Here’s how attackers are getting around phishing defenses
Hackers are evading natural language processing detection capabilities used to filter out phishing attacks by adding benign text and links, according to data from Egress’ threat intelligence unit released Tuesday.
Egress researchers looked at 40 attacks targeting U.S. organizations that used obfuscation techniques designed to evade anti-phishing services by using natural language processors (NLP) to send malware or malicious links. NLPs are also used by artificial intelligence models like ChatGPT.
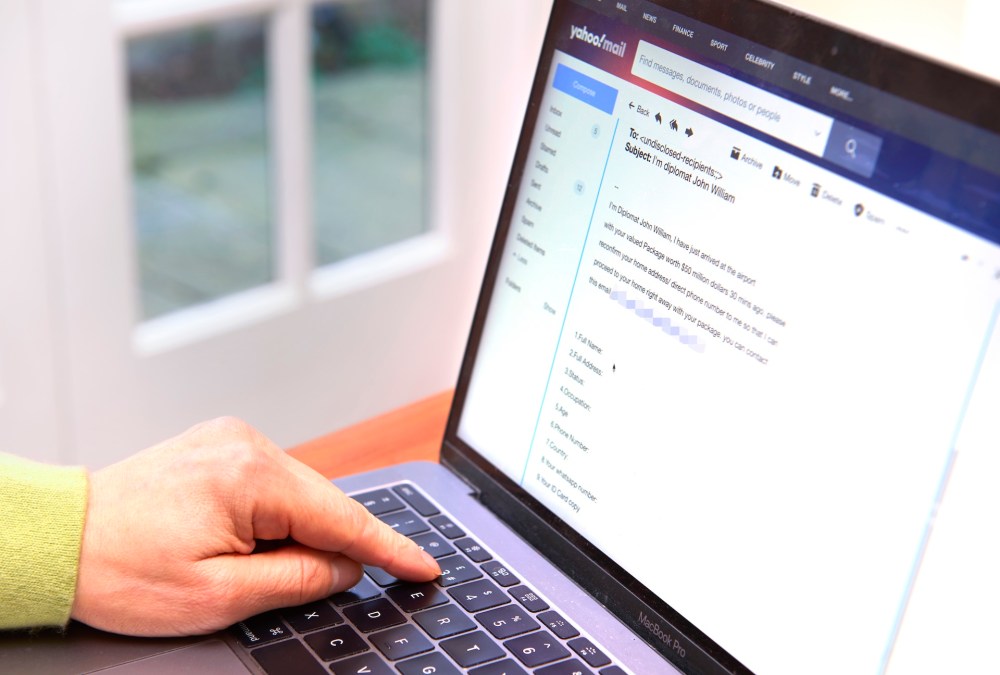
Egress, a KnowBe4-owned firm, said some email services use NLPs and make a calculation on whether an email is safe. Knowing these guardrails are in place, attackers are looking to manipulate NLPs with random text, links, or whitespace. If enough “safe” elements are detected, the email will be delivered to the victim, researchers wrote.
“It is the attackers’ hope that by stacking enough benign elements at the bottom of an email, an NLP tool will generate a general conclusion that the email is safer than it is malicious and deliver it to the recipient’s inbox,” Egress researchers wrote.
Dan Shiebler, head of machine learning at Abnormal Security, told CyberScoop that NLPs are among the oldest email protection techniques. NLPs look for words, phrases, or tokens that are rendered to the reader in a pattern that is likely to be spam, Shiebler said.
“The simplest thing you do is just look at certain phrases that are going to show up in attacks and not show up in safe stuff,” Shiebler said. “So if it’s like ‘Click here for penis enhancement’ … you’re going to see that in spam.”
But it has only been in recent years that processing power has been able to move beyond a couple of words or phrases at a time, Shiebler said. Now, statistical patterns are becoming more complex with recent advancements in artificial intelligence.
Egress’ report noted that while legitimate links to Bank of America and Uber were the most frequent sites used to evade NLP detection, random characters, breaks, and other links not included on email block lists were also found.
Egress also noted that attackers are aiming to give NLPs more data to process.
“For some email security tools, if an email takes too long to scan, it will be released before the scan is complete, so [a] phishing email can get through without [being] classified as malicious,” the report states.
Egress noted in a recent report on phishing that 78% of discovered malicious emails use two or more obfuscation techniques.
Verizon’s 2024 data breach investigations report found 31% of all detected incidents involved phishing tactics.