How Russian hackers will impact the encryption debate on Capitol Hill

Could encryption have saved the Democratic National Committee from a cyberattack we now know was directed by Russian intelligence? Will public acknowledgement of Russia’s aggression actually move the needle in Congress, where politicians are preparing for yet another contentious battle over encryption that may spur regulation?
On Capitol Hill and around D.C.’s think tanks, both questions have been asked privately and some believe it will soon become a public talking point.
“The announcement that the Russian government is responsible for the hacks into American political organizations and election systems is one more reminder how foolish it would be to undermine strong encryption, which is the foundation of digital security,” Sen. Ron Wyden, D-Ore., told CyberScoop. “History has shown us that anytime you build a backdoor for the good guys, bad guys will exploit that security weakness. I’ll certainly be making that argument to my colleagues when Congress returns.”
The use of network intrusion techniques by foreign intelligence agencies’ is far from a revelatory story for America’s defense community. However, recent public statements made by leaders of the House and Senate intel committees, in addition to the Department of Homeland Security and Office of the Director of National Intelligence, is shining a conspicuous spotlight on Russia’s spying efforts against U.S. citizens.
“At a minimum, Russia’s alleged hacking increases the importance that Congress convene a commission to dig deeply and quickly into the use of technology by terrorists and nation-states to determine how we can protect America from bad actors while preserving our civil liberties,” said Matt Mayer, a visiting fellow who focuses on homeland security and counter terrorism policy at the American Enterprise Institute.
To formally attribute recent, high profile cyberattacks to the Kremlin serves to fully recognize that a highly skilled, well resourced actor is actively working to erode basic privacies enjoyed in the U.S., cybersecurity experts say.
“This announcement from the intelligence community should definitely spark a move on Capitol Hill away from discussions of encryption backdoors,” according to Ross Schulman, senior policy counsel at New America’s Open Technology Institute.
“Being faced with the plain evidence of another nation working concertedly to interfere with our political process should take efforts to reduce encryption protections completely off the table. It’s time to move on from this conversation and begin discussing what law enforcement can do to adapt to a future with pervasive encryption,” Schulman said.
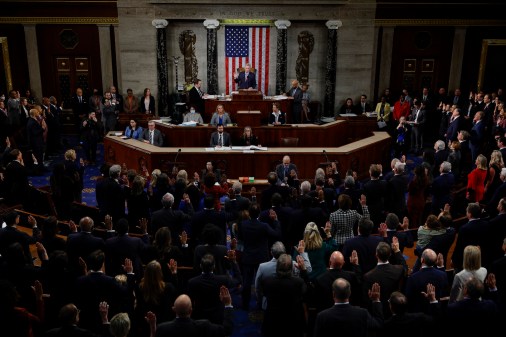
Today, makeshift congressional groups — all of which exist solely in legislative limbo without approval — have laid claim to overseeing future laws concerning encryption. This includes participation from members on the House Judiciary Committee, House Energy and Commerce Committee and a proposed bipartisan encryption working group led by Rep. Michael McCaul, R-Texas, and Sen. Mark Warner, D-Va.
In June, democratic presidential candidate Hillary Clinton endorsed McCaul and Warner’s proposed working group; announcing in a statement: “This commission will work with the technology and public safety communities to address the needs of law enforcement, protect the privacy and security of all Americans that use technology, assess how innovation might point to new policy approaches, and advance our larger national security and global competitiveness interests.”
Separately, a bill proposed by Sens. Richard Burr, R-N.C., and Dianne Feinstein, D-Calif., earlier this year — and then updated in September with new language — would require companies to provide “technical assistance” for investigators that seek access to encrypted customer data.
“The hack of the DNC raises many cybersecurity issues,” Warner told CyberScoop, “Russia and other cyber actors seem intent on gaining access to information of both government officials and private citizens who may have a connection to sensitive work.”
“While encryption is not a panacea and there is no evidence it would have prevented the DNC hack, it is one of a number of useful tools to protect data from states and state-sponsored cyber actors. Tools such as encryption certainly increase the level of effort required to gain access to data and therefore are invaluable for cybersecurity and national security purposes,” added Warner.
If the McCaul-Warner bipartisan encryption working group ultimately becomes a guiding force in drafting policy then it will similarly face the challenge of manning legitimate privacy concerns with law enforcement’s calls for increased access to private data so as to keep Americans safe.
Where that balance between privacy and enabling investigators falls in relation to eventual policy, however, remains entirely unclear.
“We have a lot of work to do to adjust cybersecurity policies to a much more hostile international environment, to figure out how to respond to cyber coercion, and to teach people how encryption actually works,” explained James Lewis, senior vice president at the Center for Strategic and International Studies.
Lewis worries that the administration’s decision to publicly attribute Russia will cause the discussion surrounding encryption to return to a debate about “strong” versus “weak” encryption.
“The intelligence community, big banks, and even IT companies use strong encryption that supports law enforcement access,” Lewis said, “it’s an issue of how much do you trust the oversight procedures we have in place for surveillance, whether people can buy products that defeat surveillance and what this means for public safety. Let’s not mischaracterize the debate as strong versus weak; it’s about access to data.”
Meanwhile, the FBI could be headed toward another encryption fight with Apple due to the capture of a locked iPhone owned by the man responsible for shooting people in a Minnesota mall.
“Dahir Adan’s iPhone is locked and we are in the process of assessing our legal and technical options to gain access to this device and the data it may contain,” FBI special agent Rich Thornton of the Bureau’s Minneapolis office told reporters Friday.