First in space: SpaceX and NASA launch satellite that hackers will attempt to infiltrate during DEF CON

On Monday at 11:47 a.m. at the Kennedy Space Center in Florida, for the first time ever, SpaceX and NASA sent a satellite into low-earth orbit hoping that it’ll get hacked.
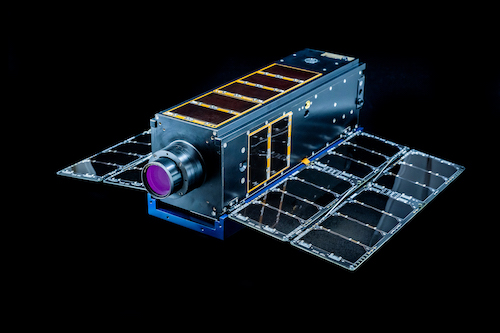
Several small square-shaped satellites called cubesats were strapped to the SpaceX rocket launched for a resupply mission to the International Space Station. One of those cubesats — called Moonlighter — will be used as an experimental “hacking sandbox.” Security researchers will use that sandbox as part of a competition taking place at the annual DEF CON hacking conference in Las Vegas later this year. Teams will attempt to infiltrate it all in the service of identifying vulnerabilities in satellites to improve cybersecurity in space.
A collaboration between The Aerospace Corporation, the Air Force Research Laboratory and U.S. Space Systems Command, Moonlighter represents the latest iteration of the Hack-A-Sat competition. The Air Force has hosted Hack-A-Sat since 2020 as a multi-year effort to increase collaboration with cybersecurity researchers, but the past three capture-the-flag contests have all been simulations.
This year they wanted to take the competition to a whole new level. “We wanted a vehicle where the sole purpose was to understand how to do cyber operations in space,” said Aaron Myrick, senior project engineer at The Aerospace Corporation.
Securing space systems has become more of a focus for the space industry and the Biden administration as experts are growing increasingly alarmed about new commercial off-the-shelf products with potential vulnerabilities. Just last week, experts in the field launched a worldwide effort to create voluntary technical standards through the Institute of Electrical and Electronics Engineers to better secure commercial products by design.
“We’re really trying to wrap our heads around cybersecurity operations and how do we do cyber operations on a system that is starting to have a lot more commoditized hardware and software, but it’s also extremely remote,” said Myrick. “We can’t just go up there and flip the power switch or change a hard drive … it’s quite a challenging problem.”
Earlier this year, the White House held a space cybersecurity summit with some of the biggest players. Additionally, CSC 2.0 —a continuation of the congressional Cyberspace Solarium Commission — called for space systems to be designated as critical infrastructure.
While cyberattacks against space systems may not be common, the potential consequences for an attack was most recently seen during the start of the Russian invasion after state-backed hackers targeted U.S.-based Viasat’s satellite modems. The attack was aimed at impacting Ukrainian command and control during the start of the invasion, but also included cascading impacts that spread to thousands of German wind farms and satellite internet connections across Europe.
Myrick said the space industry understands many of the physical risks associated with space such as harsh radiation levels, but cybersecurity still presents many challenges that experts are just beginning to resolve. While simulating cyberattacks in a real-world environment will be helpful, Myrick explained, it won’t answer every question about how satellites could be affected in an attack outside the test environment.
“Moving to on-orbit actually introduces a lot of challenges, but it removes a lot of the sims you build into it,” Myrick said. For example, satellites actually spend much of their time disconnected from an operation center and are fairly automated, adding additional layers of complexity, Myrick said. Operators may simply not have full knowledge of what is impacting those space systems at particular periods of time.
Test-beds such as Hack-A-Sat allow for researchers to discover how hackers target networks in space systems they may not be familiar with, which will be mapped to a space-centric attack framework called SPARTA.
There will be limits to just how far Hack-a-Sat contestants can go. They will be able to hack at the Moonlighter’s cyber payload while in-orbit, but won’t be able to change the orbit.
“We are designing the flight software for the cyber payload to basically be able to operate the vehicle fully. So it will be able to change how the vehicle is pointed,” Myrick said. “There’s no orbit changes. That’s all pretty fixed, but where that vehicle was pointed that ability will be there.”
Myrick said that the Moonlighter has a supervisory layer that can shut off the cyber payload so if something “inevitably” goes wrong, they can “figure out what went wrong and how we can be better.”
Five teams have made to the finals at DEF CON this August to compete for the $50,000 grand prize.






