More vulnerabilities in industrial systems raise fresh concerns about critical infrastructure hacks

A slew of new reports about vulnerabilities in operational technology systems are raising fresh concerns about potential weaknesses inside U.S. critical infrastructure organizations. In just the past few weeks, researchers revealed flaws that in some cases could let hackers bypass security systems or give them remote access to equipment that runs manufacturing facilities and energy companies.
The reports provide a startling view of some long-known risks inside industrial systems that are receiving fresh attention after such high-profile cyberattacks as the Colonial Pipeline and JBS meat packing ransomware incidents. That increased attention means that both researchers trying to defend critical systems — along with malicious hackers looking to infiltrate them — are more focused than ever on industrial systems.
“We’re seeing capabilities out there that could have destructive capabilities, safety impacts: think Triton and Trisis, and think Pipedream,” said Puesh Kumar, director of the Cybersecurity, Energy Security, and Emergency Response at the Energy Department.
The types of malicious software that Kumar mentioned during a keynote at the S4 industrial control system security conference, which was held last week in Miami, are among the most potent types of malware designed to infiltrate critical infrastructure. Pipedream is a malware toolset likely designed specifically to cause disruptive or destructive attacks. Triton, which is also known as Trisis, targeted a Saudi Arabia petrochemical plant in 2017 and was dubbed among the most dangerous at the time.
Other research presented during S4, or released leading up to the annual conference, revealed an equally troubling picture of the evolution of critical infrastructure threats.
In fact, cybersecurity firm SynSaber pointed out that the number of industrial control systems vulnerability advisories released by the Cybersecurity and Infrastructure Security Agency has jumped from 550 in 2020 to 1342 in 2022, a 144% increase in just two years. The jump highlights the increased focus from both equipment manufacturers who are increasingly scrutinizing their own products and security vendors putting more resources into finding vulnerabilities.
Ahead of the S4 conference, the cybersecurity firm Forescout disclosed two potentially significant vulnerabilities in the widely used Schneider Electric Modicon programmable logic controllers, an industrial computer used in plants and utilities across critical infrastructure sectors. As part of its research, the firm released a proof-of-concept using those vulnerabilities to mimic how hackers could bypass safety logic built into low-level devices in critical infrastructure.
The first vulnerability is in the authentication mechanism for Schneider Electric Modicon PLC. Schneider previously released a patch for the authentication vulnerability, but Forescout researchers found that the fix did not address the issue. However, the existence of a software vulnerability in the authentication mechanism isn’t necessarily a bad thing. It means that vendors such as Schneider are adding new security measures such as authentication and “making steps towards getting some security baked in by default,” said Jos Wetzels, a security researcher at Forescout.
“While vendors in OT usually say, ‘Look, I don’t care. It’s a vulnerability, just put it behind the firewall because it’s all insecure anyway.’ Schneider actually went out and said ‘look, OK, there’s an authentication mechanism [that] should be good and we put out a patch,” Wetzels said. The second vulnerability would allow a hacker to execute code on the PLC.
Additionally, Forescout released a sophisticated proof-of-concept demonstrating how hackers with nation-state capabilities can move between the lower levels of OT networks. Typically, there is built-in safety logic that can ignore dangerous commands or it can be difficult to maneuver within the environments to get to a place where a hacker can control the motors and pumps. But Forescout demonstrated how hackers could infect a PLC and jump to lower-level PLCs and potentially ignore safety logic.
“For example, in automotive security where attackers have shown, ‘Look, I can take over the infotainment unit.’ But just from the infotainment unit I cannot control your brakes or your motor control unit,’ said Wetzels. “But they’ve shown that if I’m on the infotainment unit, I can maybe move to the gateway and from the gateway, I can move to the control units that actually control the brakes.”
Other devices commonly found in industrial facilities are vulnerable, as well. During S4, the cybersecurity firm OTORIO gave a talk on a new report outlining ways a hacker can get into the deepest portions of OT networks through wireless industrial internet of things vulnerabilities. The firm found 38 vulnerabilities in four leading vendors, some of which are still in the disclosure phase.
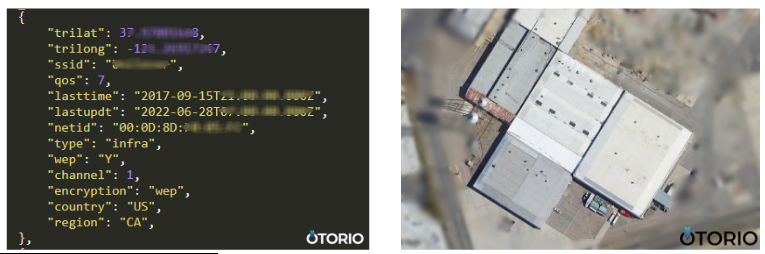
The firm revealed how a hacker can use a wireless network mapping platform such as WiGLE with specific search terms to physically identify a target’s location and potential vulnerabilities and exploit them. The platform collects information such as network names, encryption types and coordinates, from wireless access points including geolocation, which the researchers were able to use to locate industrial sites with lax security like default credentials.
“Usually, you’re going to have a gateway that is highly secured and responsible to make sure that all the operations are encrypted and cannot be hacked and things like that,” said Yair Attar, co-founder and CTO of OTORIO. “We identified different ways of basically hacking those types of devices under management consoles, that basically can help you to gain full control on the substation.”
In one case, the hackers could use WiGLE as a sort of wireless recon tool and drive up to the location and find the vulnerable devices to gain access to some of the most sensitive parts of OT networks. One example showed the physical location of a manufacturing company alongside the network name and crackable encryption algorithm.
OTORIO researchers also discovered major vulnerabilities in cloud management platforms allowing hackers to compromise “every cloud-manage device with high privileges, remotely and without authentication.”
“Most industrial wireless IoT vendors provide a cloud-based management platform, enabling the device operator to perform remote operations like configuration changes, firmware upgrades, rebooting, tunneling over the device, and more. By targeting a single vendor cloud-based management platform, a remote attacker may expose thousands of devices located on different networks and sectors,” the report noted.






