Russia’s digital warriors adapt to support the war effort in Ukraine, Google threat researchers say

Russian and pro-Russian operatives continue to modify their hacking and influence operations aimed at Ukraine to extract intelligence and sway public opinion in favor of the war, Google researchers said in a report released Wednesday. The latest tactics include promoting highly produced YouTube videos as well as more traditional phishing campaigns.
Roughly 14 months after the Russian invasion of Ukraine, the cyber components of the Russian onslaught continues with nearly 60% of Russian-backed phishing campaigns targeting Ukraine, Billy Leonard, a security engineer with the Google Threat Analysis Group, wrote in an update on the most notable hacking campaigns the company observed between January and March of 2023.
The latest report includes new information operations from Russia’s elite hacking units as well as work from a group believed to be Belarusian, a staunch Russian ally. From traditional credential and intelligence gathering efforts to information operations aimed abroad and at Russian audiences to glorify war efforts, the ongoing cyber operations remain active and show signs of adaptations and new techniques, Leonard wrote.
One of Russia’s most prolific and elite hacking groups — known widely as Sandworm, but tracked by Google as FROZENBARENTS — “continues to focus heavily on the war in Ukraine with campaigns spanning intelligence collection, IO, and leaking hacked data through Telegram,” Leonard wrote. Believed to operate out of Russian Armed Forces’ Main Directorate of the General Staff, or GRU, Unit 74455, the group known best for its multiple successful Ukrainian power grid attacks and the NotPetya malware that racked up more than $10 billion in global damages maintains its perch atop the Russian-backed offensive hacking ecosystem.
“FROZENBARENTS remains the most versatile GRU cyber actor with offensive capabilities including credential phishing, mobile activity, malware, external exploitation of services, and beyond,” Leonard wrote. “They target sectors of interest for Russian intelligence collection including government, defense, energy, transportation/logistics, education, and humanitarian organizations.”
The group continues to exploit EXIM mail servers around the world, Leonard wrote, a tactic it has employed since 2019, according to a 2020 NSA advisory. Once compromised, the hosts have been observed “accessing victim networks, interacting with victim accounts, sending malicious emails, and engaged in information operations (IO) activity.”
FROZENBARENTS has also continued to target organizations associated with the Caspian Pipeline Consortium (CPC), one of the largest oil pipelines in the world that transports crude oil from Kazakhstan across Russian territory to the Black Sea, Leonard wrote. The group has targeted a range of unnamed Eastern European energy sector organizations using fake Windows update packages on a domain spoofing CPC that, if executed, loaded a variation of the Rhadamanthys malware that could then exfiltrate stored credentials, including browser cookies.
Dating back to December 2022, the group has also “launced multiple waves” of credential theft campaigns targeting Ukrainian defense industry, military and Ukr.net mail users, Leonard wrote.
The group has also been active in the information operation space, he said, creating online personas to push pro-Russian news and narratives and leak stolen data, Leonard wrote, such as the persona CyberArmyofRussia, or CyberArmyofRussia_Reborn.
Both the YouTube channel for CyberArmyofRussia, or CyberArmyofRussia_Reborn — which was pulled down upon notification — and the Instagram account had minimal engagement and a “negligible number of subscribers or followers,” Leonard wrote. The group’s Telegram channel, launched April 1, 2022, remains robust, with frequent posts for nearly 23,000 subscribers. Google researchers assess that the channel was created and controlled by the elite hacking unit.
