
So much of the dark web leaves enterprises, well, in the dark.
Unless a security team has someone infiltrating and scouring hacker forums, it’s hard to get a handle on how much money adversaries are spending on the latest exploits.
We’ve seen tons of stories on exorbitant price points for first-class zero-days, but attackers don’t need to shell out Rolls Royce prices for every remote code execution on the market.
In order to give enterprises a better look at what attackers are paying for, CyberScoop has teamed up with McLean, Virginia-based RunSafe Security to bring you the RunSafe Pwn Index.
Think of it as the Dow Jones Industrial Average for dark web exploits: Every quarter, RunSafe examines multiple sources of exploit data, including dark web marketplaces, payout services and private practitioners. From the zero-day pricing data it collects, RunSafe then creates a weighted average price based on the target platform and exploit type. Those prices are then averaged to form the overall RunSafe Pwn Index.
We want this index to serve as an indicator of what exploits are popular among attackers aiming at enterprise and government agency software assets, and how the prices and quantities of those exploit shift over time.
“The market for zero-days and malicious exploits is constantly evolving. The price and volume of transactions for a given exploit represent a leading indicator on how enterprises and government agencies should think about the next attack,” said Joe Saunders, CEO of RunSafe Security. “In illuminating hacker economics via the RunSafe Pwn Index, we want to raise awareness that newer defenses focusing on prevention regardless of the exploit, such as binary stirring and moving target defenses, ultimately disrupt the hacker economics rendering exploits inert. ”
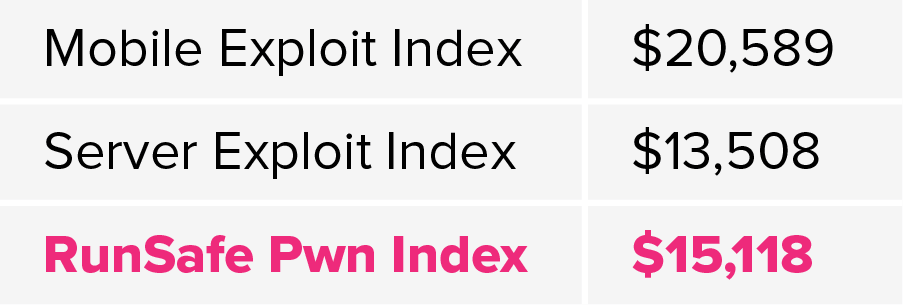
For the introductory index, mobile exploits exceeded the server exploits, primarily due to what attackers are after on mobile devices: user data. Among mobile exploits, the highest payout are going to remote code execution aimed at Apple’s iOS.
“Given Apple’s closed system, the company’s tight security efforts and the demographics of its customers, gaining access is a premium service that few attackers can achieve,” RunSafe researchers told CyberScoop. “The scarcity of the supply of exploits drives the price up.”
There are several current factors that are probably causing mobile vulnerabilities to trend higher. A recent security updated from Apple squashed a widely publicized FaceTime bug that allowed attackers to spy on others via audio and video. It also fixed two zero-day vulnerabilities that would have allowed attackers to gain elevated privileges, and execute arbitrary code with kernel privileges.
Additionally, attackers are shopping around for both remote code execution and local privilege execution when it comes to messaging apps, as they provide a way to inject further malicious code onto a mobile device.
On the server side, virtual machine escape — an exploit that allows an attacker to break out of a virtual machine and interact directly with a host operating system — are popular among attackers. Proprietary deployments such as VMWare, HyperV, Oracle VirtualBox all have flaws that are often left unpatched, so attackers buy up exploits that take advantage of enterprises who haven’t fixed those flaws.






