German political party targeted by SVR-linked group in spearphishing campaign, Mandiant says

A hacking group linked to Russia’s Foreign Intelligence Service (SVR) known for targeting governments, embassies and diplomatic missions for political intelligence has expanded its targeting to German political parties, according to new research from Mandiant.
Mandiant, part of Google Cloud, said it discovered the campaign in late February, when the hackers — part of a subgroup of APT29, also known as Cozy Bear and Midnight Blizzard — sent spearphishing emails to victims that detailed a dinner invitation and used the logo of the Christian Democratic Union, a major center-right party in Germany. Those emails carried links to a compromised website that delivered a malicious dropper payload, dubbed ROOTSAW, which directed users to another lure document that could implant a backdoor via second-stage malware called WINELOADER.
Mandiant believes WINELOADER to be a variant of bespoke malware families that are unique to APT29. It has significant overlaps with other malware code associated with the SVR and was last seen in a previous operation in January targeting diplomatic organizations in Germany, Italy, Czechia, Latvia, India and Peru.
Mandiant said this is the first time they have witnessed this specific cluster of APT29 expanding its remit to target political parties, and given the group’s historical interest in espionage and obtaining political intelligence on Western policymakers, could present a broader threat to other parties in Germany, Europe and the West as well as their downstream technology providers.
“There is no reason to believe this activity is limited to any single party or country,” John Hultquist, chief analyst at Mandiant Intelligence and Google Cloud, said in a statement.
In an email to CyberScoop, a CDU spokesperson said the party “has already faced digital attacks from both domestic and foreign actors in the past. In this case, too, we received very prompt information about the attack, which we are constantly following up. In cooperation with the relevant authorities, we are working continuously to keep our systems resilient to digital threats and attacks. There was no official CDU dinner on March 1, the event was fictitious.”
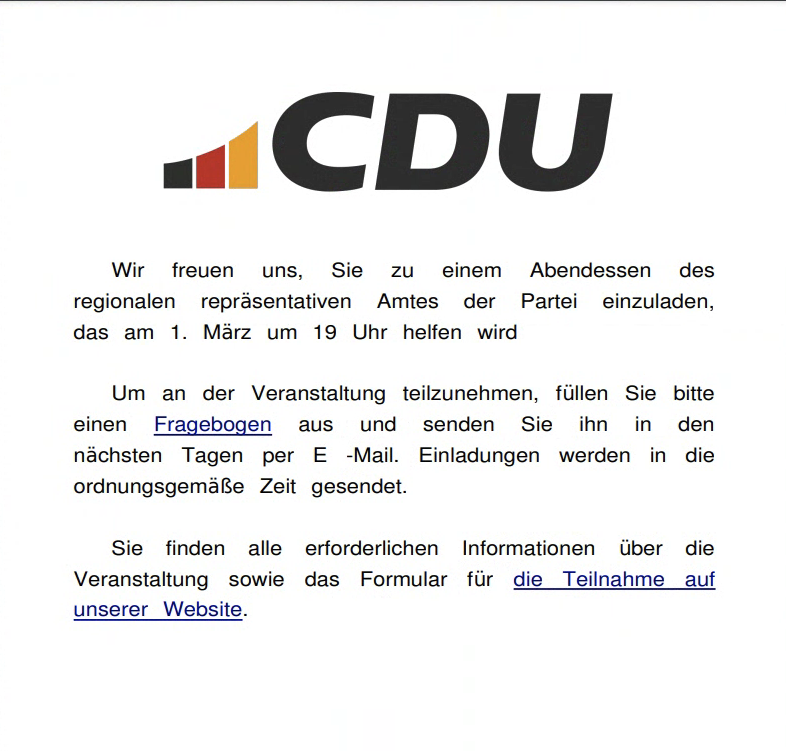
Mandiant-provided image of the lure document redirecting victims to an APT29-controlled and compromised WordPress website hosting ROOTSAW.
The SVR and Cozy Bear are also believed to have been behind the 2020 hack of SolarWinds, an IT management software company whose product was deeply embedded in U.S. federal agencies and commercial industry. That operation, which compromised the build environment for a legitimate software update sent out to 18,000 SolarWinds customers, resulted in the widespread compromise of at least nine federal agencies and 100 companies, including FireEye, the company that was home to Mandiant’s threat intelligence work until it split off and was purchased by Google in 2022.
Mandiant suspects the operation targeting the CDU is part of a larger push by Russian intelligence to glean insights into shifting Western policymaking and sentiments, particularly around issues like the war in Ukraine, where Germany and other European countries have been staunch supporters and financial backers of Kyiv, sending tens of billions of dollars in weapons, ammunition, and other funding to the beleaguered country as it seeks to fend off Russian troops.
But there are signs that European support could be waning as the war enters its third year, and as gas prices and other essential costs have risen as a result of the conflict, far-right parties less sympathetic to the Ukrainian cause have been ascendant in elections and polling across the continent.
“Outside of Ukraine, there is no bigger priority for Russia’s intelligence services right now than monitoring changing Western political dynamics,” said Dan Black, a principal analyst at Mandiant. “This latest targeting is not just about going after the CDU or Germany; it is part of Russia’s wider effort aimed at finding ways to undermine European support for Ukraine.”
Black told CyberScoop in an email Friday that Mandiant independently identified the campaign as part of its regular monitoring of SVR operations, whereupon they moved to notify the CDU. The lure was designed to ensnare not only members of the CDU, but also other parties that may interact with them, including other political parties. Black declined to answer whether Mandiant observed any victims clicking on the malicious links.
In addition to compromising political parties for policymaking insights, Cozy Bear may also try to use their access to infect downstream cloud providers and their customers. According to an advisory from the UK’s National Cyber Security Centre in February, the SVR was observed using password spraying, brute forcing and cloud-based authentication tokens in attempts to gain access to service accounts for victim cloud environments, where they can register their own devices and burrow in for further operations.






