U.S. Army machine communicated with infrastructure used to deploy WannaCry

Clarification: U.S. Army Cyber Command disputed CyberScoop’s earlier description of the incident, saying that the IP address supplied to CyberScoop was indicative of research, rather than a machine that had been infected. The story has been amended.
A machine tied to an IP address associated with the U.S. Army connected to a command and control infrastructure used to send out WannaCry ransomware, CyberScoop has learned based on a list of affected IP addresses provided by a security vendor.
The vendor observed this IP address, which is tied to the Army Research Laboratory, communicate with the attacker command and control server a total of seven times on May 12. The IP address is tied to a server block parked at a host located at Fort Huachuca, Arizona.
The type of machine the IP address is attached to is unknown.
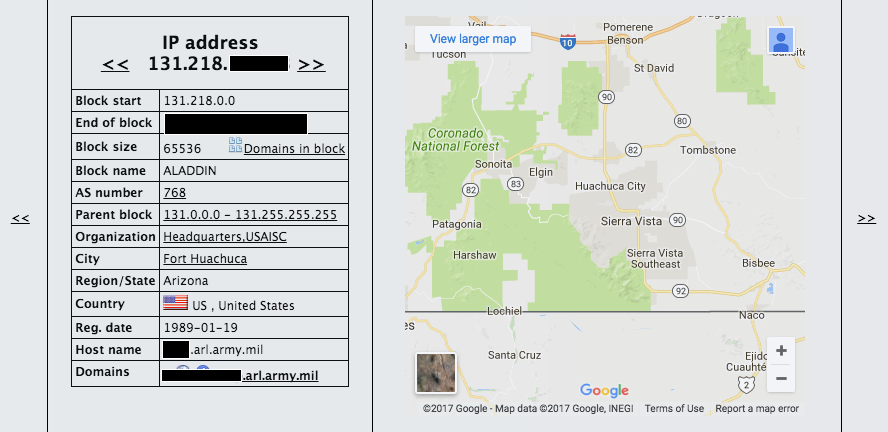
Victim IP associated with ARL
Fort Huachuca is home to the Army’s Network Enterprise Technology Command (NETCOM) and Information Systems Engineering Command (USAISC).
In a Tuesday statement sent to CyberScoop, ARL public affairs officer Tom Moyer neither confirmed nor denied whether an infection had taken place: “The U.S. Army Research Laboratory takes the security of its networks very seriously and does not openly discuss the systems and methods used to ensure the integrity of its networks.”
Other IP addresses from the list supplied to CyberScoop have been independently confirmed to be affected by WannaCry. Our sister publication StateScoop reported Monday that government offices in Cook County, Illinois, were infected, making it the first known case of a local government being hit by the computer virus.
The vendor provided the data on condition of anonymity in order to discuss sensitive material.
The WannaCry campaign began on Friday, affecting upwards of 300,000 computers. The ransomware is spread by leveraging malicious computer code that was once used by the National Security Agency.
A mysterious group known as the Shadow Brokers started sharing supposed NSA hacking tools, including the tool used to spread WannaCry, through a series of blog posts starting last August.
One of the hacking tools leaked by the ShadowBrokers, codenamed ETERNALBLUE, exploits a vulnerability in older versions of Microsoft Windows. The spread of WannaCry is supported by computer code copied from ETERNALBLUE, which enables the ransomware to spread inside of vulnerable networks.
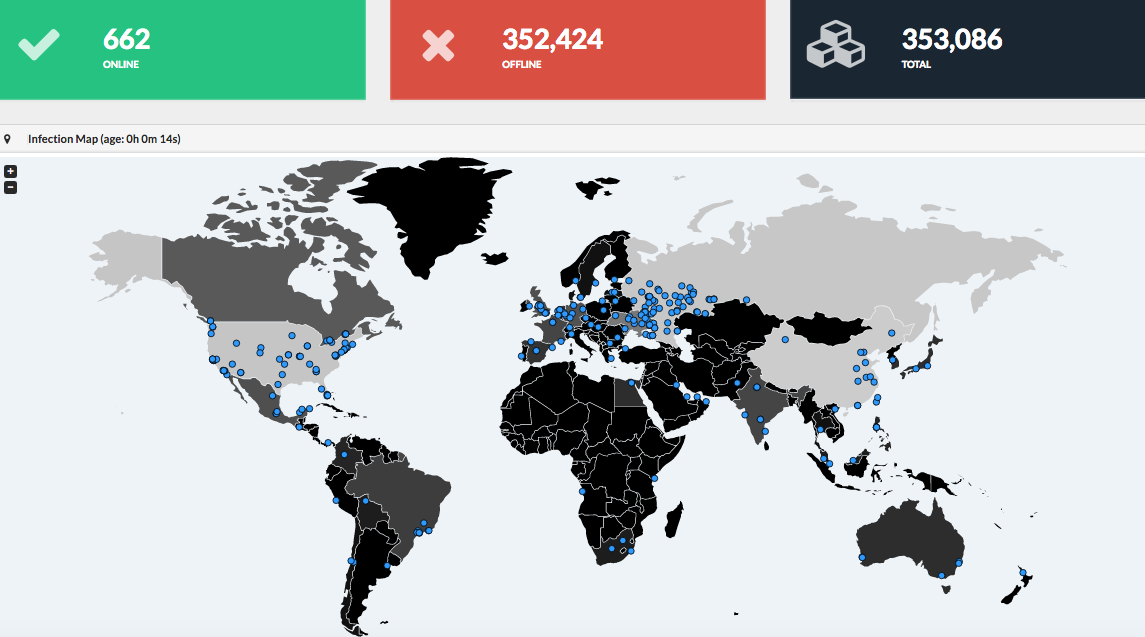
WannaCry tracker developed by MalwareTech (findings as of Tuesday 3pm)
While WannaCry has disrupted operations for a significant number of organizations based in Europe, officials say it remains largely under control in the U.S.
A official with Department of Homeland Security told reporters Tuesday that less than 10 U.S. organizations reported an infection to DHS.






