Microsoft identifies new hacking unit within Russian military intelligence

On Jan. 13, 2022, about five weeks before Russia’s full-scale invasion of Ukraine, Russian hackers carried out one of the first cyberattacks in the run-up to the conflict.
Posing as ransomware, the malware worked in two stages: First, it would overwrite the master boot record with a ransom note, pointing victims to a bitcoin wallet and demanding a relatively paltry $10,000 to recover corrupted files. Then it would download and deploy file corrupter malware, targeting files in particular directories to be overwritten. But the operation was a ruse: There was no way to recover the files.
Two days after the malware was deployed, Microsoft researchers published an analysis of the destructive tool, dubbing it WhisperGate. By May, officials in Ukraine, the United States and the United Kingdom attributed the attack to units working under Russian Main Intelligence Directorate (GRU).
A year later, Microsoft researchers have determined that the unit behind that attack is an active and distinct group within the GRU, responsible for website defacements, destructive attacks, cyber espionage and hack-and-leak operations. In a report published Wednesday, Microsoft concludes that a group it is calling “Cadet Blizzard” is behind a wave of attacks since February 2023 targeting not only Ukraine, but also NATO member states providing military assistance to Ukraine.
Wednesday’s report for the first time identifies the activity as distinct and novel from other GRU-affiliated cyber operations, which includes the group widely tracked as Sandworm and believed to be responsible for multiple attacks on Ukraine’s electric grid in recent years. Hacking operations linked to the GRU are considered among the most destructive and potent in the Russian-affiliated hacking ecosystem.
“The emergence of a novel GRU affiliated actor, particularly one which has conducted destructive cyber operations likely supporting broader military objectives in Ukraine, is a notable development in the Russian cyber threat landscape,” the researchers said Wednesday, while noting that the group’s attacks are generally less successful than more sophisticated and prolific Russian hacking groups, such as Sandworm.
Russian hacking groups have either refrained from or failed to carry out spectacular cyber attacks targeting Ukrainian critical infrastructure as part of the Kremlin’s attempt to overthrow the government in Kiev. But Russian hacking groups have nonetheless remained active in the conflict, carrying out attacks to wipe Ukrainian computer systems and carry out information operations — the type of action that is emblematic of Cadet Blizzard.
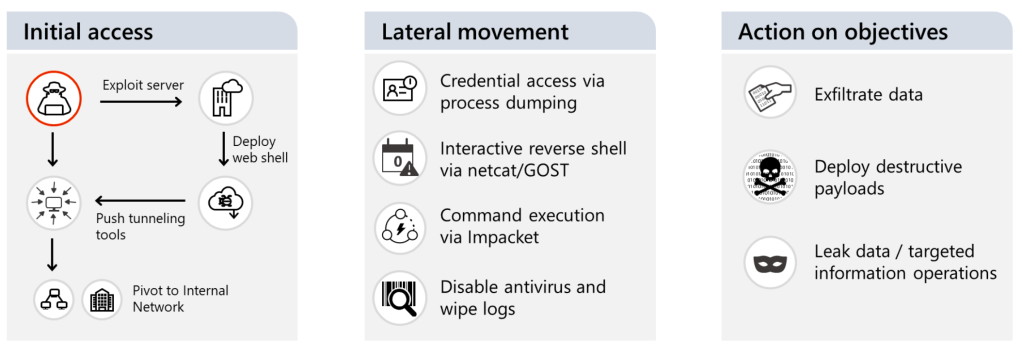
Dating to at least 2020, Cadet Blizzard’s activity includes attacks around the world — in Europe, Latin America and Central Asia — with a particular focus on government services, law enforcement, nonprofits/NGOs, IT service providers and emergency services, the researchers said. The group has consistently targeted IT and software providers, the researchers added, given that one successful attack can lead to multiple downstream compromises.
