcher at NATO CCD COE Law Branch said.
“There is a lack of a clear coercive element with respect to any government in the campaign, so prohibited intervention does not come into play,”Minárik said. “As important government systems have been targeted, then in case the operation is attributed to a state this could count as a violation of sovereignty. Consequently, this could be an internationally wrongful act, which might give the targeted states several options to respond with countermeasures.”
Tallinn’s CCD COE was established in 2008, one year after Estonia fell victim to a landmark cyberattack described as “Web War I” that has widely been widely credited to Russian hackers. It’s important to note that CCD COE is sponsored by NATO but the researchers are independent so — contrary to the way these remarks have been portrayed in some media reports — these are not official NATO statements. Nevertheless, they represent important insight into the work of researchers close to the Western alliance.
At around the same time on Friday, the Czech cybersecurity firm ESET published research suggesting the main suspect behind the global malware attack was a hacking group known as Sandworm that is suspected of ties to the Russian government. Kaspersky, a Russian cybersecurity firm, released its own research pointing toward possible Russian connections. Ukranian authorities blamed the Russian government as well.
Ukranian officials told the Associated Press that M.E. Doc, the Ukrainian tax software company whose hacked servers may have been at the heart of Tuesday’s malware attack, will face charges for blowing off warnings about known security vulnerabilities.






