Can hackers really do that much damage to the election?
Even though the majority of states have turned to the Department of Homeland Security for help in protecting their election systems from hacks, cybersecurity experts are at odds to what portions of the country would be targeted for attacks.
Breached voter registration databases in Illinois and Arizona, reported earlier this year, is causing the public to become skeptical about election cybersecurity, according to a recent survey of 700 registered U.S. voters conducted by cybersecurity firm CarbonBlack. Republican presidential nominee Donald Trump added to the skepticism when he publicly stated on August 1 that if he does not win the race then that in itself may be indicative of a “rigged” election.
While both cybersecurity and policy experts say it’s unlikely that hackers will be able to significantly alter November’s election results by compromising voting machines, suspicions of tampering have become a cause for concern amongst state and federal officials.
More than 25 states have now turned to DHS for additional resources and expertise to help monitor and secure their individual election processes, Brett DeWitt, staff director of the House Homeland Security Committee, said Thursday. According to a source with knowledge of DHS’ election preparations, Pennsylvania is among those actively working with the agency.
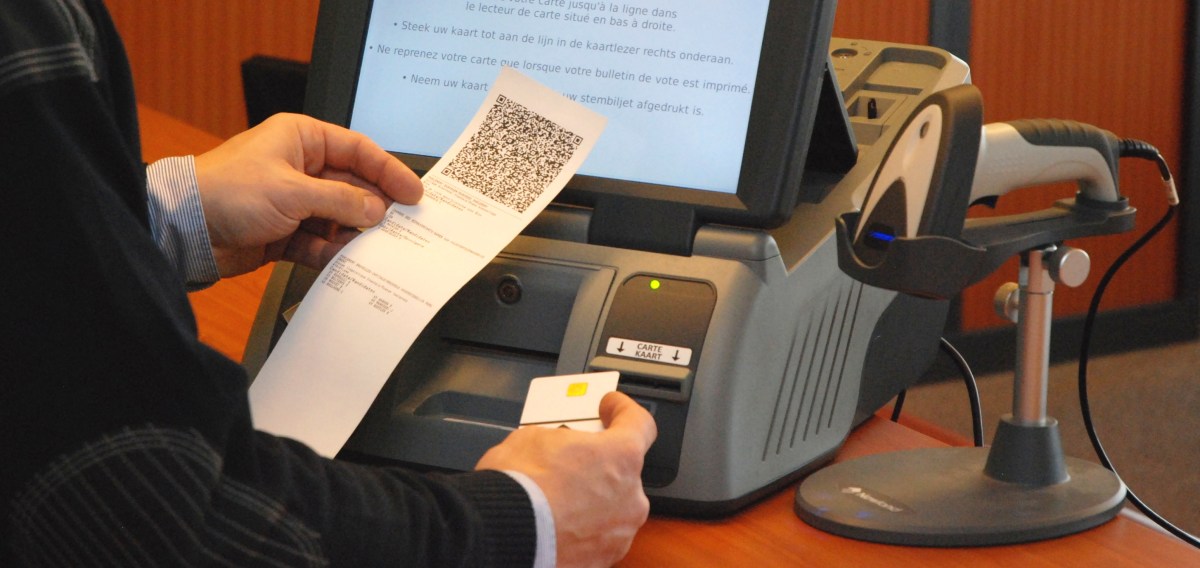
Municipalities that employ electronic voting machines without paper audit trails — including counties in swing states like Pennsylvania, Florida and Virginia — will likely be under the greatest scrutiny, according to Gregory Miller, co-founder of the OSET Institute, a Silicon Valley-based nonprofit think tank focused on election technology.
Pennsylvania is the most vulnerable state to election mischief because it lacks post-election audits and manual recount provisions, CarbonBlack’s report notes.
Notably, Pa.’s Secretary of State office recently distributed a guidance for county election administrators, providing advice to boost their digital security by offering basic cyber hygiene information.
“If I was a 400-pound hacker, I would target Pennsylvania,” wrote Ben Johnson, a former NSA engineer and the now co-founder of CarbonBlack.
Miller’s OSET Institute, which last week briefed lawmakers on Capitol Hill about the perceived threats to November’s election, pushed back against CarbonBlack’s report and Johnson’s comments.
“If one believes there are state actors seeking to alter an election result by exploiting voting machine vulnerabilities — despite the fact there are lower-cost higher-impact attack opportunities on U.S. elections in general, including some already underway — then Pennsylvania might be a more attractive target,” Miller said.
“[Pennsylvania] is no more vulnerable to cyber-focused attacks than any other state relying heavily, if not completely, on digital voting machinery, namely [direct-recording electronic] machines,” said John Sebes, CTO at the OSET Institute. ”Notwithstanding reports such as the CarbonBlack white paper, Pennsylvania’s voting machines share the same technical security vulnerabilities as in other states — no more and no less.”
Miller agreed, ”[Pennsylvania] is not more vulnerable but potentially more attractive insofar as attempts on voting machines.”
To be clear: voting machines themselves are not connected to the internet. And a diversity of different voting machines, sporting old technology, across the U.S. further insulates the larger system from influential digital attacks, FBI Director James Comey explained last month.
Andrew Appel, a professor at Princeton University, described to members of the House Oversight IT subcommittee last week that hacking into electronic voting machines is possible but sufficiently difficult and would require physical access to individual machines.
“My view is they don’t have to hack 50 states. In a close presidential election, they just need to hack one swing state. Or maybe one or two. Or maybe just a few counties in one swing state,” Rep. Ted Lieu, D-Calif., said during last week’s House Oversight IT Subcommittee hearing,
Miller and Sebes’ opinion echoes that of other experts; those who similarly fear attacks on the integrity of America’s voting process rather than on machines themselves.