The fixes needed to fight phishing

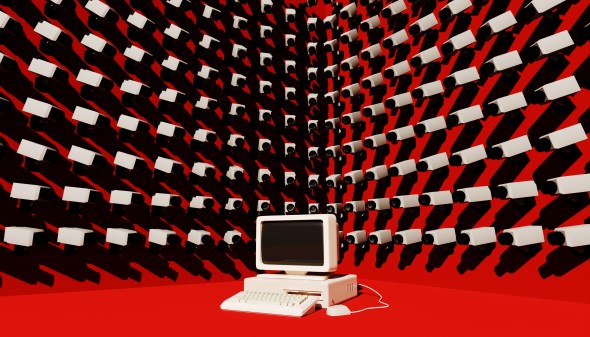
No amount of training, it seems, will stop computer-users clicking on malicious links or opening booby-trapped attachments in fake emails, so a technical solution is needed to defeat phishing — a tactic that still provides the baseline method of network penetration even for the most advanced hackers.
The good news is, there are solutions available. The bad news? None is a golden ticket to ending phishing on its own. But experts say much progress is being made all the same.
“The right answer is defense in depth,” Phil Reitinger told Cyberscoop.
A cyber veteran who has worked for Microsoft and the Department of Homeland Security, Retinger is president and CEO of the Global Cyber Alliance, an international non-profit founded by law enforcement and public sector organizations to tackle systemic security issues on the Internet. The group’s top technical priority is combating phishing messages.
By clever use of fraudulent web and email addresses, phishers fool users into entering their login and password details on a fake version of what appears to be a legitimate site. Criminals can then use those stolen credentials on the real site to drain a person’s bank account, clone their phone, install malware, or launch a host of other nefarious activities. The process is now highly automated and scalable and the cash it generates supports a significant proportion of the cybercriminal underworld, according to the Anti-Phishing Working Group.
In spear-phishing, the emails are individually crafted so they appear to come from a target’s colleagues or friends, and carry a piece of malware hidden in an attachment. By downloading such an attachment, the user’s machine — and subsequently, an organization’s network — can be compromised and brought under the hacker’s control.
As seen in a multitude of attacks from the OPM hack to the proliferation of ransomware, hackers can infiltrate an entire network from a single computer by using phishing as a baseline technique.
Training doesn’t work
Trying to train employees to suspect any message they get from a colleague can have hurtful effects on productivity and morale, according to research presented at the 2016 Black Hat security conference by Zinaida Benenson from the University of Erlangen-Nuremberg in Germany.
“People’s work effectiveness may decrease, as they will have to be suspicious of practically every message they receive. This may also seriously hamper social relationships within the organization,” she noted.
Reitinger countered, however, that “raising user awareness has has a variety of positive effects,” but acknowledged that ultimately it’s not a solution, except to the “low-hanging fruit” of commodity phishing — the easily detectable fake mails claiming to come from eBay or Apple that clog most user’s spam folders.
“There are different technical solutions to the different elements of this problem,” he said.
Containerization or sandboxing is one approach that works by isolating attachments and allowing users to preview or even print them without actually loading their full functionality — and allowing any exploits hidden in them to load as well, and take over the target’s computer.
Other approaches aim at stopping the forgery, or “spoofing,” of email addresses.
DMARC: The cure for spoofing
Because of the way email was designed as an open communications protocol, it’s possible to send email that looks to be coming from an address other than the one it was actually sent by.
Domain-based Message Authentication, Reporting and Conformance, or DMARC, is a protocol companies and other network owners can adopt to prevent spoofing of email addresses from their domain, explained Reitinger. But it’s proved slow to get it adopted, especially by small and medium-sized enterprises.
“The good news is that several large consumer email providers, like Microsoft and Gmail, have adopted DMARC,” said Craig Spiezle of the Online Trust Alliance, a nonprofit that audits online security for large consumer-facing enterprises.
Google, for instance, announced last week that it would start to warn Gmail users when mail came from unauthenticated domains or contained links to known phishing sites.
Together with other protocols, Spiezle said, DMARC protects consumers by filtering out spoofed email — either placing it in the spam folder or not delivering it at all.
Reitinger noted that there was often a lack of awareness about DMARC and said “ease of deployment” was an issue.
“We are developing an online wizard,” he said, that can walk any user through “a quick deployment of DMARC and give them feedback on how they are doing.”
He said the effort would “supplement and compliment” the work of OTA and commercial DMARC services.
“We are working to make DMARC a common best practice, at least for critical infrastructure,” he said.
Blocking malicious URLs
Another approach is to target and block the web pages used by phishers, which often rely on common misspellings of genuine domains — like “appple.com,” for instance. Other domains can quickly be identified as malicious.
Popular browsers all use some kind of blacklist or reputation engine that warns users if they are about to visit a malicious site, said Spiezle, but he added “That protects you against the known bad, but not the unknown bad.”
One solution being promoted by the Global Cyber Alliance, Reitinger said, is a change to the way the Domain Name System, or DNS, is run.
DNS servers, most of which are run by large communications providers, direct Internet traffic by translating the written URL for a website — like Fedscoop.com — into the numeric IP address that actually designates the computer hosting the site.
DNS Response Policy Zones are “a world class means of blocking malicious URLs,” said Reitinger. Essentially, the method allows DNS server owners to incorporate the latest threat intelligence about malicious domains into the software that runs their servers.
“It has an extremely low false positive rate,” Reitinger said, adding that it was “scalable and simple,” and that he hoped it would be widely adopted as soon as this year.
“We hope to have substantial results [on adoption] to report out in November,” he said.
No be-all, end-all
Even the most optimistic experts understand that the problem will persist.
“You can’t patch negligence,” said Spiezle. “The precision and complexity” especially of spear-phishing, makes it difficult to defeat.
“The social engineering that’s possible with just access to open-source social media intelligence is pretty hard to stop” even without spoofing, said Kevin Lancaster, CEO of Winvale, a government contractor that provides ID protection services.
Malicious actors can find out when senior executives are off base through their social media check-ins or activity, he said. “Then you don’t need to spoof their [email] address … ‘Hey, Bill. I’m off base and can’t get to my Outlook, so I’m sending this from my personal account.’ … And they download it and that’s it.”
“There are many solutions,” concluded Reitinger, but “The best solution is not to rely on just any one of them.”