Hackers use fake contact tracing apps in attempt to install banking malware on Android phones

Twelve applications posing as coronavirus contact tracing apps available outside mainstream marketplaces are designed to steal personal and financial information from unwitting Android users.
Apps meant to impersonate official government tracing apps from countries including Italy, Russia and Singapore trigger malicious software capable of collecting a range of data from user’s devices, the threat intelligence firm Anomali found in research shared with CyberScoop prior to its publication. It’s the latest example of hackers and scammers exploiting global events to try stealing from anxious smartphone users who, in this case, would have believed they were downloading an app designed to measure the prevalence of COVID-19 in their community.
None of the apps were included in the Google Play Store at press time. Anomali determined that apps were available on suspicious websites and in third-party app markets. Researchers were unable to determine how many people downloaded the suspicious apps, and the distinct programs do not seem to be part of a coordinated operation.
Scammers previously have deployed mobile contact tracing apps meant to pose as the U.K.’s National Health Service, while the U.S. Federal Trade Commission and security researchers have warned about the inherent fraud opportunities in contact tracing. Attackers have seized on coronavirus to launch phishing attacks and a broad array of other attacks.
In this case, four of the 12 apps called upon either the Anubis banking malware, which can record phone calls and keystrokes, or the SpyNote trojan, a hacking tool that accesses text messages, contacts and GPS location details. The other eight apps directed to more generic malware strains.
Once users download the Arrogya Setu app, which appears to be an Indian government app, they inadvertently infect themselves with the Spynote hacking tool. The malware functions similarly to a range of remote access trojans, in that it’s capable of viewing other apps installed on a user’s phone, accessing their messages and sneak data out of an infected device.
The app is so pernicious because of the potential for abuse. The legitimate version of the app has been downloaded more than 100 million times, India’s information technology mistry told the BBC in May, and it’s mandatory for Indian government employees to use the program.
The goal of the real Aarogya Setu app is to notify users when they are near a person who has contracted COVID-19. It then quantifies the users’ risk of infection, and encourages them to follow specific recommendations to avoid spreading the illness further.
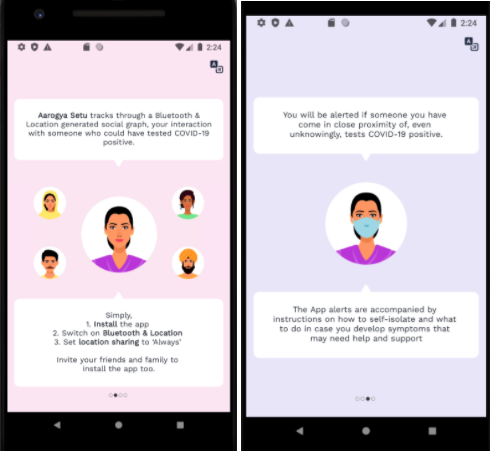
Screenshots of the malicious version of the app show careful craftsmanship (Anomali).
Meanwhile, when users download the app masquerading as the Brazilian government’s program, for instance, it triggers the download of the Anubis malware. Scammers have deployed Anubis in various forms since 2017, often in Android apps or as malicious software updates. Instead of providing users with updates about which of their friends and neighbors might have contracted the coronavirus, the app enables attackers to covertly steals data such as usernames and passwords to other applications.
The malicious app appears to be hosted on a website advertised as a cryptocurrency exchange, researchers said.
Other apps targeted Armenia, Columbia, Indonesia, Iran, Kyrgyzstan and the Indian state of Chhattisgarh.






