A look inside Russian cybercrime syndicate TrickBot reveals an organized, potent adversary

On Feb. 21, just days before Russia launched its brutal invasion of Ukraine, someone with the username “fire” posted a message to one of the TrickBot cybercrime syndicate’s internal chat groups.
“We are in a difficult situation,” fire wrote in an attempt to explain to others why they hadn’t been paid, and to ask for their patience. There had been “too many leaks,” among other circumstances, so “the boss has apparently decided to lay low.”
Fire added that the future of the group was bleak. “There is no boss, no clarity or certainty about what we will do in the future, no money either.”
The message was just one of roughly 250,000 communications analyzed by British cybersecurity firm Cyjax as part of a report published Friday that offers a detailed look at the inner workings of TrickBot, which refers to both a sophisticated trojan malware and the developers behind it.
The @trickleaks Twitter account originally post the messages in batches. Its Twitter bio claims to “have evidence of FSB’s cooperation with members of the Trickbot criminal group (Wizard Spiders, Maze, Conti, Diavol, Ruyk).”
The Cyjax report highlights the highly structured nature of the major Russian cybercrime group, a key reason they are able to generate tens of millions of dollars annually. The leaks also revealed reams of information about TrickBot members, Cyjax Intelligence Analyst Joe Wrieden wrote, including “where they are based, what real jobs they have held in the criminal organisation and commercial world as well, and in some cases, why the member joined the group.”
But while the leak may have been a blow to the criminal cyber syndicate, and revealed the trouble in the group in the aftermath of the invasion, researchers say that TrickBot continues to be a menace, especially in Ukraine.
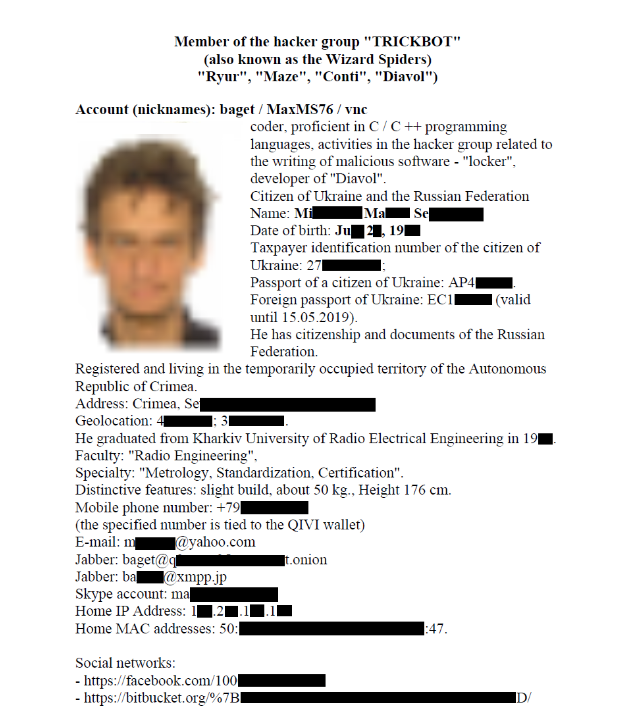
The group behind the @trickleaks account posted PDFs with detailed biographical information on alleged TrickBot members, which included full names, addresses and other personal information from a likely mix of open-source information and internal data held by TrickBot. Cyjax was able to download 27 such PDFs before they were deleted from the hosting service where they were posted.
Wrieden questioned why so much information was available on some of the group’s members. “Perhaps these cybercriminals are aligned, affiliated, or controlled by a nation state protagonist which required this information,” Wrieden wrote.
Altogether, he added, the leak is “over four times the size of the Conti leaks which was seen by some researchers as one of the most useful information dumps of the past few years.”
Both the Conti leaks and the TrickBot leaks came about after Conti posted a message to its website pledging full support for the Russian government as it waged its assault on Ukraine. Conti, like other major cybercrime groups, is thought to operate out of Russia or in a Russian-friendly country, and did not attack Russian targets as a matter of policy.
Conti quickly walked back its message, but the damage was done in the eyes of some of its Ukrainian and other non-Russian members. A Ukrainian researcher with access to Conti’s infrastructure leaked the Conti materials, but it’s unknown who is behind the TrickBot leaks, the reports authors said.
Conti would go on to continue attacking targets for the next few months, and TrickBot was thought to be shutting down its infrastructure, researchers concluded in late February, just the latest time the group was believed to be dead.
But on July 7, IBM’s Security X-Force research group published findings suggesting the TrickBot syndicate had been “systematically attacking Ukraine” in the wake of the Russian invasion as part of “an unprecedented shift” that reflected some members allegiance to Russian goals.
“Wizard Spider is a business. And while the Conti leaks did a lot to disrupt one part of their business [Conti ransomware], other parts, like TrickBot, have continued to operate,” said Allan Liska, an intelligence analyst at cybersecurity firm Recorded Future.
Wrieden concluded that the leaks’ value is helping to understand what modern high-level cybercrime actually looks like.
“The threat we face today is often depicted as hundreds of individual groups, each with different tactics, techniques, and procedures vying for money and notoriety,” he wrote. “From what we have seen, it appears this claim is highly exaggerated.”

This story was featured in CyberScoop Special Report: War in Ukraine






