Kaseya obtains decryption key for victims of massive ransomware attack
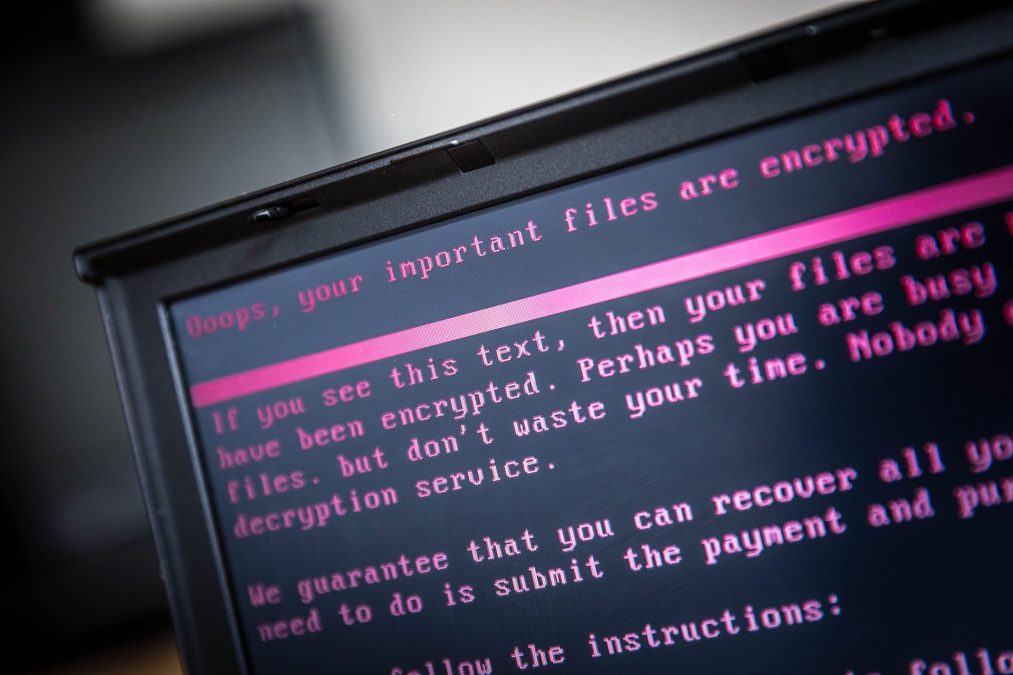
Roughly three weeks after Russia-based ransomware group REvil attacked Kaseya, the Florida-based IT firm has obtained a working decryption key to unlock encrypted files belonging to hundreds of victims, a spokesperson confirmed to CyberScoop on Thursday.
Dana Liedholm, the company’s senior vice president of marketing, declined to comment on the source of the key, other than to say it came from a “trusted third party.” She also declined to comment when asked if the company had paid to obtain the key, or and on long it would take to remediate all the clients that had been impacted by the attack.
Security firm Emisoft confirmed in a blog post that the decryptor works and it has been working with customers to restore their files.
The news of the decryption tool was first reported by NBC’s Kevin Collier.
Kaseya has estimated the number of affected companies at somewhere between 800 and 1,500. Private cybersecurity firms have suggested a higher figure, as Huntress Labs estimated the number of victims at closer to 2,000. Sophos Labs identified 145 victims in the United States, including local and state agencies, governments, and small and medium-sized businesses.
Hackers exploited a Kaseya platform that’s used by managed service providers, or companies that provide third-party IT service to other organizations. Because these companies have administration privileges with their clients, the number of victims quickly spiraled beyond Kaseya and its direct customers.
Among the victims are New Zealand schools, international textile company Miroglio Group, Swedish grocery store chain COOP, and two Maryland towns.
The tool may come too late to help some victims, however.
“For almost three weeks now, managed service providers and small to medium businesses have been working overtime to recover and restore systems. After recovery efforts, a universal decryption key would have helped retrieve data that wasn’t restored correctly,” John Hammond, a senior security researcher at Huntress wrote to CyberScoop in an email. “With the weeks that have gone past since the beginning of this incident, perhaps this universal decryptor is just too little too late.”
Huntress was one of the first firms to identify the attack.
The attack, which occurred just before the Fourth of July weekend, roiled tensions between Washington and Russia, which is suspected of harboring cybercriminals. Russia has denied any involvement in the incident.
The White House has not formally pinned the attack on REvil, the same group behind a May breach at international meat supplier JBS.
Shortly after demanding a $70 million dollar ransom from Kaseya, the group’s online presence went dark. Both the United States and Russia deny any knowledge of why the group went offline.
Kaseya on Monday released a series of patches to fix the vulnerability that hackers had used to exploit its software.
Updated 7/22: This post was updated to include additional information.






