The endless hunt: Looking for patterns in malware data

“No research is ever really finished,” observes Kenneth Geers, senior research scientist for Comodo.
He’s talking about the second massive set of data he’s crunched in two weeks: The Comodo Threat Labs Q2 2017 report.
It was only a week ago that Geers released Comodo’s Q1 data — the first time the company sought to leverage the huge amounts of information about malware attacks gathered by the 90 million installs of its software across the world.
This time around, the dataset is four times as large — more than 97 million malware incidents — and Geers told CyberScoop the analysis he’s been able to do on it so far is “just scratching the surface.”
“I’m going to be working all week,” he said, preparing for a presentation at DEF CON Saturday.
In Q1, he demonstrated that “different malware types map against [national] GDP per capita.” The more advanced types of malware, like backdoors, make up a greater proportion of the attacks in wealthier countries. For worms, the least sophisticated kind of malware, Geers explained, “It’s the opposite, the highest ratio is in the most impoverished nations.”
The Q2 data bear out one conclusion he drew from the first set: Russia’s IT networks are riddled with malware.
“Russia and South Africa suffered the highest volume of computer worms,” the Q2 report reads. “Frankly, this situation should be urgently addressed within Russian and South African IT security communities. Given the nature of worms, what this means is that many networks in these countries do not have nearly enough licensed, patched and professionally managed hardware and software. Part of this problem, of course, is non-cyber and may take years to rectify.”
This time around, Geers wants to map malware incidence longitudinally — across time as well as space.
“I’m sure we will find clusters of malware activities around [significant] geo-political events … like elections,” he said.
For instance, the data show several spikes in malware activity in the U.S. — the largest in the week of May 8. “I will look into that,” he said.
The other correspondence he wants to check: What happened to malware incident levels in France during the run-up to the election.
In a previous analysis of malware in the middle east he conducted, he said, “For each one of the major spikes [in malware occurrence] there is a geopolitical event that corresponds.”
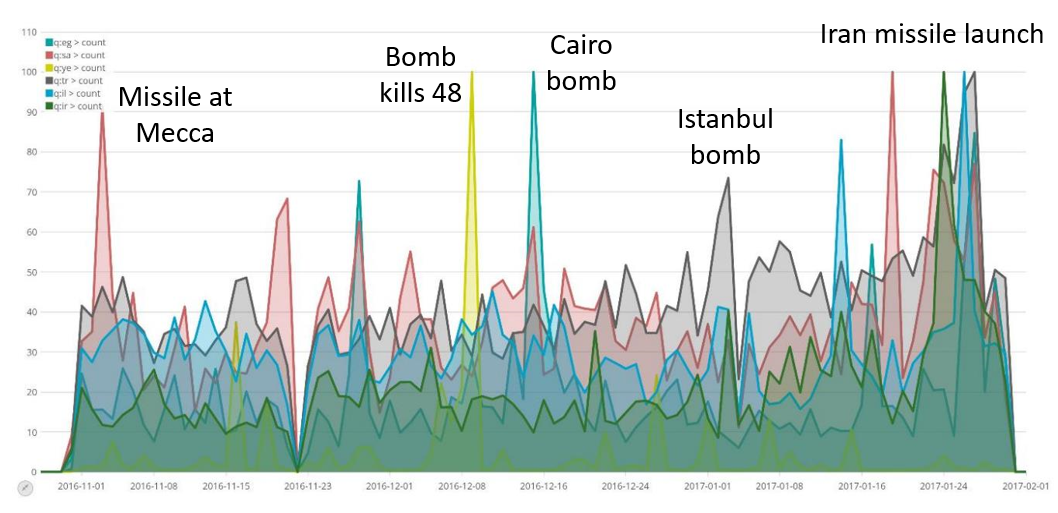
Longitudinal analysis of Middle Eastern malware incidents (Source: Comodo)
For each of those events, “There’s going to be local and international intelligence agencies running [cyber-espionage] collection operations,” in addition to cybercriminals attempting to exploit major news stories with phishing campaigns, Geers said, explaining why the spikes shadow political and other kinds of crisis.
“I don’t want to over dramatize the numbers,” he added, “But I firmly believe there are thousands of cyber-espionage operations being run every day — you can see them in the data.”





