New cybercrime group calling itself DarkBit attacks Israeli university

A previously unknown cybercrime group attacked an Israeli technical university over the weekend, demanding $1.7 million in bitcoin as payment for what the attackers claim are the Israeli government’s “lies and crimes” ranging from occupation to war crimes to tech layoffs.
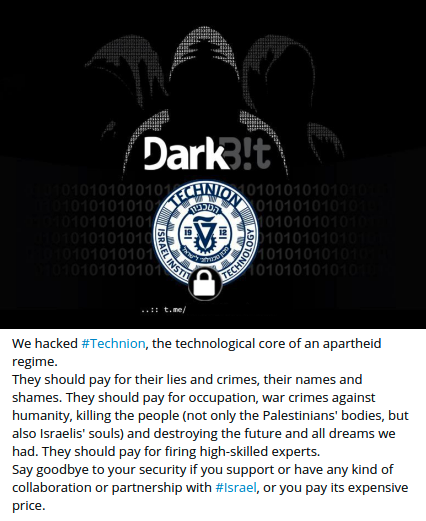
The Israel Institute of Technology, also called Technion, announced the attack on Twitter midday Sunday, and on Monday tweeted that the school remained “under a challenging cyber attack,” calling it a “complex event,” according to a Google translation. Around the same time, the online malware repository vx-underground posted a photo purporting to show the ransom note in which the group identified itself as “DarkBit” and demanded 80 Bitcoin.
The school said Monday services were slowly returning to normal, but its website remained inaccessible Monday morning U.S. time. The school said in one of its tweets that it had “proactively blocked all communication networks.”
DarkBit launched a Telegram channel on Saturday and claimed responsibility for the attack on the school, calling it “the technological core of an apartheid regime,” and threatening more attacks on entities affiliated with Israel. It’s not yet clear who is behind the group. The name could be seen as an amalgamation of older, established ransomware variants DarkSide and LockBit, and the demand of 80 Bitcoin follows an established ransomware pattern. But the ransom note seems designed to evoke the appearance of hacktivism, with the references to war crimes and occupation.
“While this attack had the characteristics of a ‘usual’ large scale ransomware attack (asking for 80btc to release the encrypted files), the way the group delivered their message and the overall political sentiment they used, and the threats, make us believe it’s ideologically driven and not a pure financial ransomware attack,” Messing said. “We expect them to continue to threaten the leakage of information, and also possibly act on the threat, in an attempt to embarrass the university and threaten its faculty, students and partners.”
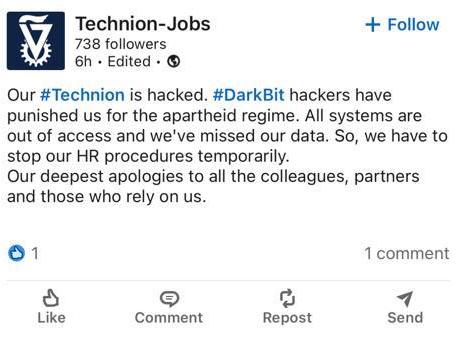
Gil Messing, spokesperson at Israeli cybersecurity company Check Point, told CyberScoop in a statement that the company believes DarkBit “are linked to a different ideological group with possible connections to Iran” based on a both technical and non-technical factors. Messing noted the creation of the Telegram channel the day before the attack, as well as hacking into and manipulating the school’s LinkedIn account:
Israel’s education sector is targeted roughly 3,400 times per week, compared to 1,600 per week for the overall national average, Messing noted, and universities there have been targeted by ideological hackers from Iran in the past.
“The university is a quality target for hackers and they are still in the process of understanding the scope of the attack, which servers are impacted and what data is encrypted,” he said. “This will take some time before the full picture becomes clearer.”
Updated Feb. 14, 2023: This story was updated to include comments and information from Check Point.