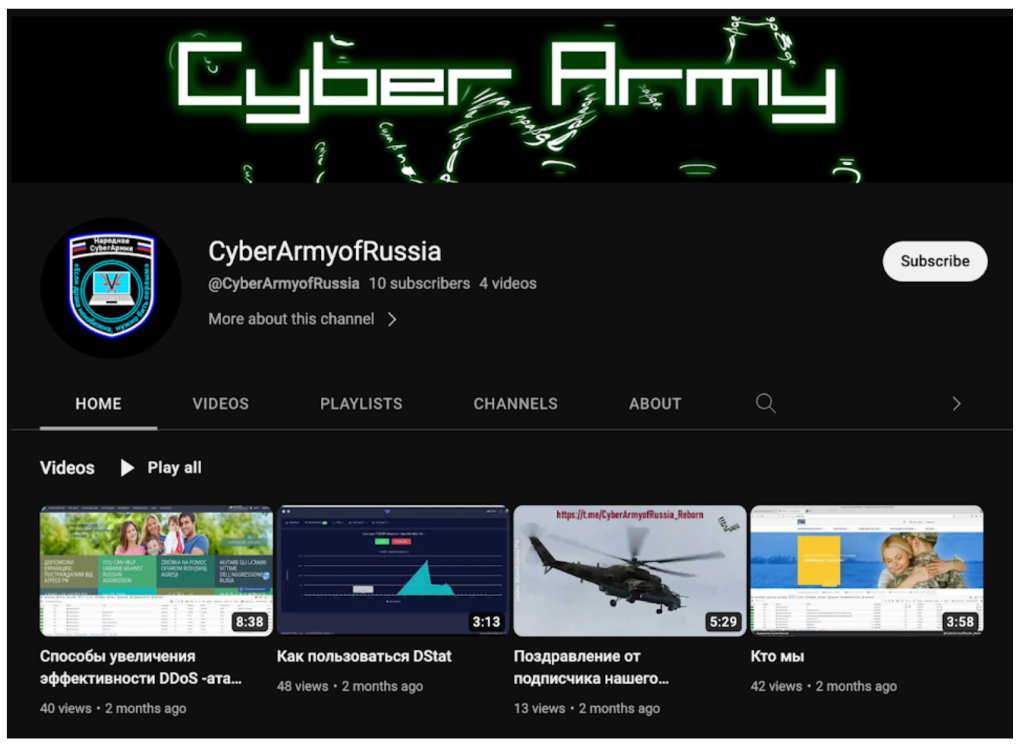
“In several recent incidents, FROZENBARENTS compromised a webserver of the target organization and uploaded a webshell to maintain persistent access to the compromised system,” Leonard wrote. “The attackers then deployed Adminer, a single file PHP script for managing databases, to exfiltrate data of interest. Shortly after exfiltration, the data appeared on the CyberArmyofRussia_Reborn Telegram channel.”
In another information operation, the Internet Research Agency — notorious for its efforts to shape domestic U.S. opinion ahead of the 2016 presidential elections — produced a series of YouTube Shorts, short-form videos akin to TikTok or Instagram’s Reels. “The group has focused particularly on narratives supportive of Russia and the business interests of Russian oligarch Yevgeny Prigozhin, especially the Wagner Group,” Leonard wrote.
The U.S. Department of Justice indicted Prigozhin, a longtime associate of Russian President Vladimir Putin, in 2018 for his role in the IRA interference operation. He is currently wanted by the FBI.
“The group was also promoting a new film by Aurum LLC, a film company partially owned by Prigozhin. This movie has a high production value and communicates narratives portraying the Wagner Group in a positive light,” Leonard wrote.
Promotion for movie film about the Wagner Group (Google Threat Analysis Group).
Altogether, “Moscow continues to leverage the full spectrum of information operations–from overt state-backed media to covert platforms and accounts–to shape public perception of the war in Ukraine,” Leonard wrote.
Smaller campaigns from other hacking groups caught Google’s eye as well.
Another operation — attributed to the GRU as well but perhaps a unit other than FROZENBARENTS — has since April 2022 “maintained a Telegram channel to promote and amplify narratives related to the use of biological weapons in Ukraine and how the United States is responsible for the proliferation of biological weapons around the world,” Leonard wrote. This campaign involves a Russian-language Telegram channel and an English Substack newsletter, which has published only once.
APT28 — known widely as Fancy Bear, and tracked as FROZENLAKE — sent “multiple large waves of phishing emails to hundreds of users in Ukraine” in February and March, Leonard wrote. Part of the effort involved reflected cross-site scripting (XSS) on multiple Ukrainian websites, which represents a new tactic for the group.
A Belarusian-linked hacking campaign — tracked as PUSCHA by Google but sometimes called UNC1151 and linked to Belarus by Mandiant in November 2021 — has “consistently targeted users in Ukraine and neighboring countries throughout the war,” Leonard wrote, typically targeting the i.ua and meta.ua webmail services. Leonard described the phishing campaigns as “targeted,” and “focused on small numbers of users in Ukraine.”




