‘Five Eyes’ nations release technical details of Sandworm malware ‘Infamous Chisel’
The U.S. government and its allies on Thursday released a technical breakdown of malware used by the infamous Russian hacking group Sandworm on the battlefield in Ukraine, offering one of the most detailed analyses to date of malicious software used by the Kremlin in military cyber operations against Kyiv.
The joint alert by the Cybersecurity and Infrastructure Security Agency, the National Security Agency, the FBI, and agencies in the Five Eyes intelligence partnership — made up of the United States, the United Kingdom, New Zealand, Canada, and Australia — provides a detailed analysis of malware dubbed “Infamous Chisel,” which the Sandworm hacking group deployed against Android devices belonging to Ukrainian service members in a bid to collect battlefield intelligence.
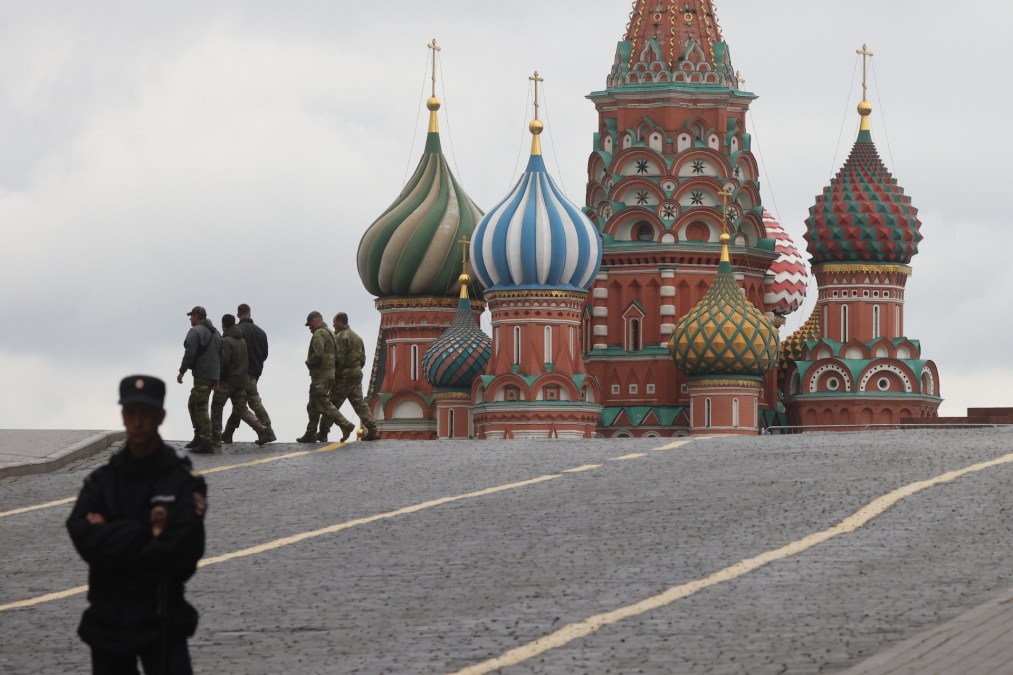
Use of the malware has been described by Ukrainian officials as a shift in Russia’s use of cyber operations against Ukraine, from disruptive attacks to more targeted collection to help on the battlefield. Sandworm operates from within the Russian Main Intelligence Directorate, or GRU, and is perhaps best known for the cyber attacks against Ukraine’s grid in 2015 and 2016 that disrupted power in the middle of winter.
Infamous Chisel targets Android devices through a collection of components that ensures persistent access over the Tor network while also collecting information. The malware exfiltrates data that matches a predefined list of extensions like .jpeg and .txt, among others. Additionally, the malware looks for system information, scans the local network for active hosts and open ports, as well as looks for specific Ukrainian military applications. Those military applications were not detailed in the report.
Ukraine’s security services first attributed the campaign to Russia in an August report. The report noted that Russia took tablets used by Ukrainian soldiers for use in further penetrating their defenses.
While Sandworm is widely known for the sophisticated malware used in its attacks on the Ukrainian grid and the more recent NotPetya malware, Infamous Chisel is described by Five Eyes cybersecurity agencies as “low to medium sophistication” and appeared to give little thought to avoiding detection, the report notes.
“The searching of specific files and directory paths that relate to military applications and exfiltration of this data reinforces the intention to gain access to these networks. Although the components lack basic obfuscation or stealth techniques to disguise activity, the actor may have deemed this not necessary, since many Android devices do not have a host-based detection system,” the report reads, meaning there are few ways to monitor the Android devices for malicious behavior.
Even so, the alert warns that the apparently lax concealment methods does not mean that the malware isn’t dangerous. The information gleamed from exfiltration could give Russia an advantage on the battlefield at a time when Ukraine is on the counteroffensive against Russian positions.






