Flaws in Qualcomm chips could allow snooping, Check Point finds
Software flaws in millions of smartphones used throughout the world could give hackers a gateway into users’ personal data.
More than 400 vulnerabilities in chips used in approximately 40% of the world’s cellphones and devices could allow hackers to spy on users’ GPS location and microphones in real-time, according to new Check Point research.
The vulnerable units, Digital Signal Processor units or DSP chips made by Qualcomm Technologies, specifically Qualcomm Snapdragon DSP chips, impact popular cellphones and devices from Samsung, LG, Xiaomi, and Google are vulnerable, according to researchers.
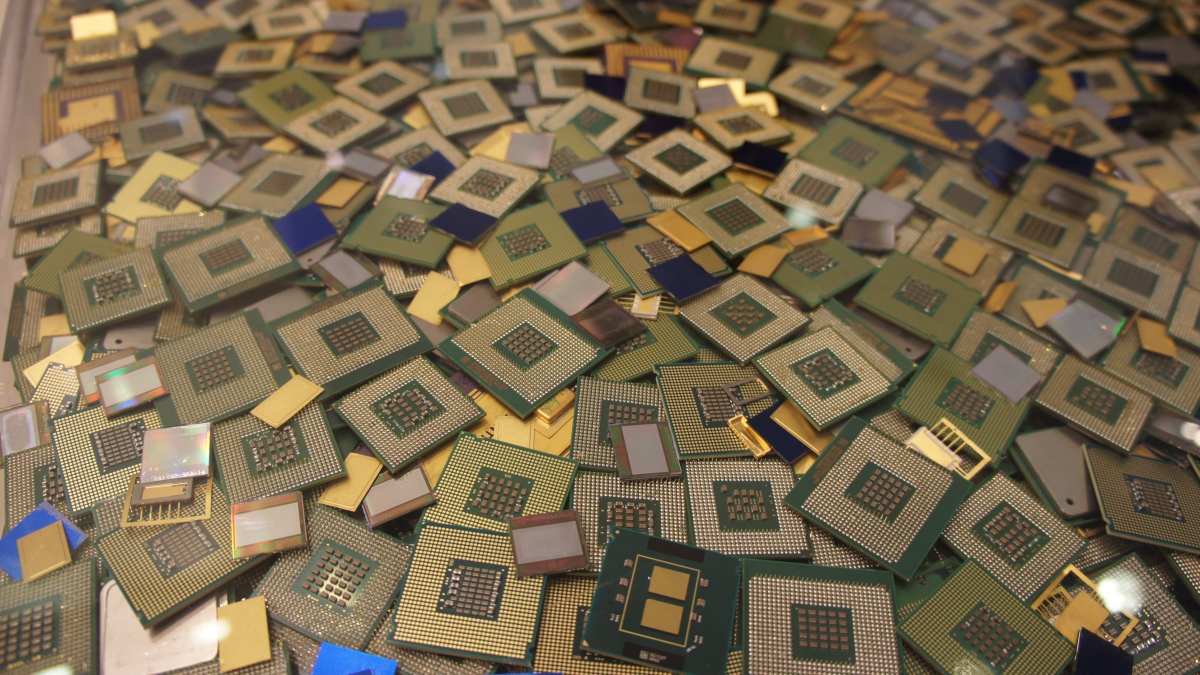
DSP chips, made up of software and hardware, are designed to enhance charging, audio features, and multimedia activities. But these flaws are a reminder that as ubiquitous as chips are in popular devices, vulnerabilities abound. The Spectre and Meltdown vulnerabilities, discovered by Google’s Project Zero two years ago, affected nearly every modern computer chip, for instance.
In a statement shared with CyberScoop, Qualcomm said it has seen no evidence that hackers have exploited the vulnerabilities, and that it is working with original equipment manufacturers to remedy the issue.
“Providing technologies that support robust security and privacy is a priority for Qualcomm,” a Qualcomm spokesperson said. “[W]e worked diligently to validate the issue and make appropriate mitigations available to OEMs…We encourage end users to update their devices as patches become available and to only install applications from trusted locations such as the Google Play Store.”
Some of the vulnerabilities could enable attackers to spy on vulnerable users’ photos, videos, calls, GPS location, and even access their microphones, according to Check Point. Others could allow them to force the phone to be unresponsive, by making all of the data stored on the phone permanently unavailable, including contacts, photos, and videos, Check Point security researcher Slava Makkaveev said. Some of the vulnerabilities would also enable attackers to hide malware in their campaigns, according to Makkaveev.
The vulnerabilities do not appear to affect iPhones. But in Android devices, if there is one original equipment manufacturer, or OEM, that has a vulnerable Snapdragon DSP the vulnerability can essentially spread to others, according to Makkaveev.
“It’s possible to run a library intended for one device, for example Chinese Xiaomi, on any other device, for example Samsung,” Makkaveev will say in his presentation at the DEF CON security conference Friday. “This means that a vulnerability discovered in one OEM’s library compromises all Snapdragon-based Android devices.”
Qualcomm has notified multiple vendors of the vulnerabilities, which have been given several CVE numbers, including, CVE-2020-11201, CVE-2020-11202, CVE-2020-11206, CVE2020-11207, CVE-2020-11208, and CVE-2020-11209.





