Conficker worm still spreading despite being nearly 10 years old
Nearly a decade after it first burst across the world, the Conficker worm remains one of the internet’s most prevalent malware threats, according to research by the security firm Trend Micro.
Conficker, also known as Downad, was first spotted in 2008 when it infected as many as 15 million machines. Experts saw it as one of the worst and most sophisticated cybersecurity crises to date.
The malware rapidly propagates across networks via network shares, removable media or software vulnerabilities. European businesses and governments quickly lost millions due to disruptions.
By technological standards, Conficker’s initial attack phase occurred a long time ago. This year, however, saw 2,564,618 successful infections. The pattern is clear: Anyone using old, unpatched machines remain vulnerable and are hit with abandon.
“Although it is not as exciting to the public eye as more modern malware such as WannaCry and Petya, it remains a persistent threat – and will continue to be as long as unsupported, unpatched legacy systems are still a regular part of an organization’s network,” Trend Micro researchers wrote.
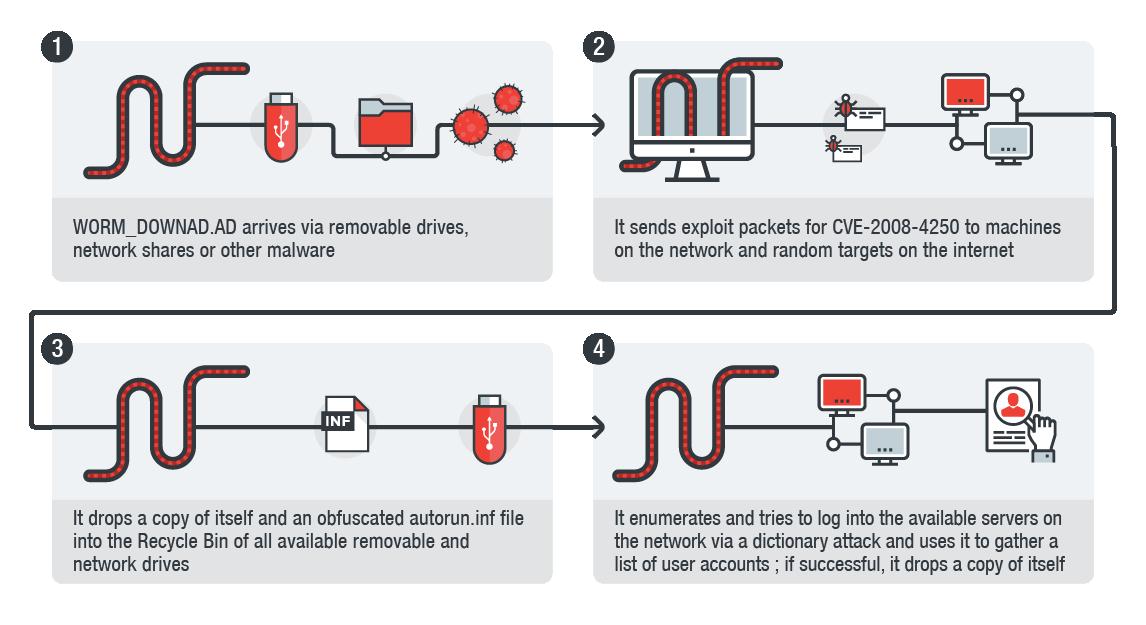
The Downad and Conficker infection chain (Credit: Trend Micro)
Conficker does not destroy or steal data, it simply infects a system and tries to spread to as many systems as possible.
“This particular malware was first created at a time in history when threat actors were more interested in infecting as many systems as possible, mainly for the notoriety among their peers that they successfully infected millions of computers worldwide,” said Jon Clay, director of global threat communications from Trend Micro. “This is very different from today’s malware which is mainly created for revenue generation.”
Tallying over 1 million total infections (41 percent of the year’s total), the health care industry was particularly hard hit by Conficker in 2017. Government and manufacturing also suffered significant successful attacks.
“Health care has to manage many legacy systems and devices which could be open to attack by the Conficker worm,” said Clay. ” Many times these systems are not able to support a security agent or are patched regularly so they tend to be more susceptible to infection.”
Countries most affected by Conficker include India, China and Brazil. These nations have large manufacturing industries that, in many cases, use old products that remain vulnerable to Conficker.
The malware remains highly effective and infectious even as it gets reaches ancient status in malware-years. Its highly capable creators and opaque purpose remain largely unknown.
“Conficker is not meant for any profit,” Clay said. “It is a worm and its purpose is to infect as many systems as possible. There is no data stealing component associated with it and no destructive payload. Simply put, when it was first created it was meant to infect as many systems as possible and today, nothing has changed, it still tries to do the same.”
In 2009, Microsoft offered a $250,000 reward for information leading to the arrest and conviction of the Conficker creators. It was never claimed.





