Cyber experts tell Congress that if companies can’t hack back, maybe the feds should
Corporate cybersecurity experts told senators that the U.S. government should launch offensive cyber-missions against hackers who attack and steal information from American companies.
During a Senate Homeland Security and Governmental Affairs hearing Wednesday, Chairman Ron Johnson, R-Wis., asked a panel of prominent private sector cybersecurity executives how the U.S. government could better collaborate with American companies to combat malicious digital activity.
The four-person panel, which consisted of individuals that work for Symantec, Monsanto, the Marine Corps University and a prominent U.S. law firm, unanimously agreed and told lawmakers that the U.S. government must do more to curb malicious cyber-activity. The follow-up question, however, of how exactly the country should advance such a broad effort, was met with widely different answers.
“I would say where the government can help corporate America most is to do the thing corporate America cannot do for itself,” said Kevin Keeney, director of cyber incident response for the Monsanto Company. “U.S. law does not allow for corporate America to strike back against an adversary that continues to bloody their nose and to do damage to their shareholders, which are likely American citizens.”
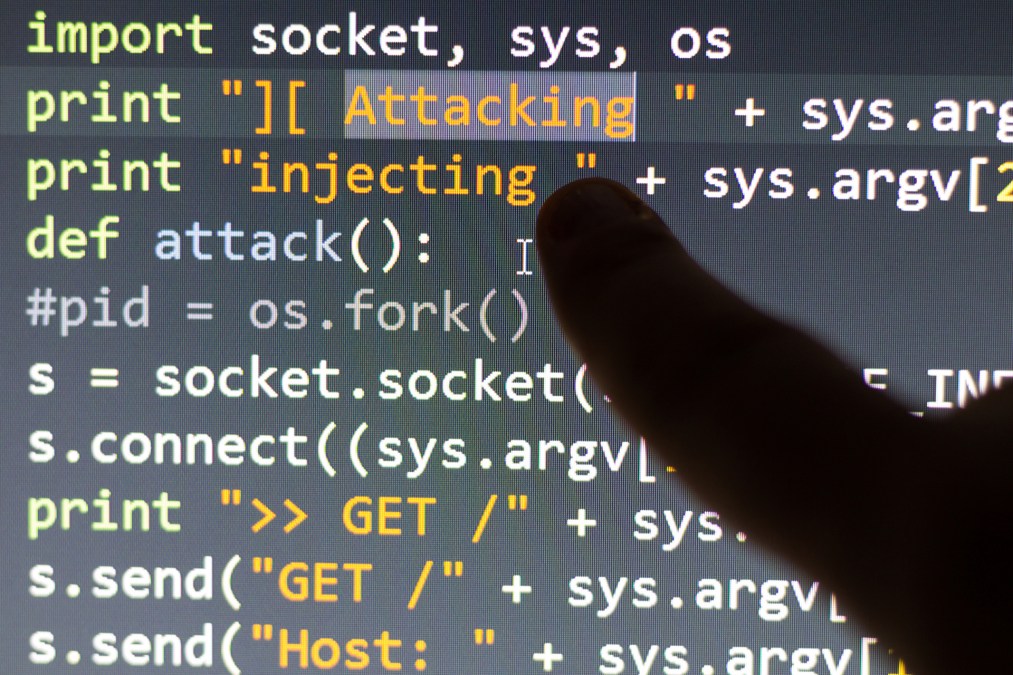
This “U.S. law,” mentioned by Keeney, which prohibits private companies from hacking back, is known as the Computer Fraud and Abuse Act, or CFAA. Under the CFAA, businesses are restricted from pursuing offensive cybersecurity measures as a response to a data breach. As it is currently written, cyber-defenders cannot infiltrate an attacker’s computer infrastructure to learn more about how a specific cyber-incident occurred or why it may have happened.
Keeney testified Tuesday in his own personal capacity, not as a representative of Monsanto.
“When the U.S. government does targeted offensive cyber-operations they are generally in response to traditional military operations. But I don’t hear much or see much about offensive operations being done as a counterpoint to someone crossing this redline of stealing intellectual property of a company valued at more than $1 billion,” Keeney said.
Keeney was not the only expert testifying Wednesday who appeared interested in a future where the U.S. government may in some cases seek revenge and act in cyberspace on behalf of victim companies.
“The headlines will show [the U.S. government] is much more confident with attribution, [but] what we are not yet confident with saying is what we’re going to do about it. And that’s where the government needs to come in,” said Steven Chabinsky, global chair of data, privacy and cybersecurity at law firm White & Case LLP.
Chabinsky explained in no uncertain terms that the existing relationship between the U.S. government and private sector when it comes to cybersecurity is largely ineffective and undoubtedly insufficient to combat increasingly capable criminals and intelligence organizations.
“There’s just no doubt that businesses cannot defend against the type of organized criminals and intelligence services we have today,” Chabinsky told lawmakers. “Until we realize that it is not the government’s role to help the private sector better protect itself by giving them guidelines and information about patches but to get out there and get rid of the threat, then we are really going to see this rise to unsustainable levels.”
While Chabinsky suggested that offensive cybersecurity measures may be one option in the U.S.’ larger toolbox, he also said that other capabilities — like diplomacy and judicial prosecution — may be helpful to discourage hackers from attacking valuable organizations.
Brandon Valeriano, a scholar at the Marine Corps University, was quick to distance himself from Keeney’s statement during the Senate hearing. He said that the U.S. would be wise to cautiously consider any strategy that heavily relies on hacking back.
“There’s a reason we haven’t seen much escalation in the cyber domain and that’s because everyone is vulnerable. Asking for more escalation, asking for responses, looking for conventional or even cyber-responses to cyber-violations is a dangerous step that we have not taken yet and that other nations have not taken yet and there’s a reason why,” said Dr. Brandon Valeriano, a scholar at the Marine Corps University.
He added, “What we’re asking for here is dangerous and that’s why we have instituted a set of norms that seem to have worked so far and what we’ve done to reply in terms of sanctions and diplomacy has generally kept the lid on cyber escalation so far but the worry is if we go further what will happen next.”






