It’s easy to fake Extended Validation certificates, research shows

What does the happy green lock at the top of your browser mean? Maybe not what you think.
Extended Validation certificates — the files that tell your browser to show the lock — are supposed to make crystal clear who owns a website, in order to stymie cyberattacks and phishing. Instead, EV certificates are dangerously easy to fake, according to experts like U.S.-based researcher Ian Carroll.
The certificates are meant to prove legal ownership of HTTPS websites so that you are certain, for instance, that Google owns the website you’re visiting. Browsers like Chrome and Firefox show a green bar with the company name to signify security. The iOS version of Safari even replaces URLs entirely with the EV certificate.
The problem, Carroll explained in a recent blog post, is that it’s easy to incorporate under the same name as big-time companies and therefore imitate their EV certificate. Carroll did exactly that by incorporating as “Stripe, Inc” in Kentucky and imitating the multimillion-dollar payment processing firm “Stripe, Inc” incorporated in Delaware.
The result is that it ranges from difficult to impossible for users to tell the difference between the real deal and the fake.
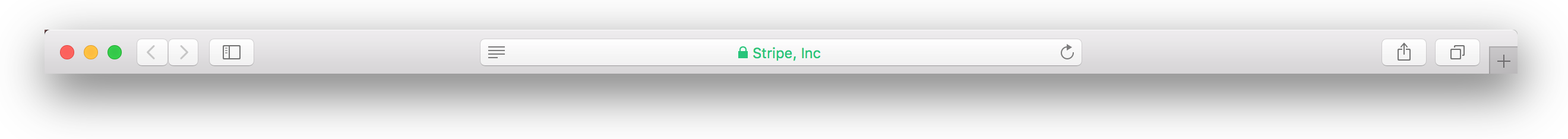
Researcher Ian Carroll imitating Stripe Inc as seen in the Safari browser.
https://twitter.com/iangcarroll/status/940281927789146112
Experts like Carroll expect to see hackers take advantage.
“There will undoubtedly be many proposed solutions to this issue,” Carroll wrote. “Ultimately, though, any method that ends up giving users a legal entity is fatally flawed.”
Because EV certificates stem from legal processes, any fix would ultimately have to be legal as well as technical in nature.
“As a result of how extended validation certificates work, browsers have few options to fix this,” Carroll argued. “Having said that, they can take steps to ensure EV certificates do not override other critical parts of the user interface, like Safari does.”
It’s not clear anyone is currently exploiting this weakness in the wild, but Carroll and other experts expect to see it in the future, especially in targeted phishing campaigns against browsers like the iOS version of Safari, which completely covers the URL bar with easily faked EV indicators.



