FBI seizes ALPHV leak website. Hours later, ransomware gang claims it ‘unseized’ it

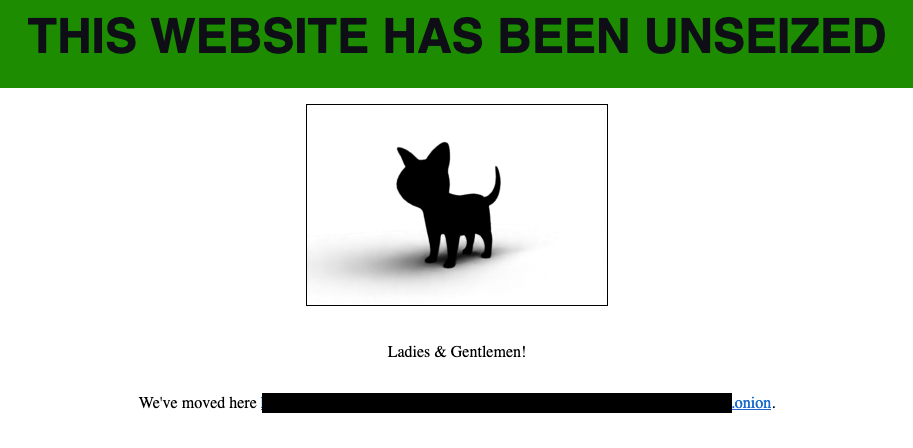
The FBI and an international consortium of law enforcement agencies claimed to have seized the main leak site from the notorious ransomware gang ALPHV, but hours later the gang claimed to have “unseized it,” while also lifting targeting rules for attacking critical infrastructure.
The ransomware gang is among the most prolific and has more than 1,000 victims, totaling hundreds of millions of dollars paid in ransoms. It has hit multiple industries, including critical services like health care and defense industrial base companies.
Also known as BlackCat, the Russian-speaking ransomware-as-a-service group first emerged in late 2021, and has been linked to other criminal gangs like DarkSide/Blackmatter and Revil. The Justice Department called the group the “second most prolific ransomware-as-a-service variant in the world.”
“In disrupting the BlackCat ransomware group, the Justice Department has once again hacked the hackers,” said Deputy Attorney General Lisa Monaco in a statement. “With a decryption tool provided by the FBI to hundreds of ransomware victims worldwide, businesses and schools were able to reopen, and health care and emergency services were able to come back online. We will continue to prioritize disruptions and place victims at the center of our strategy to dismantle the ecosystem fueling cybercrime.”
But just hours after the press release was sent, the ALPHV gang said it had “unseized” the website and was lifting targeting rules for critical infrastructure. However, experts are quick to note that the gang has previously targeted critical infrastructure, highlighting the tendency among these groups to lie or exaggerate.
“Because of their actions, we are introducing new rules, or rather, we are removing ALL rules, except one, you cannot touch the [Commonwealth of Independent States], you can now block hospitals, nuclear power plants, anything, anywhere,” according to a translation of the website that, hours before, showed the logos of law enforcement authorities around the world.
The gang did note that ransomware affiliates still cannot target countries that used to be a part of the Soviet Union, a common tactic for ransomware gangs looking to avoid penalty as long as they don’t target Russian interests.
It’s possible that the gang simply registered another server to link to the website, according to Allan Liska, a threat intelligence analyst with the cybersecurity firm Recorded Future.
“The way .onion addressing works is that, as long as you have the signing key, if you register a second server with that address the newest server will be believed by default,” Liska wrote on X.
“This reeks of desperation,” Alexander Leslie, a threat intelligence analyst at Recorded Future, said on X. “Ransomware groups, including ALPHV, have been routinely targeting critical infrastructure for quite a while. This isn’t new.”
The gang is thought to be based out of Russia and engages in stealing files before encrypting them to use as further leverage by threatening to leak sensitive data. ALPHV is a ransomware-as-a-service operator, meaning they lease out the ransomware program to affiliates for a portion of the extortion paid. One of the most well-known affiliates is Scattered Spider, or UNC3944, which allegedly hacked both MGM International and Caesars Entertainment in Las Vegas.
The seizure is at least the second time this year that authorities have thwarted one of the larger ransomware operators, following the January takedown of the notorious Hive ransomware gang’s infrastructure.
Just last week, ALPHV had difficulties with its website, causing speculation that law enforcement was behind it. However, the gang claimed it was due to “hardware failure.”
Now instead of a list of victims, ALPHV’s leak website now displays a splash page with the logos of law enforcement agencies from multiple countries, including Germany, Denmark, Australia, the United Kingdom, Spain, Switzerland, Austria as well as Europol.
“The FBI has also gained visibility into the Blackcat ransomware group’s computer network as part of the investigation and has seized several websites that the group operated,” the DOJ said.
The FBI claimed to have taken over multiple websites and developed a decryption tool for ALPHV’s victims that the agency is offering to more than 500 impacted victims, according to the press release. The FBI has since worked with “dozens of victims” to use the decryption tool, saving roughly $68 million in ransom payments, the DOJ said.
Charles Carmakal, chief technology officer at Mandiant Consulting at Google Cloud, called the seizure “a huge win for law enforcement and the community. ALPHV was one of the most active ransomware-as-a-service (RaaS) programs and they worked with both Russian affiliates and English-speaking western affiliates.
“Some of the ALPHV affiliates are still active however, including UNC3944 (Scattered Spider). We expect some affiliates will continue their intrusions as normal, but they will likely try to establish relationships with other RaaS programs for encryption, extortion, and victim shaming support,” he added.
The FBI gained access to ALPHV’s backend infrastructure through a “confidential human source” that accessed an online panel used to manage extortions, according to the search warrant.
The source — who “routinely provides reliable information related to ongoing cybercrime investigations” — gained access to the panel after answering an online advertisement for a ALPHV affiliate position and successfully applied.
Using this new access, the FBI collected 946 public/private key pairs for websites that ALPHV uses to host communication sites, leak sites and affiliate panels.
“The FBI has conducted extensive and outgoing outreach to victims,” the search warrant noted. “This outreach includes a decryption operation using a tool the FBI developed, which the FBI has offered to over 400 victims around the world.”