Microsoft characterizes the group as a conventional network operator that works without bespoke malware or tooling. “Unlike other Russian-affiliated groups that historically prefer to remain undetected to perform espionage, the result of at least some notable Cadet Blizzard operations are extremely disruptive and are almost certainly intended to be public signals to their targets to achieve the larger objective of destruction, disruption, and possibly, intimidation,” the researchers noted.
Cadet Blizzard’s activity overlaps with other cyber operations that “may have a broader scope or a nexus outside of Russia,” including connections to a group Microsoft tracks as Storm-0587, denoting an unattributed activity. That group is linked to malware known as SaintBot, a downloader that can be configured to deliver nearly any other payload. Cadet Blizzard also has support from “at least one private sector enabler organization within Russia,” the researchers noted.
The group uses a hacktivist front called “Free Civilian” to publish and share stolen data, according to the report. Free Civilian posted and leaked stolen Ukrainian government data from various sources on its website in January 2022 ahead of the invasion. The organizations whose data was leaked “strongly correlated to multiple Cadet Blizzard compromises earlier in 2022,” the researchers said, suggesting “that this forum is almost certainly linked to Cadet Blizzard.”
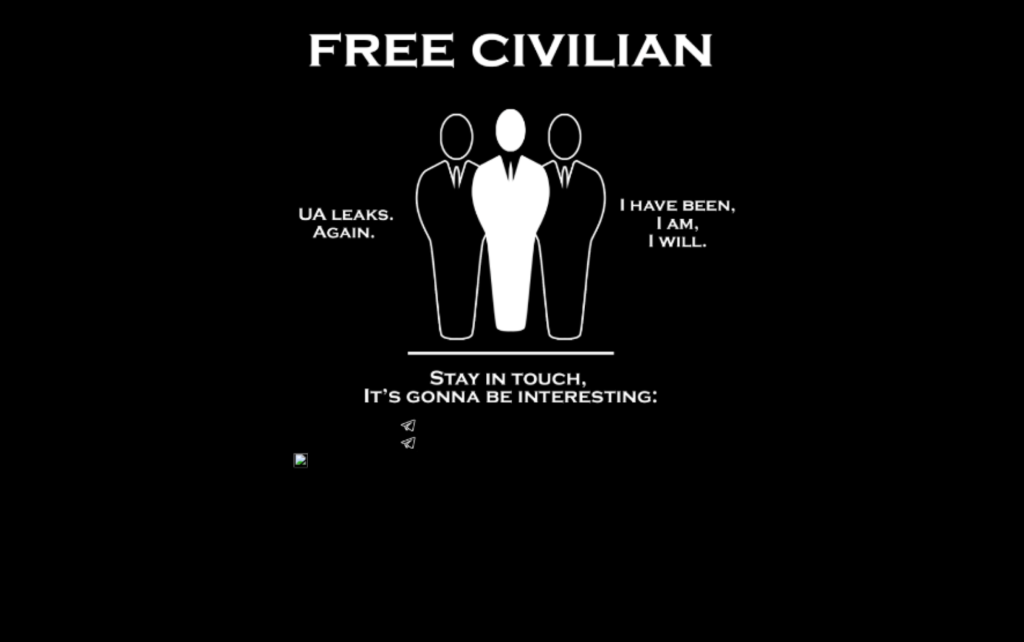
On Feb. 21, 2023, the Free Civilian launched a Telegram channel. The next day, a post in Russian began: “Hello, long time no see,” followed by promises of data from a range of Ukrainian government agencies and a message mocking Ukraine’s Cyber Police and its security service.
The channel has continued to post stolen data and references to stolen data, including as recently as April 26. The channel had just more than 1,300 subscribers as of Wednesday, with most posts “getting at most a dozen reactions as of the time of publication,” the researchers said, “signifying a low user interaction.”
A separate private channel likely operated by the group offers access to stolen data. The administrators of that channel have to manually approve requests to join, and as of Wednesday the channel had 779 members.