DEF CON report finds decade-old flaw in widely used ballot-counting machine
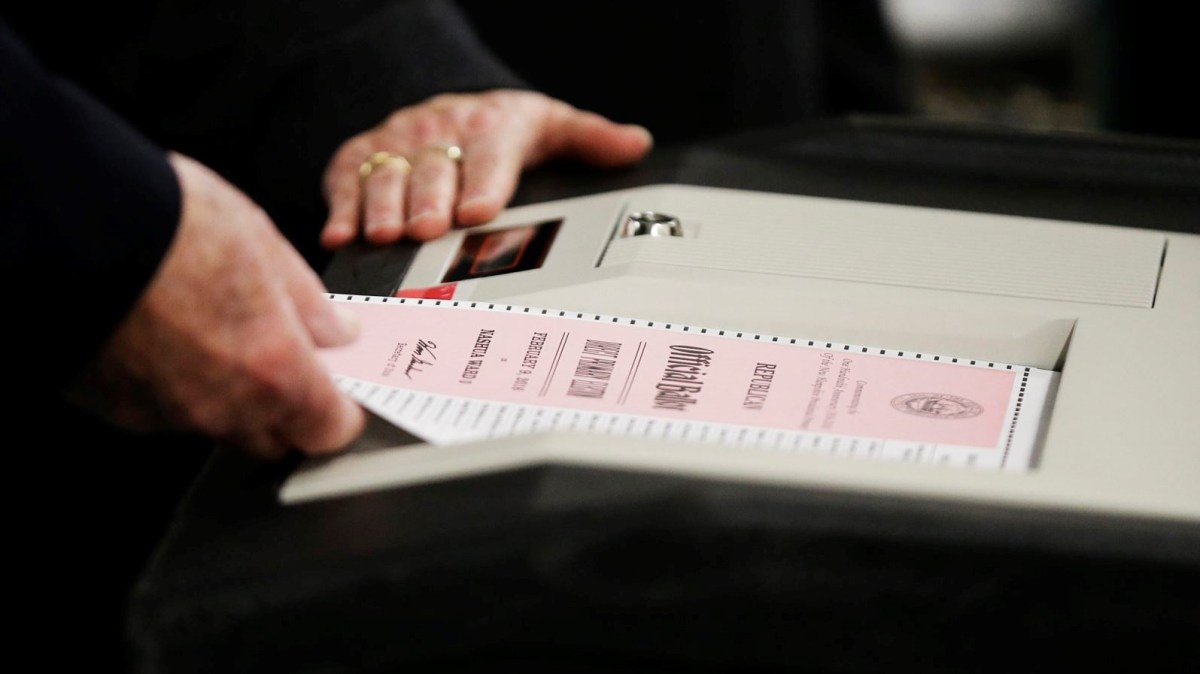
A voting tabulator used to count ballots in more than half of states has a decade-old flaw that leaves it vulnerable to hacking, according to a report published Thursday by security researchers.
The M650 machine, made by top voting-equipment vendor Election Systems and Software, could be compromised using a flawed software-updating procedure to infect it with malicious code, according to the report from the Voting Village at DEF CON, a renowned annual hacking conference. “It is very doubtful that the operators of M650s all over the U.S. are aware” of the need to combat the updating procedure by reformatting a ZIP disk, the report states.
The M650 vulnerability was revealed in a 2007 report by the Ohio secretary of state’s office, pointing to a long lag time in patching some voting gear. “[D]isclosing vulnerabilities does not seem to be enough to get them fixed, even years later,” the DEF CON report laments.
An ES&S spokesperson told CyberScoop the vendor had stopped making the machine in 2008. “This means the base-level security protections on the M650 are not as advanced as the security protections that exist on the voting machines ES&S manufactures today, although we believe that the security protections on the M650 are strong enough to make it extraordinarily difficult to hack in a real-world environment and, therefore, safe and secure to use in an election,” the spokesperson said.
In 2016, 26 states and the District of Columbia used the M650 in elections, according to the DEF CON report.
The flaw was one of several found by security researchers dissecting voting equipment at the conference in Las Vegas in August. The findings come just weeks before the midterm elections amid a tense debate between security researchers and voting equipment vendors on just how aggressively vulnerabilities in the equipment should be uncovered.
Tensions flared before the Voting Village opened as the National Association of Secretaries of State and ES&S criticized the village as an unrealistic environment that would paint a misleading picture of voting-system flaws. In a recent interview with CyberScoop, Christopher Wlaschin’s vice president for systems security, said that white-hat hackers already test the vendor’s equipment. “We believe, and our customers believe, that that’s sufficient and we see no value in submitting our equipment or our software to anonymous hackers whose intentions are unknown.”
On Thursday, Rob Joyce, a top cybersecurity official at the National Security Agency, said he wished the voting village could be as collaborative as the car hacking village at DEF CON, to which Tesla has submitted equipment to be tested.
“Steering the voting village to similar collaborative relationships will take us to the next level and address the constant erosion of trust, which only helps further the objectives of our adversaries,” Joyce wrote in an op-ed for The Cipher Brief. He praised DEF CON for assembling “amazing talent and expertise,” people who have “an enthusiasm to make things better.”
Jake Braun, one of the village’s organizers and a co-author of the report, told CyberScoop that the conspicuous objections to the village from ES&S and NASS notwithstanding, there had been a “dramatic expansion of engagement with election officials” in the village this year compared to last. More than 100 election officials visited the village this year, according to the report.
The report covers numerous other aspects of election security, including supply-chain risks to voting equipment. There are “essentially no security procedures to determine whether the machine parts are trustworthy or pre-hacked before the machine is assembled,” the authors wrote.
The document also advises state and local officials to prepare a crisis communications plan in the event that websites reporting results on election night get hacked. Among the recommendations is for an organization’s employees to “stop using email and website messaging immediately” and to use personal devices, if possible, in the event of a cyberattack.
Braun said the document offers actionable recommendations that could make a difference in boosting election security just weeks before the midterms. “Obviously, massive changes are not possible between now and the election,” he told CyberScoop. “But some of these things are pretty simple.”
You can read the full DEF CON report below.
[documentcloud url=”http://www.documentcloud.org/documents/4946384-DEF-CON-26-Voting-Village-Report-FINAL-1.html” responsive=true height=500]






