Russian military intelligence may have deployed wiper against multiple Ukrainian ISPs

The updated version of the malware used by Russian military hackers to hobble thousands of modems linked to the Viasat internet and satellite communications company at the onset of the Russian invasion may have been used in attacks on four Ukrainian internet service providers, researchers said Thursday.
A group calling itself “Solntsepek” claimed credit on March 13 for disruptive attacks on four Ukrainian internet service providers: Triacom, Misto TV, Linktelecom and KIM, claiming that they “provide Internet to government agencies, parts of the Armed Forces of Ukraine, as well as the TCC,” according to a machine translation of the message posted to the group’s Telegram channel.
Solntsepek — an apparent hack-and-leak front controlled by Russian military intelligence (GRU) — claimed responsibility for a major attack on Kyivstar, Ukraine’s largest telecommunications provider, in December. Illia Vitiuk, the head of the Security Service of Ukraine’s (SBU) cybersecurity department, said at the time that the attack had been carried out by the Russian military intelligence hacking unit known widely as Sandworm.
Juan Andrés Guerrero-Saade and Tom Hegel, researchers with SentinelOne’s SentinelLabs, first identified on Monday what’s likely an updated version of AcidRain, the malware used by the Russian military to disable thousands of KA-SAT modems associated with Viasat as the country’s armed forces invaded Ukraine on Feb. 24, 2022. The new variant, dubbed “AcidPour,” displayed an expanded set of capabilities and potential targeting capability.
Guerrero-Saade and Hegel said in a blog post published Thursday that although targeting and impact is inconclusive, “indications suggest disruption on multiple Ukrainian telecommunication networks, which have reportedly been offline since March 13th.”
The State Service of Special Communications and Information Protection of Ukraine, responsible for network defense, declined to comment on the matter. The SBU, an intelligence and law enforcement agency, did not respond to a request for comment.
Doug Madory, the director of internet analysis for Kentik, posted a message to the X social media platform Wednesday showing major disruptions to the companies’ web traffic beginning March 13, and slowly recovering in the following days.
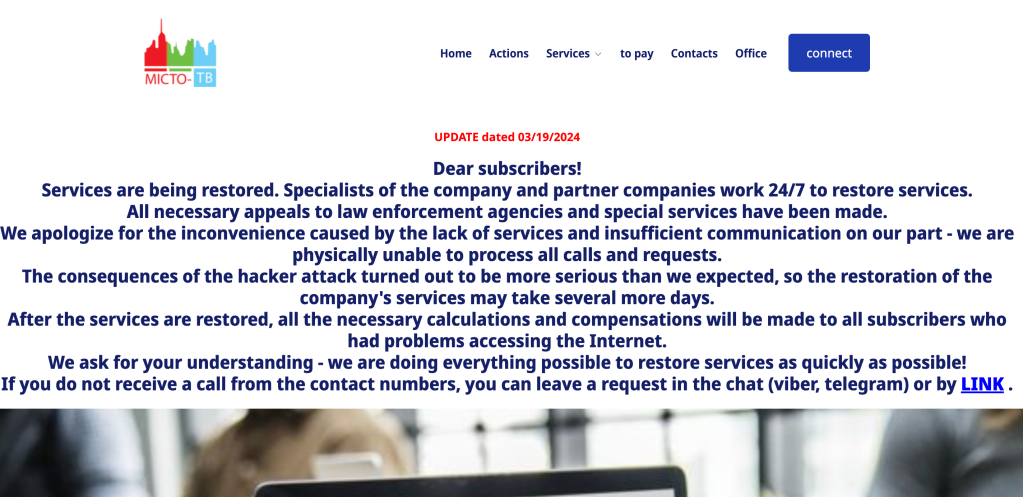
A message posted to the homepage of Misto TV on Tuesday said that services were being restored and that “the consequences of the hacker attack turned out to be more serious than we expected,” according to a machine translation of the message.
The advent of AcidPour is concerning because it could be used as part of a “larger service disruption by Russia” and wipe the contents of not only modems, but a range of other devices, Hegel told CyberScoop on Monday. Rob Joyce, the outgoing director of cybersecurity at the National Security Agency, called AcidPour “a threat to watch” in an X post Tuesday.
The updated version of the malware discovered March 16 was much more concerning, Hegel said, because it could be used to target memory in embedded devices — components within larger systems — “which could be used for a different level of impact” and make attacks “even more difficult to prevent and recover from.”
“Embedded devices are particularly concerning as they often serve critical needs yet lack simple detection and recovery options if they were to be wiped,” he added, noting that he would expect it to have been deployed to “many devices.”
A representative of the State Service of Special Communications and Information Protection of Ukraine confirmed to CyberScoop early Tuesday that they were aware of AcidPour and “its repetitive usage against targets within Ukraine.” The malware was the work of a unit the Ukrainians track as UAC-0165, which is a sub cluster of activity tracked under the broader Sandworm umbrella, the agency told CyberScoop.
UAC-0165 has repeatedly attacked Ukrainian telecommunications entities, the country’s Computer Emergency Response Team (CERT-UA) said in an October 2023 message that detailed attacks on at least 11 companies.
Solntsepek’s Telegram channel, launched in April 2022, details repeated attacks on a variety of victims, including multiple telecommunications-related entities.






