US cyber officials offer technical details associated with CL0P ransomware attacks
The U.S. government’s top cybersecurity agency and the FBI on Wednesday shared technical details associated with CL0P ransomware group after the group claimed responsibility for infiltrating a popular file sharing service, exposing companies globally to further attacks.
Hackers with the group exploited a previously undetected vulnerability in the MOVEit Transfer file transfer software, which the group said used to attack “hundreds of companies” as “part of exceptional exploit.” CL0P said this week it would give affected companies until June 14 to contact them and begin negotiating a price for their data. If a deal can’t be reached within three days, or the company does not get in touch, the group said it will publish the data.
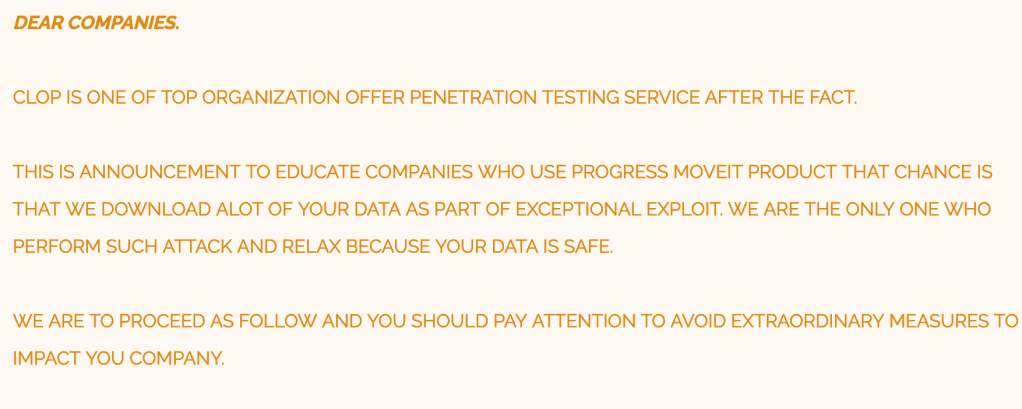
The CL0P ransomware variant evolved from CryptoMix ransomware, according to the FBI and the Cybersecurity and Infrastructure Security Agency’s Wednesday advisory. It started as a typical ransomware as a service platform — where a core group of developers lease access to the malware and other infrastructure to “affiliates” and split any profits — and was known for its double extortion method of stealing and encrypting data and then publishing that data on its leak website. The group is also known to sell access to compromised networks to others — known as an initial access broker — as well as operating a large botnet spcecializing in financial fraud and phishing attacks, the advisory said.
The group has been tied to compromises of more than 3,000 U.S. organizations and 8,000 worldwide, Wednesday’s advisory said. CL0P told Bleeping Computer that it was moving away from encryption and preferred data theft encryption, the news site reported Tuesday.
CL0P first emerged in 2015 and has been associated with deploying other group’s malware, but has in recent years been developing custom code, according to cybersecurity firm Secureworks. The group, which Secureworks tracks as GOLD TAHOE, attacked the Accellion File Transfer Appliance in a pair of attacks in December 2020 and January 2021, affecting a range of downstream targets including hospital records, universities, insurance firms and others.
“The majority of MOVEit Transfer servers are located in the U.S. and the Secureworks Counter Threat Unit is aware of victims in the U.S.,” said Rafe Pilling, director of threat research for the Secureworks CTU. Known victims include several British companies such as British Airways, Boots and the BBC, who all shared a payroll provider that was a victim of the MOVEit attack, Pilling added. “This is likely just the tip of the iceberg in terms of potential future data disclosures.”
Censys, a company that tracks internet-connected devices, reported June 2 seeing nearly 3,800 MOVEit Transfer hosts online across nearly a dozen countries, primarily the U.S., spanning industries including the financial sector, education, U.S. federal agencies and state governments.
“Although the exact version of the software cannot be determined with scans, it is highly improbable that all of these hosts have been patched against the newly discovered vulnerability,” the company said in a blog post.
More recently, in January 2023, CL0P targeted the GoAnywhere file transfer service, claiming more than 130 downstream victims in that attack, according to TechCrunch. In that case, the group sent ransom notes to executives, pressuring them to negotiate directly with the group or have their data leaked, Wednesday’s government advisory noted.
The earliest MOVEit exploitations were detected on May 27, resulting in the deployment of web shells and data theft, according to Google Cloud’s Mandiant, with data theft occurring “within minutes” in some cases. Another company, GreyNoise, reported scanning activity involving the login page for MOVEit Transfer and the particular file associated with this attack as far back as March 3.
On May 31, Progress Software Corporation, the company that owns MOVEit, posted its first notice of the situation and began posting patches. The vulnerability exploited by CL0P, CVE-2023-3462, affected all MOVEit Transfer versions, the company said.
“CISA remains in close contact with Progress Software and our partners at the FBI to understand prevalence within federal agencies and critical infrastructure,” CISA Executive Director for Cybersecurity Eric Goldstein said in a statement. “Today’s joint advisory provides timely steps that organizations can take to protect against and reduce the impact of CL0P ransomware or other ransomware threat. CISA continues to work diligently to notify vulnerable organizations, urge swift remediation, and offer technical support where applicable. Potentially impacted organizations should reach out to CISA via cisa.gov/report or your regional cybersecurity representative.”






