Security researchers and industry reps clash over voting machine security testing
Cybersecurity experts and voting machine makers are fighting over laws that would allow researchers to test for vulnerabilities and report them without fear of legal retribution.
Section 1201 of the 1998 Digital Millennium Copyright Act (DMCA) made it illegal to bypass security measures that prevent access to copyrighted material, such as software. Over the years, however, the U.S. Copyright Office has created exemptions to Section 1201 to grant “good-faith” hackers the ability to research consumer device security, such as cell phones, tablets, smart appliances, connected cars and medical devices.
Now, as the Copyright Office mulls expanding those exemptions to allow access to a broader array of technology — and voting machines in particular — security researchers and vendors are voicing their disagreements about the value of such an expansion. The office held a hearing fielding comments from stakeholders on Tuesday.
“A large fraction of security research really isn’t about devices that individual consumers are using but it’s about devices that are critical to business, to industry, to making the communications networks and the systems that we all rely on operate correctly and securely,” said University of Michigan professor and election security researcher J. Alex Halderman, a proponent of expanding the exemption.
Part of the hearing focused on whether simply getting permission from a voting equipment vendor would remove the need for an expansion of the DMCA exemptions. Proponents of an expansion argued that vendors historically haven’t been responsive to such requests. Steve Englund, a lawyer representing three election technology vendors, pushed back, saying that voting equipment already undergoes adequate security testing before being used in an election.
“In the election context, there are abundant opportunities for independent testing and consent when it’s to be had,” citing guidelines from the Election Assistance Commission that states and localities — which are responsible for administering elections — can choose to include in vendor contracts, as well as certification requirements that some jurisdictions implement.
Englund added that he was not aware of instances when states or localities wanted independent security researchers to test the security of their voting equipment, but were held back by the copyright terms of their supplier. Halderman took issue with that notion.
“There absolutely have been cases where local governments have wanted to conduct independent security testing on voting systems and have either been denied permission or have refrained from seeking permission because they were convinced it would be denied if sought,” Halderman said.
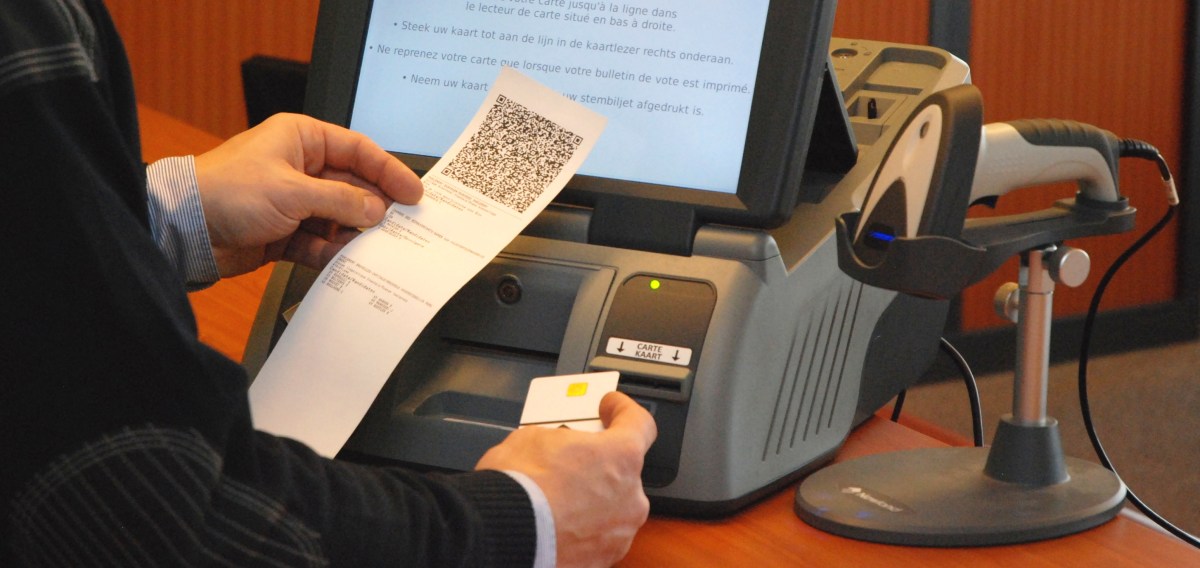
Independent researchers currently do investigate the security of voting machines, but the equipment is difficult to obtain, and researchers argue that there’s not enough assurance that they won’t run into copyright trouble because of their actions.
Blake Reid, a technology policy professor at the University of Colorado, said that the law as it exists creates uncertainty for researchers simply asking for permission from a vendor to test a product.
“The mere act of asking for permission might well be answered positively, but it might well be answered negatively. And it might well be answered so negatively that there’s a threat of a lawsuit,” Reid said.
Halderman and Reid sought to assure the panel of Copyright Office lawyers that independent researchers follow norms to make sure their hacking is under control such that it doesn’t harm the general public.
Christian Troncoso, policy director for the Software Alliance objected to that notion, saying that not all researchers are necessarily acting in good faith.
“Just because the researchers in this room abide by certain norms that would guided them in the construction of their research projects to mitigate harms to third parties doesn’t meant that every purported security researcher out there is doing the same thing,” Troncoso said.
Regan Smith, deputy general counsel for the Copyright Office, wanted to know from Englund whether vendors are incentivized on their own to secure their systems. Englund replied that his three clients — Dominion Election Systems, Election Systems & Software and Hart InterCivic — are competitors and therefore have an incentive to edge each other out.
Kit Walsh, an attorney with the Electronic Frontier Foundation, countered that vendors incentivized more so to shut good-faith hackers out.
“They’re discovering vulnerabilities and putting public pressure on the companies, too, to get them fixed. And when the election vendors … say they compete on security, that’s competing on the perception of security of their purchasers. And that’s kind of why there’s a financial interest from these companies not to allow their brand to be tarnished by truthful reporting about vulnerabilities in their software,” Walsh said.
The Copyright Office is in the midst of its triennial exemption process for DMCA Section 1201, involving several rounds of public comments and hearings for various topics. Later this year, the Copyright Office’s parent agency, the Library of Congress, will decide whether to issue any exemptions.
Last year, the office issued a report recommending that Congress amend Section 1201 to expand existing statutory exemptions for security and encryption research.





