Nation-state actors are taking advantage of weak passwords to go after cloud customers, Google says
When it comes to attacking customers using cloud technology, nation-state and criminal hackers have something in common: They love targeting weak passwords.
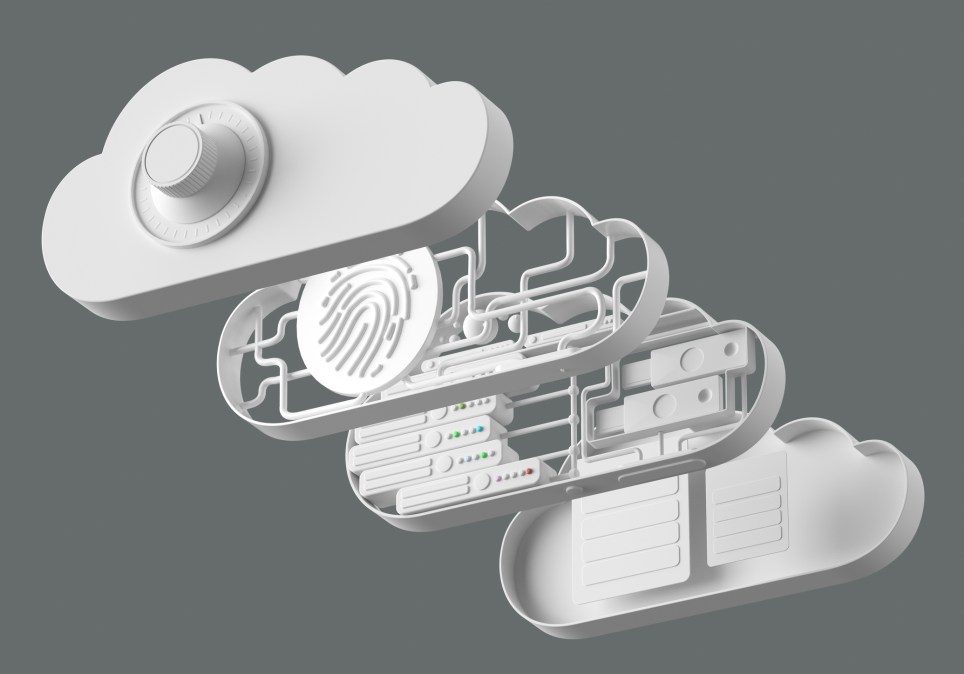
Weak passwords and other comprises of user identity continue to drive security incidents for Google Cloud customers, with weak passwords accounting for nearly half of the incidents affecting its clients, according to a report released by the company Thursday and first shared with CyberScoop.
Rather than targeting weaknesses in the underlying source code, attackers are increasingly exploiting the weak identity verification practices of their targets, said Chris Porter, head of threat intelligence for Google Cloud. “The percentage that’s a software issue or a zero-day, you know, it’s not zero, but it goes down and down and down. That’s a trend we generally expect to continue,” Porter said.
Compromises of APIs (application program interfaces), which allow bad actors to gain permissions within a company’s system, are another key avenue to attack cloud systems and were a factor in nearly one-fifth of all incidents reported.
Compromising weak passwords and unsecured APIs provide a gold mine for cybercriminals and nation-state actors alike, and nation-state actors appear to be mimicking cybercriminals’ tactics to infiltrate and stay in cloud environments without being detected.
“It is only prudent to consider that state-sponsored cyber threat actors may steal from the playbooks of cyber criminals to target such system,” Porter wrote in the report.
A range of actors are abusing Google’s infrastructure in carrying out attacks. For instance, in October a campaign by a Chinese government-backed actor known as APT41 targeted a Taiwanese media organization with phishing emails that linked to password-protected files in Google Drive. The malicious files contained a payload that received commands from Google Sheets.
Malicious actors have also turned to using Google Drive to store malware in encrypted ZIP files to obfuscate their efforts, suggesting that companies need to be ever vigilant about downloads, even those that appear to be from trusted sources.
“To me, the most important part of APT isn’t the ‘advanced’ it’s the ‘persistent,'” Porter said.
Intelligence officials have warned that nation-state actors have their sights on cloud environments, and the White House is pushing cloud providers to step up in their security offerings.
Ransomware attacks continue to be a challenge for companies using cloud-based products. Cloud-based victims are more likely to back up their data, but that’s just driven actors to use more aggressive techniques, such as threatening to leak sensitive data, Google researchers warn. Porter predicts that as more companies move to cloud services, a greater percentage of ransomware attacks will involve data leak extortion efforts.






