Here’s how DHS prepared to keep hackers out of the Super Bowl

When the New England Patriots and Los Angeles Rams kick off in Atlanta on Sunday, a network of at least nine operational centers staffed by city, state, and federal officials will be humming with activity near the stadium to monitor for cyber and physical threats.
About 60 employees from the Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA) will be onsite — with a cyber official at each operational center — making it one of the biggest DHS cybersecurity operations at a Super Bowl to date.
“We really want everything to run smoothly,” Klint Walker, a DHS cybersecurity adviser in Atlanta, told CyberScoop, adding that the goal is to keep opportunistic attackers who would target a high-profile event “from making the newspaper.”
Walker was part of a team of DHS officials who worked through the 35-day partial government shutdown without pay to finish assessing and mitigating cybersecurity risk at the Super Bowl.
Asked how the stadium and its equipment suppliers are managing that risk, Walker said “the maturity level of all of the participants involved was above average,” reflecting many months of preparation.
Any conspicuous sporting event can draw the attention of hackers, and the tens of thousands of mobile devices at Mercedes-Benz Stadium on Sunday, for example, could be no exception. But officials say the stadium will be well prepared for and resilient to any advanced cyberthreats.
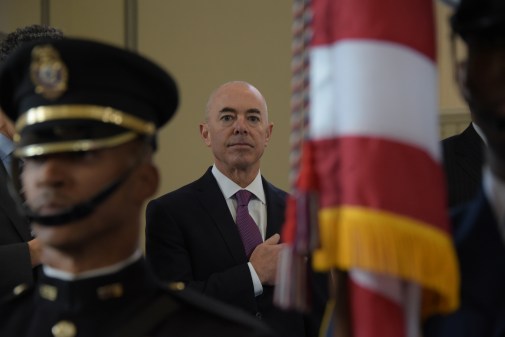
Brian Harrell, CISA’s assistant director for infrastructure security, said that, despite the funding lapse that came with the longest government shutdown in history, “we have always maintained our commitment to…providing federal resources and expertise during this highly visible, special security event.”
Harrell has been meeting with Georgia emergency management officials and representatives of Georgia Power, the utility keeping the lights on during the game.
Cybersecurity on the big stage
Sunday will be the culmination of over a year’s work by DHS and stadium officials to prepare for hacking and physical threats to the NFL’s biggest game. On the cybersecurity side, network scans, patching recommendations, and penetration-testing of software all play a part.
“Usually about nine months out, we’re really starting to jump in with our cyber assessments,” Walker told CyberScoop.
The department’s cybersecurity specialists conducted vulnerability scans of IT networks used at the stadium, and offered recommendations for making the venue more resilient to advanced attacks. Then there’s the fun part, at least for security geeks: penetration tests that probe computer networks and industrial control systems for weaknesses so they can be fortified.
Those technical assessments inform the centerpiece of the Super Bowl preparation, a series of tabletop exercises that are open to all the stakeholders, including local police, emergency responders, major hotels, and electricity providers. The drills practiced communication in the event of a security incident. About 100 people participated in the fourth and final tabletop before the game, according to Walker.
The Super Bowl is likely the biggest cybersecurity operation for CISA since it got rebranded in November to a name that reflects its mission and that the public can understand (replacing the clunkily named National Protection and Programs Directorate). Officials who have been putting in the legwork in Atlanta for months say the agency is ready for the test.