Gov email report is a mixed bag ahead of DMARC deadline

The number of federal agencies adopting a security standard that stops people from impersonating their email domains surged by more than a third just before the end of 2017, according to new research out Tuesday.
However, less than two weeks away from a Department of Homeland Security deadline, more than half of all agencies still don’t use Domain-based Message Authentication, Reporting and Conformance (DMARC), according to figures published by email security provider Agari.
The number of .gov domains with DMARC rose from 351 on Nov. 9 to 523 on Dec. 18. But that still represents only 47 percent of the 1,106 federal domains subject to the order.
Known as Binding Operational Directive 18-01, the order set a Jan. 15 deadline for agencies to adopt DMARC.
“DMARC has proven to be an effective solution to secure our federal domains, but more work is needed,” said Jeanette Manfra, assistant secretary for DHS’ Office of Cybersecurity and Communications, in a statement. “Deadlines are imminent. The time to act is now … It is crucial for U.S. citizens to trust that an email from a government agency is legitimate.”
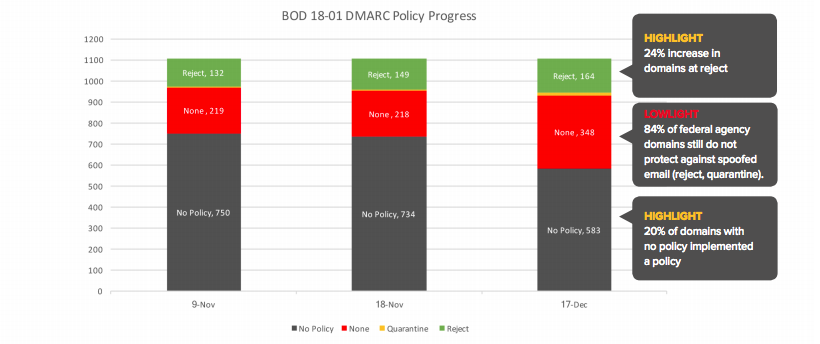
DMARC adoption by federal email domains (Agari)
DMARC is the industry standard measure to prevent email spoofing, which is a common way hackers get unsuspecting users to click on phishing emails.
“The increase in adoption is a smashing early success,” said Patrick Peterson, founder and executive chairman of Agari.
But even with DMARC deployed, the protocol has to be switched on to one of three levels. If both sender and receiver have the policy at “quarantine,” email attempting to spoof the sender’s address will be delivered to recipient’s spam folder. If DMARC is switched to its highest setting — “reject” — the spoofed mail will not be delivered at all.
But if DMARC is set to a policy of “none” — as it is with 348 of the 523 federal agencies that have it deployed — spoofed mail will be delivered as normal and the domain owner will be sent reports of any spoofing of their domain.
That’s important, because large organizations like government agencies often have multiple contractors or email servers sending from their domain and switching DMARC on without ensuring all those are authorized can result in service interruptions. For instance, marketing emails from a third party contractor may be categorized as spam or not delivered at all. Setting a policy of “none” allows IT staff to figure out which service providers are sending on behalf of the domain owners and make sure they’re authorized before the policy is set to “quarantine,” or “reject.”
The BOD gives agencies until Oct. 16 to set their DMARC policy at reject.
Despite the overall adoption rate remaining below half, Agari executives say there is good news in the numbers. Twenty-three federal agencies have achieved 100 percent DMARC adoption across all their email domains. This includes the Federal Trade Commission with 23 domains and the Consumer Product Safety Commission with 10.
Additionally, several large departments with dozens of email domains have nearly complete deployments, including the the Department of Health and Human Services (deployed in 107 of 121 domains) and the Department of the Interior (71 of 72 domains).






