Iran hacking group impersonates defense firms, hostage campaigners

An Iranian-sponsored cyberespionage unit is impersonating major brands like Boeing and the Chinese drone manufacturer DJI as part of a social engineering and phishing campaign targeting the aerospace, aviation and defense industries across the Middle East, researchers with Mandiant said late Tuesday.
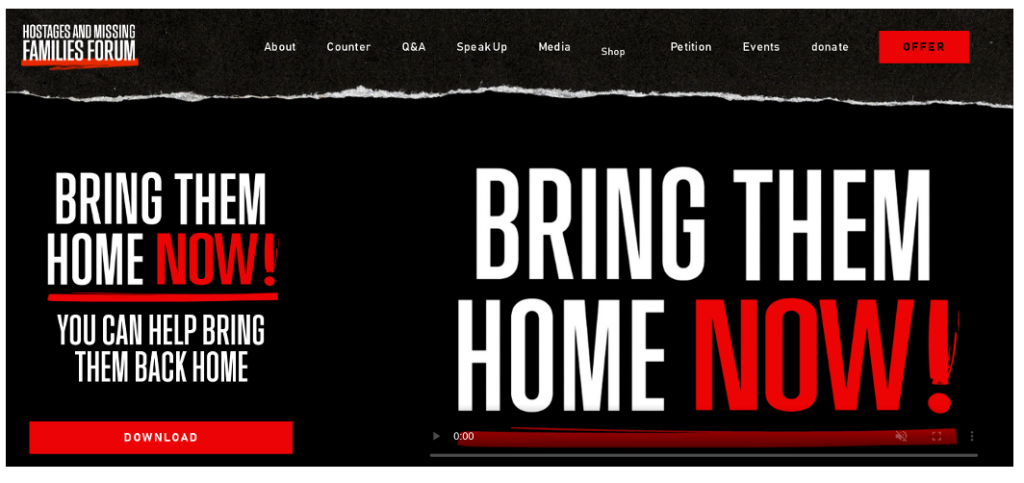
The Iranian hacking group has also been observed employing a fake website playing on the Israel-Hamas war, using the “Bring Them Home Now!” slogan associated with a campaign to free hostages held by Hamas. The website is the latest example of the way in which Iranian hacking groups are using the conflict between Israel and Hamas to carry out opportunistic attacks linked to the fighting.
The Iranian campaign relies on phony job offers from major international companies and the fake hostage-themed website to funnel targets to compromised websites designed to either harvest credentials or deliver one of two previously unreported and unique backdoors dubbed “MINIBUS” and “MINIBIKE,” the researchers said.
The current campaign dates to at least June 2022 and remains active. It has mostly targeted Israel, the United Arab Emirates and, potentially Turkey, India and Albania, the researchers said.
The unit behind the campaign is tracked as UNC1549 by Mandiant and the infrastructure described by Mandiant overlaps with the hacking groups dubbed Tortoiseshell and Imperial Kitten. The unit is likely linked to the Islamic Revolutionary Guard Corps and has a history of using fake job offers and similar lures in social engineering campaigns going back years.
In July 2021, for instance, Facebook announced the disruption of one of the group’s campaigns that used accounts on the social media platform to pose as recruiters to target U.S. military members. An October 2023 PwC analysis noted that the group is known to employ both custom and off-the-shelf malware to achieve its espionage goals, which includes credential harvesting and data exfiltration.
The current campaign uses Microsoft Azure cloud infrastructure for command and control and hosting functions, “making it difficult to discern the activity from legitimate network traffic,” the researchers said.






