Sensitive medical, financial data exposed in extortion of Massachusetts hospital

A hospital in Massachusetts quietly paid off a ransomware gang after a February hack that exposed patients’ sensitive medical and financial data, the hospital said in a May 28 statement.
Sturdy Memorial Hospital, a 126-bed facility in the city of Attleboro, said that the information exposed in the hacking incident may have included insurance claim numbers, medical history, treatment information, Social Security numbers, bank routing numbers and credit card numbers and security codes, among other data.
“In exchange for a ransom payment, we obtained assurances that the information acquired would not be further distributed and that it had been destroyed,” Sturdy Memorial said.
The incident did not affect patient care or medical devices, hospital spokesperson Kathi Hague said in an email. Hague declined to disclose the size of the ransom, the type of ransomware involved or the number of patients affected by the incident.
“Though certain files on certain systems were encrypted, we were able to restore the affected files from our backup systems,” Hague said.
Other Massachusetts health providers with which Sturdy Memorial Hospital has worked were swept up in the incident. The breach affected data belonging to patients of Harbor Medical Associates, South Shore Medical Center and providers affiliated with South Shore Physician Hospital Organization, according to the statement.
Nearly four months after detecting the hackers — and a month after discovering the data that might have been exposed — Sturdy Memorial said it is notifying victims of the incident via mail. The hospital is offering breach victims free credit monitoring, a standard practice for hacked companies that consumer advocates say needs to be strengthened.
“For individuals whose financial account or credit card information may have been involved, we recommend that they review their financial statements for any unauthorized activity, and immediately report any such activity to their financial institution,” Sturdy Memorial said.
Massachusetts law requires businesses in the state to notify the Office of the Attorney General of security breaches, including those that expose personal data on state residents, “within a reasonable amount of time.”
Sturdy Memorial Hospital “notified our office [of the incident] and we are reviewing the notice for compliance as we do with all notices that we receive,” said a spokesperson for the Massachusetts attorney general’s office.
It’s only the latest in stream of ransomware incidents to affect hospitals around the world during the coronavirus pandemic. Ireland and New Zealand have in recent weeks dealt with ransomware attacks that have affected significant portions of those countries’ health care systems.
Conti, the type of ransomware involved in the Irish incident, has been involved in 16 ransomware hacks against U.S. health care and first-responder networks within the last year, according to the FBI.
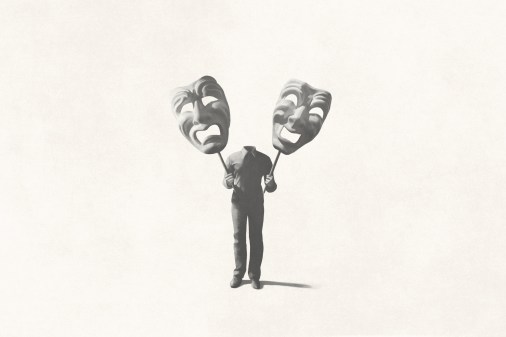
The hack of Sturdy Memorial is an example of how ransomware criminals have increasingly used a double-edged extortion tactic to pressure victims to pay, a technique that involves first stealing data from networks, then encrypting it.
UPDATED, 06/03/21, 11:32 a.m. EDT: This story has been updated with comment from a Sturdy Memorial Hospital spokesperson.