Hacking crew targeting states over transition bans claims cyberattack hitting global satellite systems
A hacking crew with a history of blending politics and criminal activities claimed on Saturday to have “targeted various satellite receivers and industrial control systems around the country, particularly in states banning gender affirming care.”
SiegedSec, a group that emerged publicly on Telegram on April 3, 2022, claimed that part of its most recent attack included “a delicious supply chain attack,” which allowed the group to “control” multiple companies’ “accounts used for monitoring satellite receivers, VSATs, VOIP services, etc.” The companies include Halliburton, Shell, Helix Energy and Oceaneering, the group claimed.
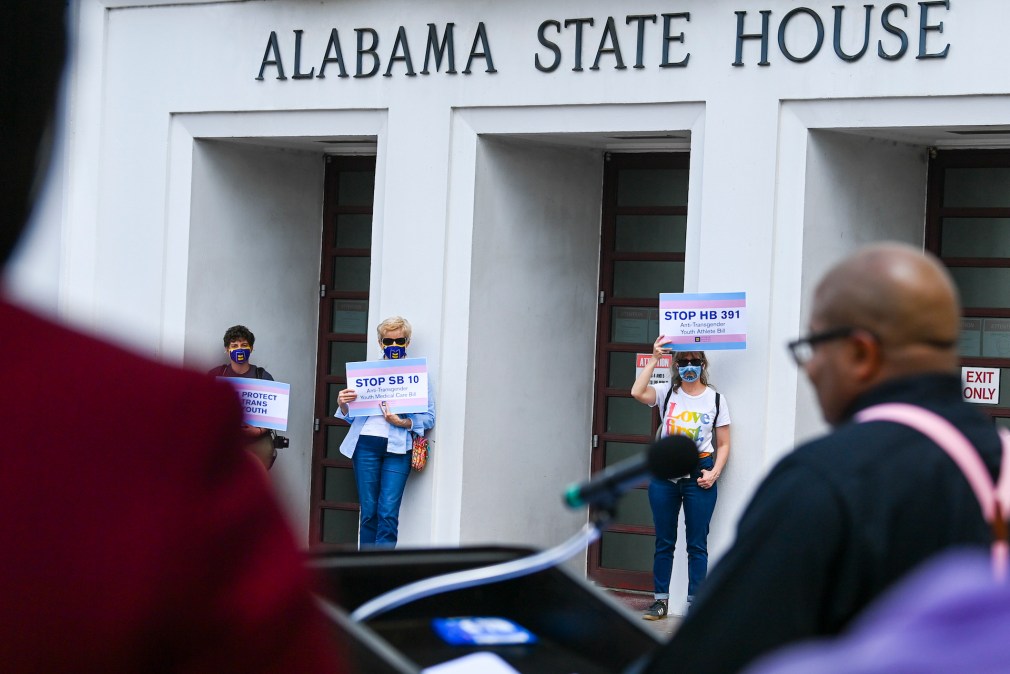
SiegedSec has claimed multiple attacks on organizations, corporations and states. Recently, it has taken aim at states where lawmakers have sought to ban or limit gender affirming care or ban and severely limit access to abortion. Last summer, for instance, the group — which describes its members as “gay furry hackers” — targeted state government agencies in Kentucky and Arkansas over those states’ changes to abortion access. The group has also targeted dozens of other companies around the world with more traditional hack and data theft operations.
The July 1 message also included links to download roughly 40 gigabytes of data stolen from the city of Fort Worth Transportation & Public Works. On June 28, SiegedSec posted what it said were roughly 500,000 files — roughly 180 gigabytes — that purportedly included work orders, employee lists, invoices, police reports, emails between City of Fort Worth employees, camera footage “and lots, lots, lots more~!”
SiegedSec seemingly hit multiple satellite receivers: the Trimble netR9 that often comes with security disabled by default or default credentials. An online manual says that the default user and password are “admin” and “password,” respectively. A cursory glance through Shodan.io, a database of publicly accessible IP addresses, shows around 1,374 that are online in the U.S. — although some are honeypots. Those receivers are often used for accurate positioning and not communications, says Ron Fabela, chief technology officer at cybersecurity firm Xona.
Some of those receivers could be used in offshore oil rigs. A screenshot that was among the documents SiegedSec posted to Telegram over the weekend showed a map with points located just off Texas’ Gulf Coast, which has a major concentration offshore oil and gas facilities. Additionally, Helix Energy provides services for the offshore energy industry.
Fabela said that so far any impact from possible SeigedSec activity appears to be limited to monitoring services, but he noted that offshore rigs have multiple positioning and telemetry methods. He noted that as SiegedSec appears only to have deleted the ITC Global portal accounts that might be the limit of their access with those networks.
Marlink Group, which owns ITC Global, could not be reached for comment. A spokesperson for Shell said the company is looking into the claims. Halliburton, Helix Energy and Oceaneering did not respond to a request for comment.
“We targeted a company that supplies satellite-related and other devices called ITC Global,” the group said in response to questions sent by CyberScoop on Monday to an email address announcing the hack. “We have more going on with ITC Global aside from just deleting accounts, however I can’t go into specifics.”
Last week, the group announced a pair of attacks, one on June 23 and one on June 28.
“We have decided to make a message towards the U.S government,” the June 23 message read. “Texas happens to be one of the largest states banning gender affirming care, and for that, we have made Texas our target. [F***] the government.”
The City of Fort Worth said in a June 24 statement that the data involved came from “an internal information system” known as Vueworks that facilitates work orders for the Transportation and Public Works and Property Management departments. There was no indication that any other systems were accessed, the city said.
A message posted to the group’s Telegram channel June 28 announced attacks on the Nebraska Supreme Court, the South Dakota Boards and Commissions website, the Texas State Behavioral Health Executive Council, the South Carolina Criminal Justice Information Services portal and the Pennsylvania Provider Self-Service website.
Agencies in each of the states were investigating the alleged hacks, the Record’s Jonathan Greig reported June 30. Texas, Nebraska and South Dakota have laws or policies banning gender affirming care, while South Carolina is considering a transition ban, according to the Human Rights Campaign.
The Pennsylvania attack gave the group access to more than 15,000 “child care records,” SiegedSec said, “however we will not be leaking any data due to… well its child care.”
“We did not intend to also target states that aren’t part of the push to ban gender affirming care, however one opportunity appeared with the Pennsylvania PSS hack, but that’s the only exclusion,” the email to CyberScoop read. “The targeted states were not opportunistic, we targeted them specifically for the gender affirming care issues.”
SiegedSec members “focus more on the message than the money,” the email read. “Although we mostly consider ourselves more blackhat than hacktivists. Money is not our main goal, most of the time we just want to have fun and destroy stuff.”






