Microsoft seizes infrastructure of top cybercrime group

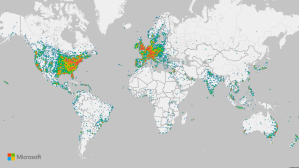
Microsoft took sweeping action against a cybercrime operation responsible for creating roughly 750 million fraudulent Microsoft accounts and various websites used to enable a bevy of cybercrime activities, the company said Wednesday.
The announcement comes nearly a week after Microsoft obtained a court order from the Southern District of New York allowing it to seize U.S.-based infrastructure and websites used by a group the company tracks as Storm-1152. The group is one of several that “enable scores of cybercriminals to carry out their malicious activities more efficiently and effectively,” Amy Hogan-Burney, Microsoft’s associate general counsel for cybersecurity policy and protection, wrote in a blog post on the company’s website.
The group “plays a significant role in the highly specialized cybercrime-as-a-service ecosystem,” Hogan-Burney wrote, offering fraudulent Microsoft accounts as well as services to bypass CAPTCHA puzzles, which are designed to reduce inauthentic, spammy behavior by forcing a human to answer questions or solve puzzles to access certain web services. Microsoft described the group as “the number one seller and creator of fraudulent Microsoft accounts.”
The investigation also identified several individuals based in Vietnam that Microsoft said were instrumental in developing and maintaining the websites associated with the activity, producing step-by-step videos explaining how to use their products to exploit fraudulent Microsoft accounts and even providing chat services to customers.
Storm-1152’s activities generated “millions of dollars in illicit revenue” and cost Microsoft and other companies “even more to combat their criminal activity,” Microsoft wrote. The company has submitted a criminal referral to U.S. law enforcement, Hogan-Burney wrote.
Microsoft researchers identified multiple groups engaged in ransomware, data theft and extortion that have used Storm-1152 accounts, she added, including Scattered Spider, the industry term for a loose collection of financially-motivated, youth-led hacking groups perhaps best known for successfully hacking MGM Resorts and Caesar’s Entertainment in September.
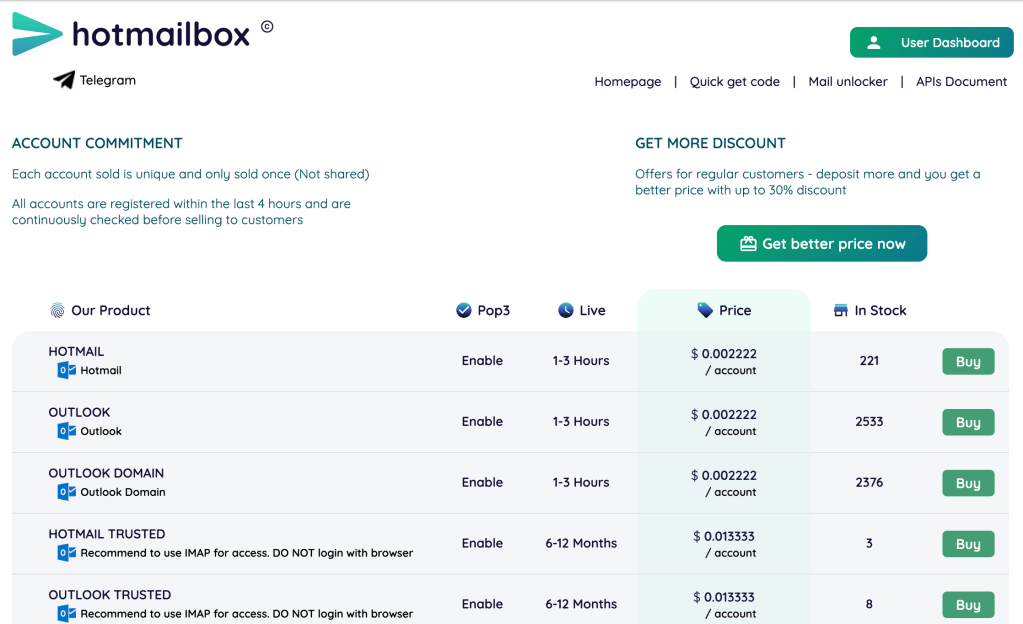
The court order allowed Microsoft to seize hotmailbox[.]me, a site that sold Microsoft accounts from around the world. A snapshot of the site captured December 7 and available via the Internet Archive offered accounts for sale for a fraction of a cent each.
“Each account sold is unique and only sold once (Not shared),” the webpage read. “All accounts are registered within the last 4 hours and are continuously checked before selling to customers.”
“With companies able to quickly identify and shut down fraudulent accounts, criminals require a greater quantity of accounts to circumvent mitigation efforts,” Hogan-Burney wrote. Instead of laboriously creating email accounts themselves, cybercriminals can simply purchase them in bulk from entities such as Storm-1152.
“This allows criminals to focus their efforts on their ultimate goals of phishing, spamming, ransomware and other types of fraud and abuse,” she wrote.
The actions also disrupted 1stCAPTCHA, AnyCAPTCHA and NoneCAPTCHA, according to Microsoft.
Microsoft collaborated with Arkose Labs to research and take actions against the group.