Trump signs long-awaited cybersecurity executive order
Updated 6:20 p.m.
President Trump signed an executive order on cybersecurity Thursday, saying his administration will begin to manage cyber-risk across the U.S. government as a whole, hold agency heads personally responsible for the protection of their networks and place modernization of federal IT at the heart of efforts to bolster computer security.
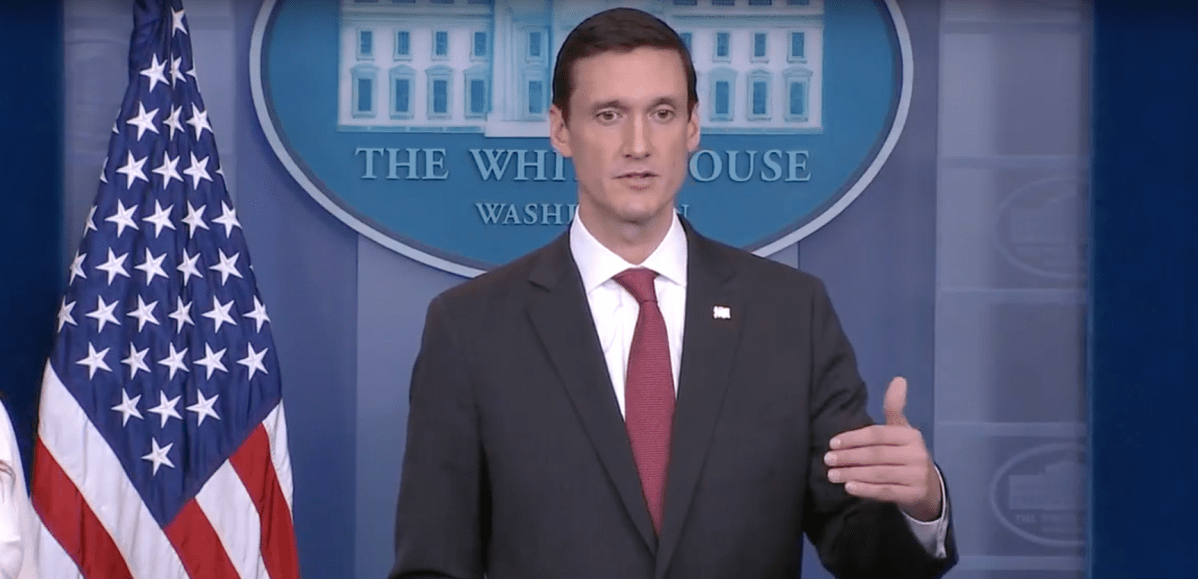
“We spend a lot of time and inordinate money protecting antiquated and outdated systems,” said Thomas Bossert, the president’s homeland security adviser, who made a surprise appearance at the podium during the daily White House press briefing to announce the signing.
The order is Trump’s first major action on cybersecurity and lays the groundwork for policy efforts to protect federal IT systems. Observers say it offers a great deal of continuity with and no sharp departures from, the policy of prior administrations.
The EO, which had originally been scheduled to be signed in January — only to be pulled the day of the planned signature — has been circulating in increasingly detailed draft form since then. But the signing Thursday came out of the blue on a day the White House continued to struggle with the fallout from the president’s shock decision to fire FBI Director James Comey.
More than a dozen major cybersecurity firms and tech companies that regularly engaged with the White House about the EO had no idea it was coming out Thursday, two people with knowledge of the feedback process told CyberScoop.
When asked about the lengthy delay, and the sudden scheduling of the signing, Bossert replied that the administration had faced criticism for rushing out policy — for instance on the president’s travel ban. “I think sometimes we’ve been criticized for doing things too quickly, and now maybe we’re being criticized for doing things too slowly, so maybe I’m right in the middle of that sweet spot,” he said.
Centralizing risk management
Bossert said that, in addition to modernization, at the center of the Trump administration’s strategy for securing federal networks was a determination to treat the entire federal government as a single enterprise and to centralize decision-making about security priorities. The order requires all departments and agencies to review the security of their IT systems using the risk management principle outlined by federal scientists at the National Institute of Standards and Technology in its much-admired Cybersecurity Framework.
The EO “centralizes risk,” Bossert said, “If we don’t do so, we will not be able to adequately understand what risk exists and how to mitigate it.”
“That mitigation process is going to have to come from a centralized place,” he added.
“Each department or agency has a responsibility to protect their own network,” he said, “but they also now have a responsibility to report that risk to the White House, to the president, so that we can look at what they’ve done” and decide whether additional measures to reduce risk are needed. The reports are funneled through the director of the Office of Management and Budget and the secretary of Homeland Security, and are due within 90 days.
Michael Daniel, who held the post of White House cybersecurity coordinator in the last administration, told CyberScoop there was a necessary tension between holding agency heads accountable for the protection of their networks, and making central decisions about what’s important to protect.
