CISA guide seeks a unified approach to software ‘ingredients lists’
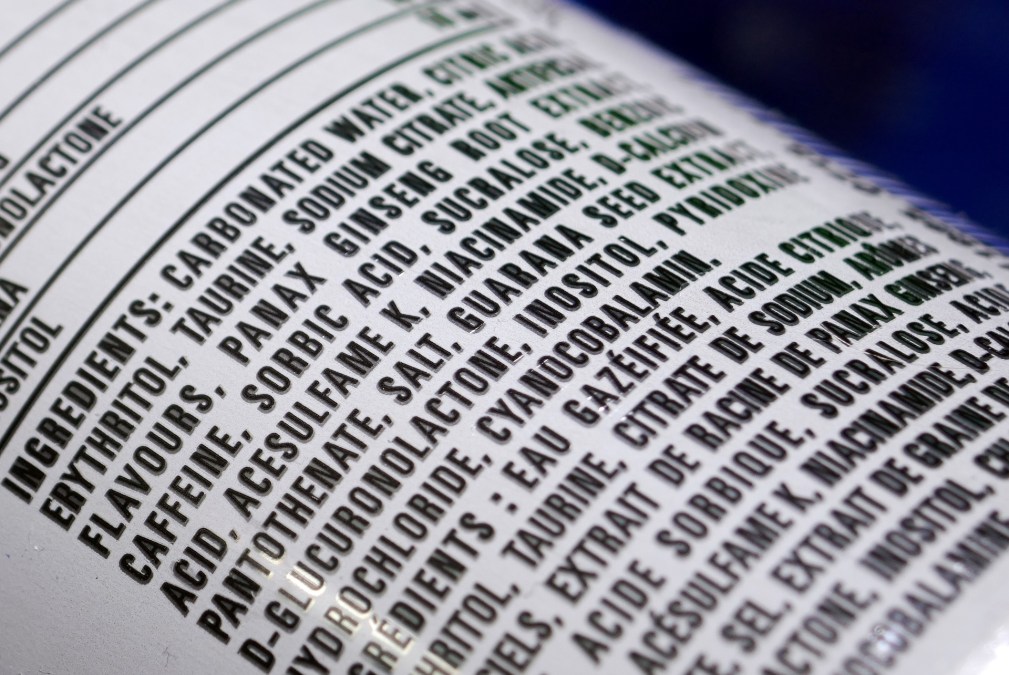
Compiling an “ingredients list” for software can help organizations reduce cyber risks, avoid fines and save time, among other benefits, a Cybersecurity and Infrastructure Security Agency-led guide published Wednesday advises.
The CISA document, produced with the National Security Agency and cyber agencies from 14 other countries, aims to produce a shared vision on advancing the concept known as software bill of materials, or SBOM. It’s a nearly universally praised idea whose implementation has been playing catch-up with the embrace of its theoretical value.
In the guide, the agencies tout SBOMs as a way to adopt secure-by-design principles, where software makers implement security as part of the design process rather than as something to be tacked on afterward.
“The ever-evolving cyber threats facing government and industry underscore the critical importance of securing software supply chain and its components,” Madhu Gottumukkala, acting director of CISA, said in a news release accompanying the guide’s publication. “Widespread adoption of SBOM is an indispensable milestone in advancing secure-by-design software, fortifying resilience, and measurably reducing risk and cost.
“This guide exemplifies and underscores the power of international collaboration to deliver tangible outcomes that strengthen security and build trust,” he said. “Together, we are driving efforts to advance software supply chain security and drive unparalleled transparency, fundamentally improving decision-making in software creation and utilization.”
Publication of the guide follows closely on CISA’s updated federal agency guidelines for SBOMs, a set of rules that got mixed reviews when it came out last month.
Wednesday’s guide aims toward a unified approach to implementing SBOMs.
“Divergent implementations could hinder widespread adoption and sustainable implementation of SBOM. An aligned and coordinated approach to SBOM will improve effectiveness while reducing costs and complexities,” the guide reads. “When used widely across sectors, regions, and countries, supply chain illumination drives better ‘ingredients’ for everyone to use and helps ensure that known risks are addressed early. SBOM adoption is an integral condition for software to be secure by design.”
According to the guide, SBOMs help with vulnerability management by allowing organizations to be able to better track vulnerabilities when they arise, making it faster and more efficient to fix flaws. It helps organizations comply with industry-specific policies or government regulations and make decisions about their software purchases as such, thereby pushing vendors to give greater attention to cyber risk. It can help organizations manage software licenses, with violations of open-source licenses something that can trigger fines or reputational damage.
The guide advertises SBOMs as something for software makers, buyers and operators to adopt, as well as government cybersecurity agencies.
Australia, Canada, the Czech Republic, France, Germany, India, Italy, Japan, the Netherlands, New Zealand, Poland, Singapore and South Korea were the other countries involved in producing the guide.