Hackers linked to the Chinese government increasingly target Russia, analysis suggests

Nation-state hackers with links to the Chinese government seem to be targeting Russian entities at an increasing rate, an analysis published Thursday suggests.
The ongoing activity appears primarily espionage-related as the Chinese government may be working to gain intelligence about Moscow’s actions in the Ukraine war, even while trying to strengthen its political alliance with Russia.
Tom Hegel, a senior threat researcher at cybersecurity firm SentinelOne, told CyberScoop that Chinese cyber espionage that had typically targeted a wide range of governments and other entities has seemingly pivoted to “a lot more Russian based activity.”
The increase “really highlights the importance of them needing intelligence collection out of Russia right now to figure out what’s going on inside the government,” Hegel said.
Hegels’ analysis examined a recent example of suspected Chinese cyberattack against Russian government targets with credential-stealing malware. The attackers attempted to deliver the malware in a document purporting to be a warning from the Russian government about phishing attempts.
A Malwarebytes researcher flagged that document June 16, and researchers with the Tokyo-based nao_sec added more detail June 20. The Ukrainian Computer Emergency Response Team published a more thorough examination June 22, and Hegel’s analysis built upon those leads.
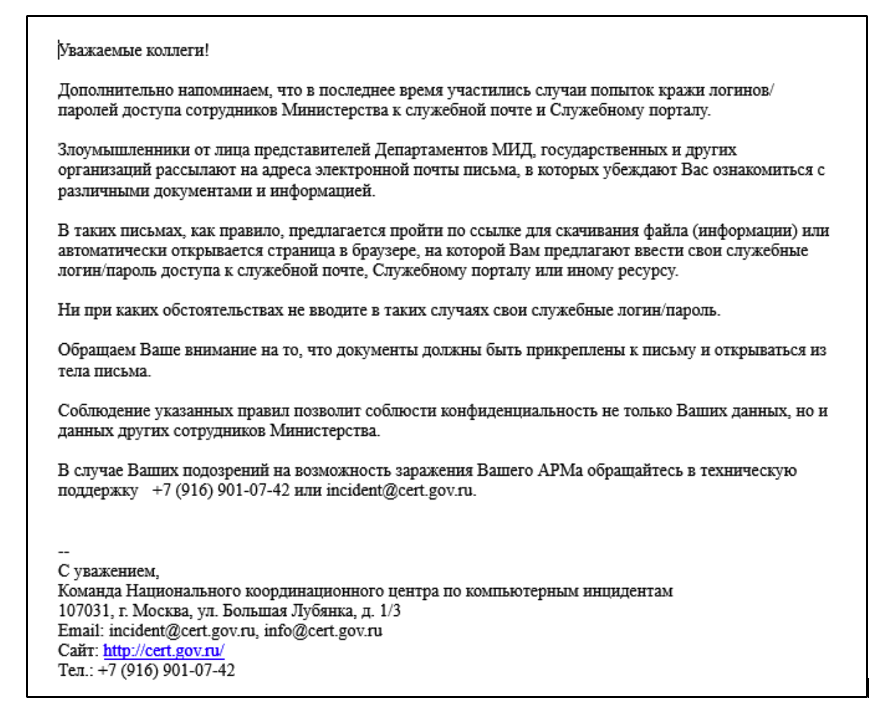
One of the phony documents purported to be a warning from the Russian Computer Emergency Response Team to Russian entities warning of increased cyberattacks on Russian government targets. The attackers built the document using the RoyalRoad document builder, which then attempted to infect a target with the Bisonal remote access tool (RAT). Both sets of malware have long been tied to various Chinese-aligned hacking efforts.
Hegel’s research also revealed a previously undetected RoyalRoad document used in a campaign targeting the Pakistan Telecommunication Authority through a potentially compromised Pakistani government email account.
Chinese hackers have likely been behind multiple campaigns in the wake of the Feb. 24 invasion of Ukraine, according to Hagel, that have been referred to variously as Scarab, Mustang Panda and Space Pirates. This latest campaign could represent a new, separate effort, Hegel said, but there is not enough data to make a definitive attribution.
Both the RoyalRoad and Bisonal malware have been in use for many years, making the attribution that much harder, he said. “I think it would be a mistake for anybody to [link] Bisonal, or RoyalRoad, to one individual actor group because it’s so long running.”
The toolkits’ longevity speaks to shared resources across multiple Chinese hacking groups with varied objectives, he said, but also the state of security of some Russian targets.
“The fact that these toolkits evolve and continue to operate really speaks to how well they’re resourced, and the state of the defense side,” he said. “Nothing can really stop them from continuing to use this. It’s still successful in many cases, as we see here. You look at the exploits they’re using in these documents, they’re years old exploits. They’re popping people that are out of date by quite a few years.”
China’s increased focus on Russian entities offers a window into the geopolitical complexities on display due to the Ukraine-Russia war. Just before the invasion, the Chinese government denounced NATO activity in Europe, and in the months since has tried to walk the tricky line of showing support for Russia’s needs without running into international sanctions, the Washington Post reported in June.
But Chinese hackers have simultaneously deployed “sprawling, and increasingly sophisticated” tactics to spy on allies, including Russia, the New York Times wrote after a Chinese hacking campaign seeking military technological data was exposed in May.
The Chinese government is also looking for fresh information about Russian actions, experts recently told CyberScoop, leaving cyber-enabled espionage as an obvious collection tool.

This story was featured in CyberScoop Special Report: War in Ukraine