“It’s a healthy tension that you’re always going to have in a distributed enterprise like the federal government. I don’t expect that you would see the White House or OMB exercise that ability [to over-rule department heads on risk management decisions] very frequently,” Daniel said. “In fact I imagine that it would be very infrequent.”
Moving to shared services
As part of the push to centralization, the administration has also decided on what Bossert called “a preference for shared services” where multiple departments or agencies use the same IT infrastructure — like an email system or cybersecurity tools.
“We’ve got to move to the cloud and protect ourselves instead of fracturing our security posture,” he said. “If we don’t move to shared services, we have 190 agencies each trying to develop their own defenses against advanced [cyber] collection efforts, I don’t think that’s a wise approach,” he said.
Modernizing and moving to shared services, “is going to be a very difficult task,” acknowledged Bossert. Working alongside the American Technology Council — which the president established last week under the aegis of his son-in-law Jared Kushner — will take “a lot of hard, good governance,” Bossert said, adding, “We have great hope that there’ll be efficiencies there but also [more] security.”
John Bambenek, threat research manager at Fidelis Cybersecurity, pointed out that there were both upsides and downsides to centralized services.
“If cybersecurity can be managed centrally, then only one agency needs to hire the best and brightest and the entire federal government can benefit,” Bambenek said. “The risk with this is that it creates a single point of compromise for all of federal government. If I can get access to the shared IT infrastructure, I can then pivot to [hack into] any federal agency I choose.”
Protecting critical infrastructure
The order also calls for a review of what more government agencies should be doing to help the private sector owners and operators of the nations most vital industries — banking, communications and utilities like water and power. “He directed them to identify additional measures … in a proactive sense” that they could take, Bossert said.
“The message is a tilt towards action,” he said, summing up the EO.
Steve Grobman, CTO of venerable cybersecurity outfit McAfee, welcomed that way of looking at the issue.
“Directing policymakers to work collaboratively with critical infrastructure companies to understand what they need to better secure themselves is the correct approach. We support a model in which the government treats the private sector as a customer with the government acting as a service provider,” Grobman said in a statement.
The reaction from Capitol Hill and industry groups was also generally favorable. “We welcome this important step, and our members will continue working cooperatively with all parts of our government,” said U.S. Telecom, echoing pledges from the U.S. Chamber of Commerce and the American Banking Association.
“There are no surprises in terms of the content,” former George W. Bush-era DHS official James Norton told CyberScoop, “There’s been a lot of consultation.”
One thing that has not changed as a result of consultation is the presence of a section of the order calling for federal officials to convene a voluntary group of private sector communications providers to take action to divert or delete traffic from botnets.
Going too far? Or not far enough?
Some critics called out the EO for not going far enough, and slammed the decision to order more reports from agencies.
“While I appreciate the president’s interest in better understanding our capabilities and challenges in cyberspace,” said Senate Armed Services Chairman John McCain, R-Ariz., in a statement, “the fact is that the challenges we confront are well known and well documented.”
“We do not need more assessments, reports, and reviews,” McCain continued, “I hope the various reviews ordered today will be completed quickly and build on the many assessments required by the past two defense authorization bills so we can move on to the urgent business of formulating a strategy to deter, defend against, and respond to cyberattacks on our nation.”
Harley Geiger, director of public policy at cybersecurity company Rapid7, while “applauding” the EO, noted that it “does not directly touch on topics such as data breach, IoT cybersecurity, vulnerability disclosure, or unfilled critical appointments (such as a national CTO).”
“We hope to see further consideration on these topics in the future,” he concluded.
And Daniel Castro, vice president of the tech industry backed think tank, the Information Technology and Innovation Foundation (ITIF), said his organization was “disappointed to see that this executive order is mostly a plan for the government to make a plan, not the private sector-led, actionable agenda that the country actually needs to address its most pressing cyber threats.”
While the order “checks most of the boxes thematically,” Castro added, “it generally kicks the can down the road instead of taking any decisive actions.”
And the aggressively pro free-market ITIF also calls the EO out for over-reliance on government solutions. “Notably, this order leans heavily on the government for ideas and implementation rather than a public-private partnership approach. This is somewhat surprising given this administration’s belief that the private sector can generally do things better than government.”
Experts said the real test of the EO will be in the implementation. “Cybersecurity is kind of like dieting,” explained Brian NeSmith, co-founder and CEO of cybersecurity firm Arctic Wolf. “You can have the best plan in place, but if you don’t stick to it, you won’t see the results you want. The real test for this EO will be whether the government can actually implement and stick to a rigorous plan … Without that we’ll be reading more about Russian or other entities successfully infiltrating our nation’s defenses.”
You can watch Bossert’s briefing here:
Chris Bing contributed reporting to this article.






